soispoke.eth
2K posts
soispoke.eth
@soispoke
research @ethereum, Robust Incentives Group
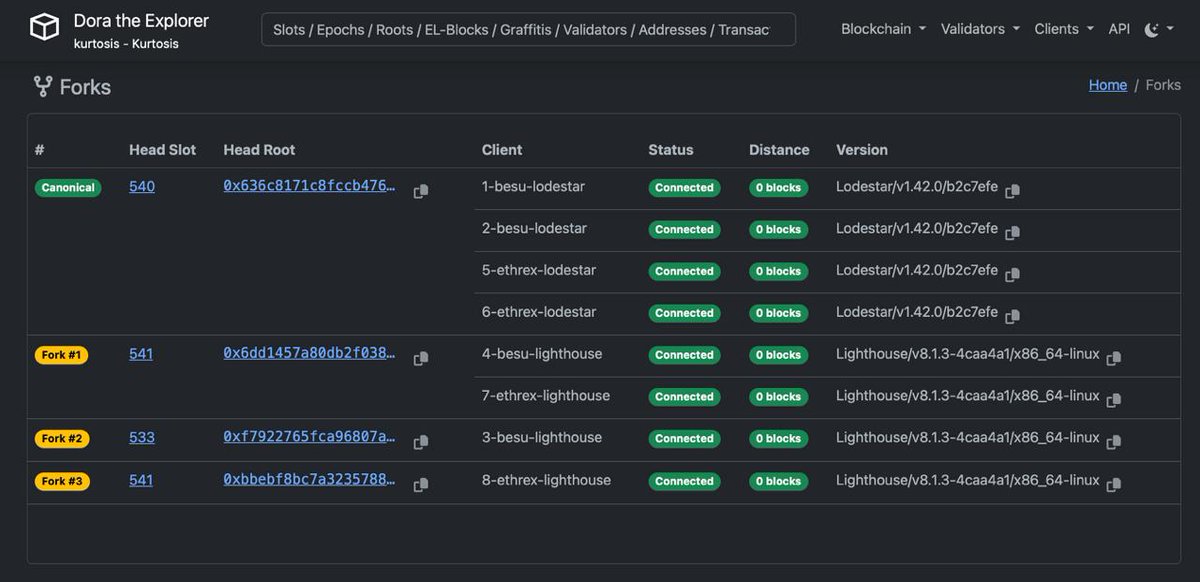
Last week, Ethereum core contributors gathered in Svalbard for the Soldøgn interop: a week long event focused on hardening Glamsterdam implementations to scale Ethereum securely ☀️ Read the full recap, including their candidate post-fork gas limit, below:



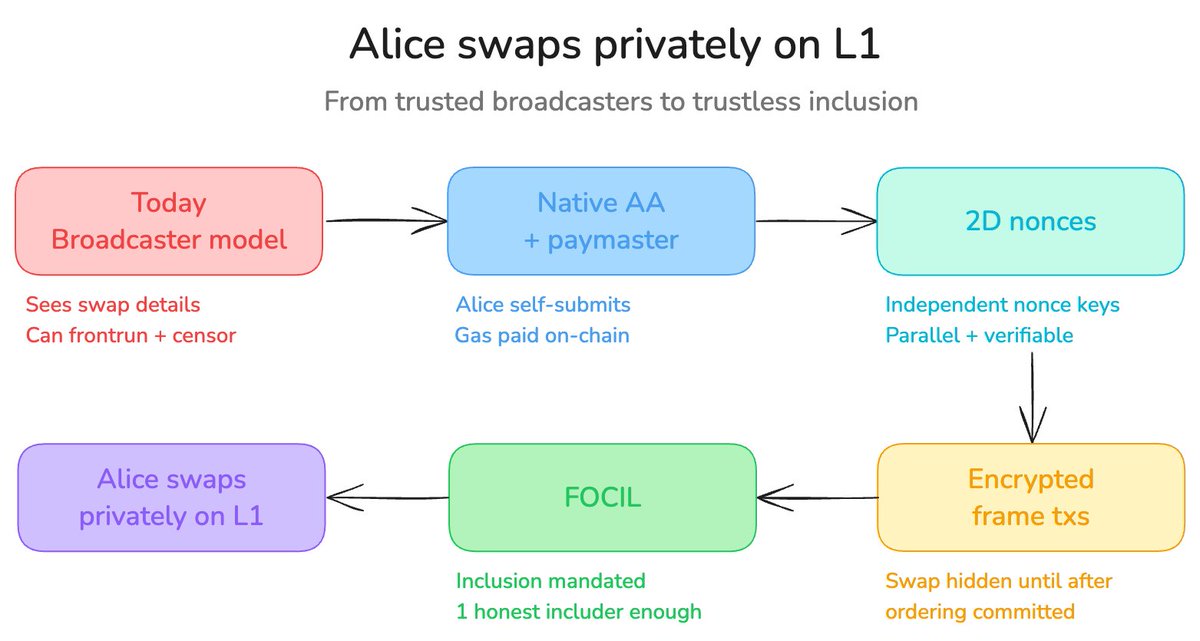
There’s been a lot of discussion this weekend across Telegram GitHub and Twitter about EIP-8141 It’s getting hard to keep track and properly educate yourself So I put together a single source of truth to learn about the future of Native AA on Ethereum eip8141.io




On Monday in NYC: Etherealize will join 150+ executives from major US institutions at the Institutional Ethereum Forum, hosted by @ethereumfndn. $250+ trillion in assets represented in one room to discuss Ethereum's role as infrastructure for the future of finance.