
Sec3
1K posts


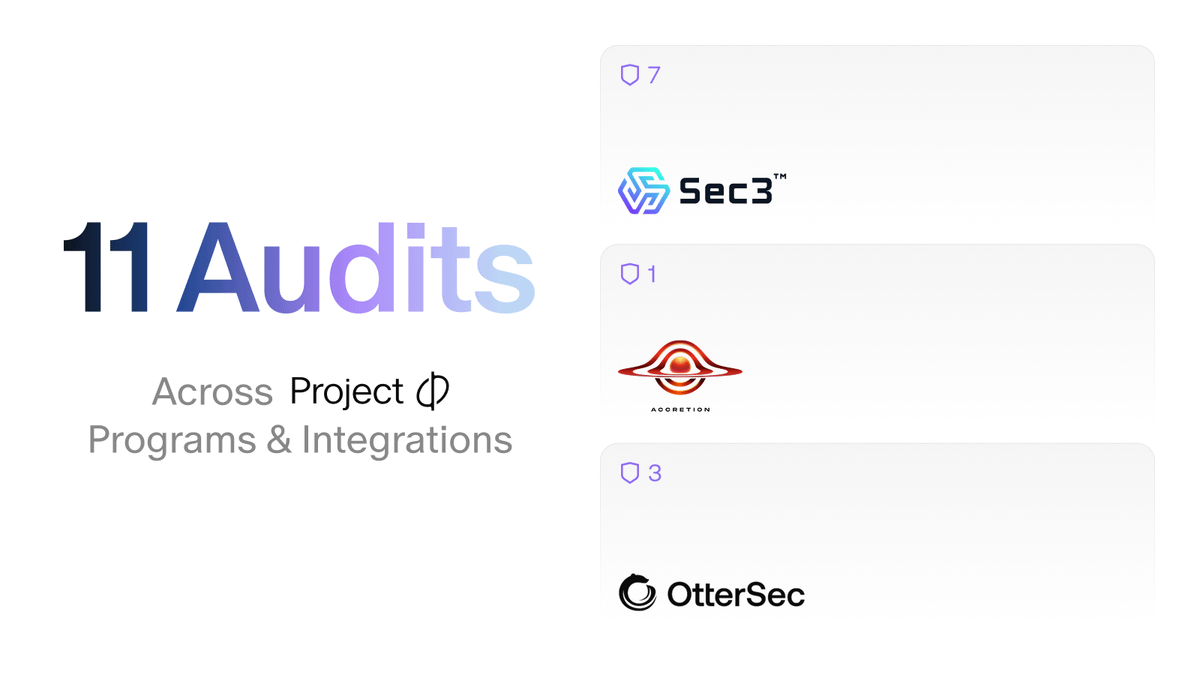
Sec3
@sec3dev
Full Stack Security: Protection at every step of the development cycle. Security Partner of @Metaplex, @Orca_so, @KaminoFinance, & many more!


0/ DeFi needs circuit breakers and other safety mechanisms which slow down large transactions and provide time for reaction. Borrow lend protocols should not allow a new user to show up with a $300M position and take out a loan against it immediately. Some ideas:












🐳 Thrilled to announce our ongoing security partnership with @orca_so! Together, we're ensuring Orca's Whirlpool and Wavebreak protocols remain secure and trustworthy for the community. Wavebreak is Orca's upcoming launchpad featuring an anti-bot mechanism to protect token launches from bots and snipers Huge thanks to Orca's dev team for their exceptional diligence and collaboration throughout this process. Let's dive deeper together! 🌊🔒





We’re excited to release IDL Guesser - an open-source CLI that rips the IDL out of any closed-source Anchor program ! Blog: sec3.dev/blog/idl-guess… Code: github.com/sec3-service/I… The Gap: about half of the top-100 Solana programs ship with no IDL. Can’t decode transactions, fuzzers stall, auditors waste hours reverse-engineering How it works: • Finds sol_log("Instruction: …") in the ELF • Walks Anchor’s try_accounts control-flow graph to map signers & mutables info Brute-probes arg sizes, recalculates 8-byte discriminators • Spits out ready-to-use JSON. Early testing shows the tool recovers the vast majority of instructions. The tool just won 1st prize at Reverse Engineering Closed Source Solana Programs hackathon hosted by Accretion. Try it now - github.com/sec3-service/I…


We’re excited to release IDL Guesser - an open-source CLI that rips the IDL out of any closed-source Anchor program ! Blog: sec3.dev/blog/idl-guess… Code: github.com/sec3-service/I… The Gap: about half of the top-100 Solana programs ship with no IDL. Can’t decode transactions, fuzzers stall, auditors waste hours reverse-engineering How it works: • Finds sol_log("Instruction: …") in the ELF • Walks Anchor’s try_accounts control-flow graph to map signers & mutables info Brute-probes arg sizes, recalculates 8-byte discriminators • Spits out ready-to-use JSON. Early testing shows the tool recovers the vast majority of instructions. The tool just won 1st prize at Reverse Engineering Closed Source Solana Programs hackathon hosted by Accretion. Try it now - github.com/sec3-service/I…

We’re excited to release IDL Guesser - an open-source CLI that rips the IDL out of any closed-source Anchor program ! Blog: sec3.dev/blog/idl-guess… Code: github.com/sec3-service/I… The Gap: about half of the top-100 Solana programs ship with no IDL. Can’t decode transactions, fuzzers stall, auditors waste hours reverse-engineering How it works: • Finds sol_log("Instruction: …") in the ELF • Walks Anchor’s try_accounts control-flow graph to map signers & mutables info Brute-probes arg sizes, recalculates 8-byte discriminators • Spits out ready-to-use JSON. Early testing shows the tool recovers the vast majority of instructions. The tool just won 1st prize at Reverse Engineering Closed Source Solana Programs hackathon hosted by Accretion. Try it now - github.com/sec3-service/I…
