scriptjunkie (Matt)
6.9K posts

scriptjunkie (Matt)
@scriptjunkie1
Documentation is lies. Source is an abstraction. Assembly is the truth. Also at https://t.co/VYFZ0HHnQn and nostr npub10mx0gx3r2lszrrut8kvr5mt2m8r9ffhn


How much time do we expect Afonso Eulalio to lose on Jonas Vingegaard today? I'm optimistic and I say 2:55. #GirodItalia


Seven customer calls. Did two blogs, a video for customers, a customer email going out next week. Met with multiple SOC analysts on what they need from NightBeacon to make it better. Got those done and into prod. 23 merge requests. Fixed a connector issue with CrowdStrike. Closed three deals. Solid day.


What historical fact sounds fake but is true?


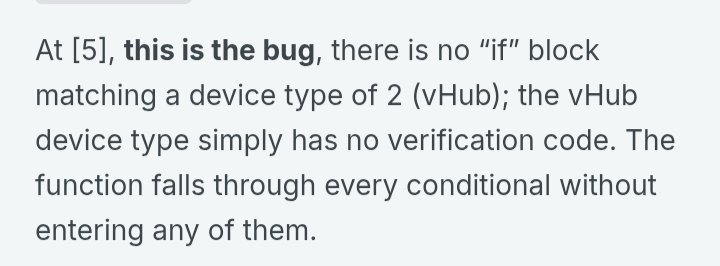
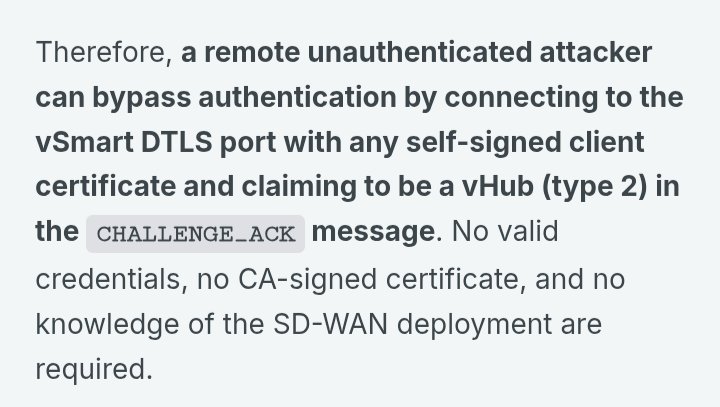
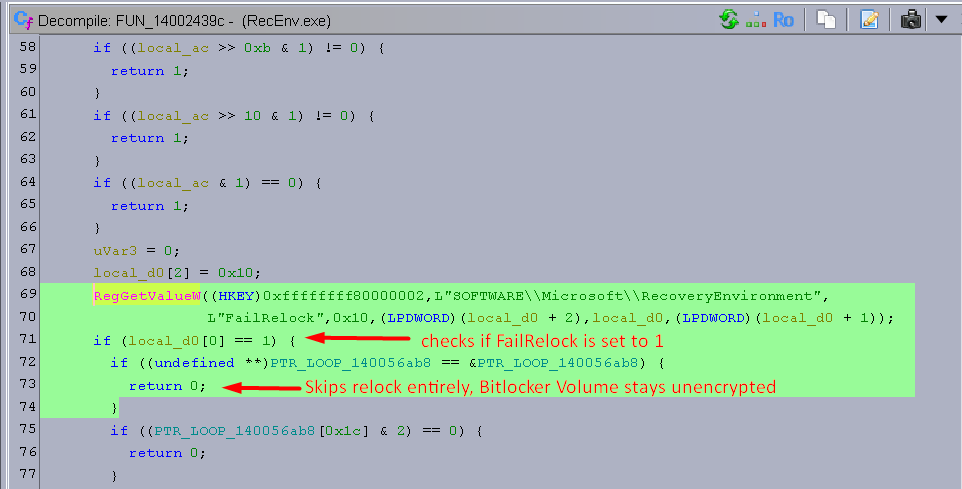
Today @rapid7 and Cisco are disclosing CVE-2026-20182, a critical (CVSS 10.0) auth bypass affecting Cisco Catalyst SD-WAN Controller, found by @_CryptoCat and I when we were researching CVE-2026-20127 last Feb. An unauth attacker can become the vmanage-admin and issue arbitrary NETCONF commands. Cisco has also disclosed that the new CVE is already EITW as of this month. Read our blog here with full technical details: rapid7.com/blog/post/ve-c…

“We are all smart enough to know to never have smoking guns…” “If we did we wouldn’t put them in emails, and if we found them we’d delete them.”


I'm seeing this question being asked a lot! I think the traditional 90+30 day responsible disclosure standard is dead (or should be). It's too dangerous to be holding onto vulns for this long now. I've been thinking about alternative responsible disclosure policies that work better for a post-AI era but it's a pretty tricky problem!

The userland demon is about to drop again.





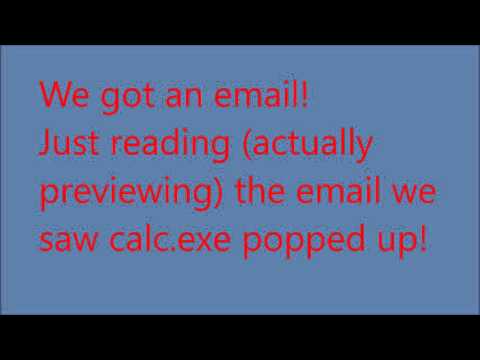
Two more zerodays - deadeclipse666.blogspot.com/2026/05/two-mo…




