Marius Steffens
105 posts

Marius Steffens
@steffens_marius
Web security guy turned Information Security Engineer @Google. Graduate from @Saar_Uni and @CISPA. Opinions are my own.

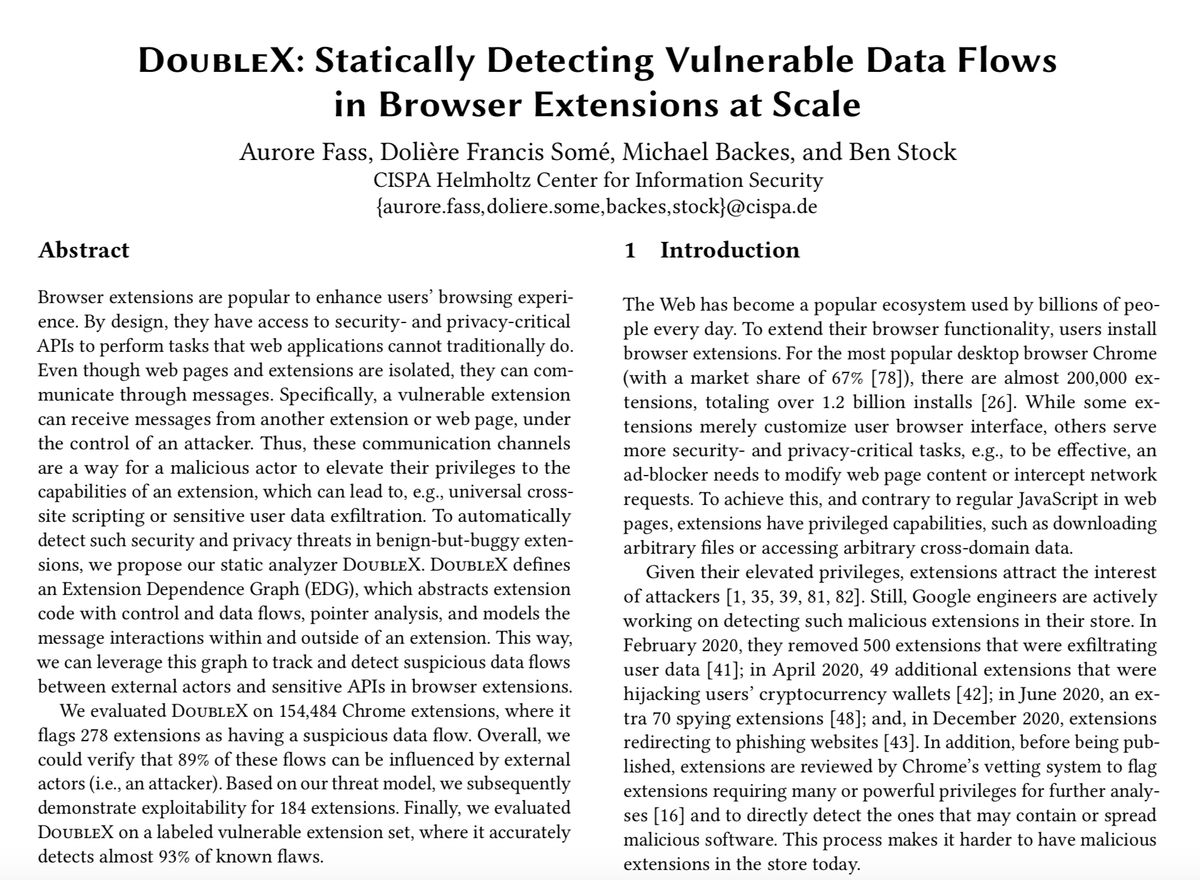
Among the alumni of my group, @AuroreFass recently joined CISPA as a faculty, @s3br0th is currently at postdoc at TU Wien, and @steffens_marius is having fun at Google these days. Want to follow in all of their footsteps? Then go ahead and visit swag.cispa.saarland/jobs.html!

Are you passionate about expanding the capabilities of the Tsunami network scanner, and would like to help keep AI infrastructure secure? See our blog post for details on getting involved and how your efforts will be rewarded 💸! bughunters.google.com/blog/569189023… bughunters.google.com/blog/569189023…

The results are in! We're proud to announce the Top 10 Web Hacking Techniques of 2023! portswigger.net/research/top-1…


HITCON Community 2023 - 議程宣傳第二彈 ✨ Day2 的 Keynote 10:10!Tag: Red、Exploit Development、Fuzzing 🚀#2「Advancements in JavaScript Engine Fuzzing 」 瀏覽器作為一般人接觸網路最直接的入口,其安全性非常重要,瀏覽器的漏洞影響不容小覷。而JavaScript 的複雜性,已然成為瀏覽器漏洞的主要成因之一。在這場議程中,將著重介紹如何系統化的找出 JavaScript 的漏洞。講者將分享如何設計及優化他們的 JavaScript Engine Fuzzer,以及他們挖掘到的漏洞。值得特別關注的是,他們的使用的 fuzzilli 是開源的,大家都可以拿來使用進行實驗。 🎙️講師資訊: Google V8 Security Team 的 Carl Smith,曾在 Exodus Intelligence 及 Google Project Zero 實習,在世界許多資安會議都有發表過他們的研究。這場議程,也是頂尖資安會議 OffensiveCon 的精彩議程。 hitcon.org/2023/CMT/agend… #HITCONCommunity2023 #HITCONCMT2023 #HITCON





The Web is going MAD again! Join us for the 5th #MADWeb workshop @NDSSSymposium 2023! Please consider submitting your awesome Web Security & Privacy research (deadline: Dec 9 AoE), and help us spread the words! CFP: madweb.work @zubair_shafiq


Congrats to my student @JohKrupp, who successfully defended his PhD thesis titled `Using Honeypots to Trace Back Amplification DDoS Attacks`! He should be your go-to person for amplification #DDoS attacks. The thesis answers 3 exciting questions (+ one I cannot yet share): 🧵1/3

Today, I can officially announce that I have been awarded tenure at @CISPA. It has been a fascinating journey to get here and I want to thank some folks. First, @thorstenholz and Felix Freiling who sparked my interest in IT security early in my studies.







Ever wondered why so many CSPs in the wild are trivially bypassable? In our new @acm_ccs 2021 paper we conducted a study to uncover the root causes behind those omnipresent misconfigurations. Read it here: swag.cispa.saarland/papers/roth202… CC: @_lgroeber @cathykxx @kcotsneb @CISPA

Happy to announce my second PhD, @steffens_marius defended his PhD thesis today with distinction. Super happy and proud to have seen him grow over the last years. Thanks also to @asabelfeld and @CasCremers for being part of the committee.