

Chris Evans
3.5K posts

@scarybeasts
CISO and Chief Hacking Officer at HackerOne. Past: Founded {vsftpd, Chrome security, Google Project Zero}; Tesla; Dropbox. Hacker / Researcher. beebjit.




HackerOne has implemented crypto payments for non-coinbase USDC and BTC wallets🎉

That is a _lot_ of collaborations recently 👀



The massive Ambassador World Cup is starting again, with 700 hackers competing in 40 teams. Last year, one of our major customers said it was the best thing they ever did.

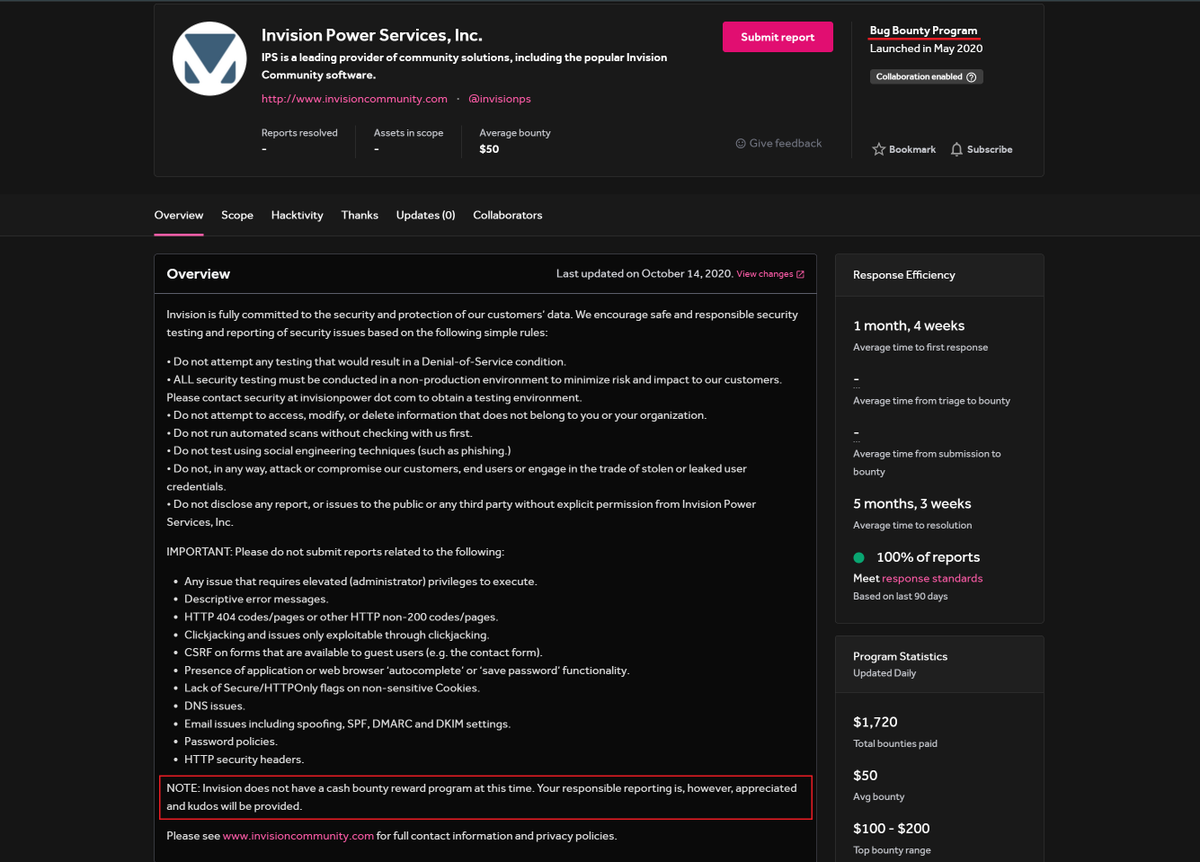
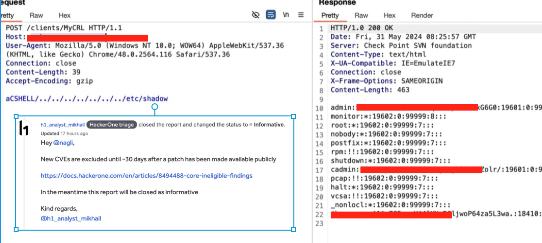
The new @Hacker0x01 policy around CVE reports is concerning, especially for High & Critical ones, as it potentially keeps hundreds of their customers vulnerable to critical ransomware-leading risks by withholding information as they are automatically being set as "Informative." A report that could have resulted in a $3,000-$15,000 bounty, based on the customer's assessment of its helpfulness, will very likely become a 6-7 digit Incident Response bill. I hope this policy will change soon, let's break down what happens today when you report a critical CVE to a Managed program: Up until a few weeks ago, programs could set in their policy that they do not accept CVE reports with a public advisory up to 30 days from disclosure. This was a reasonable decision for the program to make when it was harder to exploit, detect, and take down systems. As of the latest update, a site-wide ruling was enforced for the triage teams to not forward any incoming CVE to their customers if it is less than 30 days since disclosure, even if it is a critical LFI/RCE with one simple request, completely overriding the customer's policy that welcomes them. (docs.hackerone.com/en/articles/84…) Some serious questions arise from this policy: Timing: What constitutes a "reasonable period of time"? For example, with the latest Checkpoint LFI, the public exploitation POC came about 5 days after disclosure, make a drop down for customer to decide based on their own threat model? Validity: The policy states, "The following issues will be closed as invalid except in rare circumstances demonstrating clear security impact." Isn't unauth RCE/LFI enough? Rationale: Researchers will still report these issues, customers would appreciate the value from their bug bounty platform, and the platform would benefit from reporting it first to their customers rather than relying on other security tools. Communication: This may push researchers towards off-platform communications, bypassing triage processes. As a researcher and ethical hacker, I want to ensure the programs are aware of serious risks to their infrastructure. Obfuscation: Researchers might obfuscate their findings to bypass the policy, making it harder for clients to implement fixes. Bug Bounty Goals: One main goal of a Bug Bounty program is to report exploitable CVEs. This policy seems to contradict that. Double Policies: Program's own policy is not being taken seriously if site wide restrictions are over-riding them. Yesterday I was fortunate enough to experience three different outcomes when reporting the Checkpoint VPN CVE (a simple LFI that can lead to an easy RCE): 1. HackerOne Managed Program: Report to a program with a >$10B market value on their main VPN was directly closed as informative, not passed to the team, leaving the appliance vulnerable. HackerOne Managed Program: Report to a program with >$10B market value on 10 VPNs was picked up before triage after tagging the program manager, who is evaluating it and will probably pay for it as they take critical risks super serious. BugCrowd Report: Triager passed the issue to the team due to its criticality. The team acknowledged it was out of scope but decided to pay a courtesy award. This is not just a rant. I genuinely think this policy is a mistake and want to improve processes for everyone involved. This situation appears to be a loss for the platform, customers, and hackers. Potential Solutions: Highway Pass for Critical & High CVEs: Forward these reports to programs as "Pending Program Review," allowing the program to decide on the reward. Set a Reasonable Date: Accept reports "5-7 days" after publication. If a customer hasn't addressed a CVE within a week, additional delay is unlikely to help. Opt-in Policies: Allow programs to opt-in to strict rules rather than auto-enforcing them, ensuring critical information isn't hidden from customers. Again, the goal is to improve the experience for everyone involved in the #BugBounty space, we should definitely find those vulnerabilities and notify the customers over their legacy tools, allowing them to double-down and invest more on their programs. 🙏




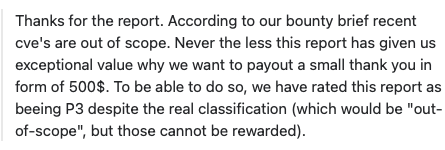



The spot check feature by @Hacker0x01 is really awesome. Submitted spot check report today at 8:25 pm and got rewarded $500 at 8.56 pm

Excited to introduce @Hacker0x01 Spot Checks! Now, customers can perform targeted testing on specific assets, and hackers have new ways to earn. Learn more: hackerone.com/vulnerability-…

