Sabitlenmiş Tweet
Steve Tippeconnic
35.9K posts

Steve Tippeconnic
@stevetipp
CybersecurityASU grad | Quantum computing experiments | Engineer/Producer | @BitViewAR
Los Angeles, CA Katılım Şubat 2009
1.2K Takip Edilen8K Takipçiler

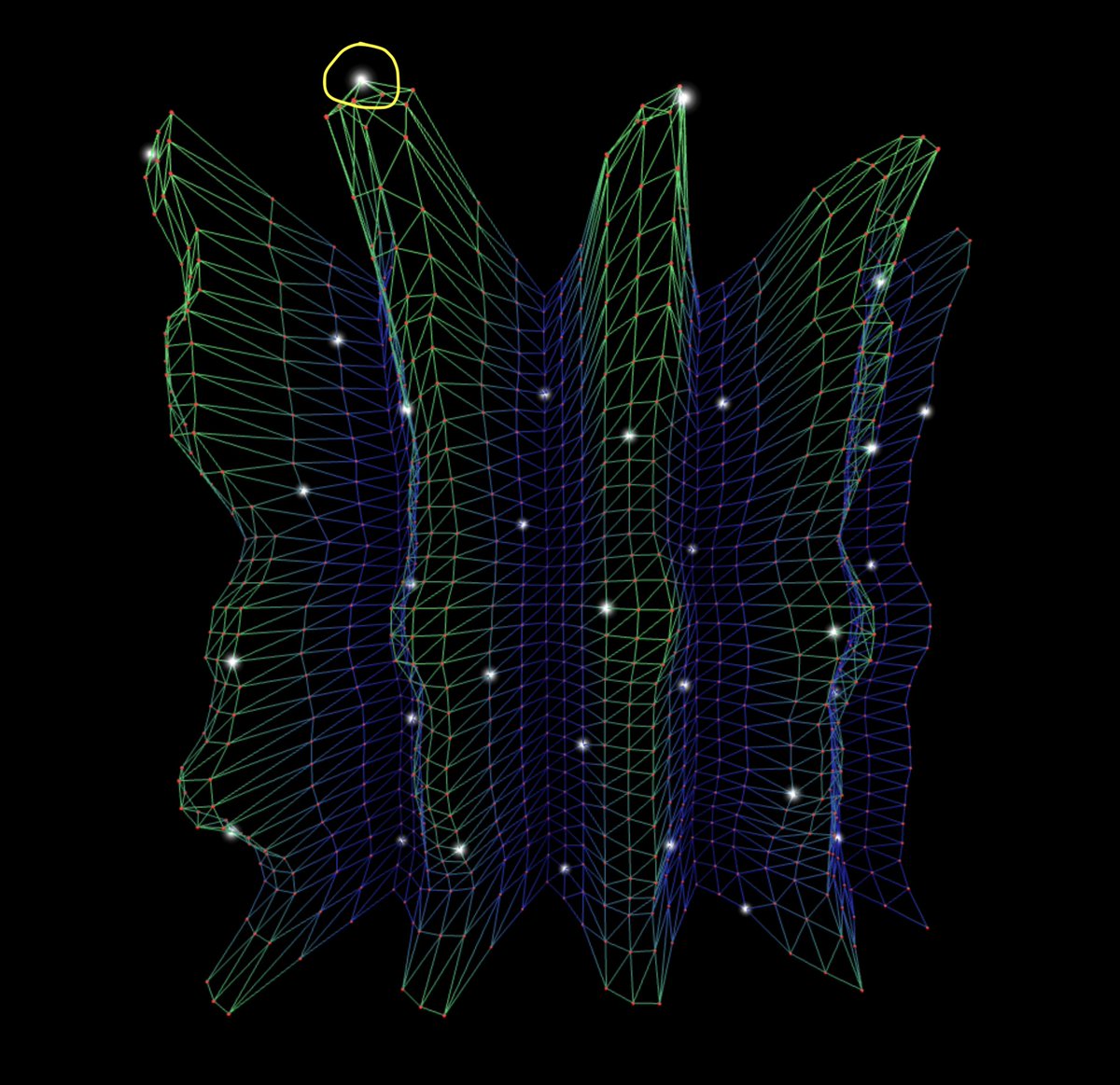
In my 5-bit arXiv IBM Quantum paper, this 6-bit experiment, and this new Codex post-processed visualization of that result, the glowing white points mark the full exact modular ridge for the correct key candidate. In this 6-bit case, that ridge is the set of points satisfying a + 42b ≡ 0 mod 64, which comes from the oracle structure aP + bQ with Q = kP. Every point on that ridge is consistent with the same hidden key relation, while the height of the surface shows how strongly the measured interference supports different parts of that ridge. The highest points are the strongest recovery locations because that is where constructive interference reinforces the hidden relation most strongly. Lower valley points can still lie on the correct ridge, but they carry less probability mass.
English

IBM has a great promo where if you log 20 minutes of compute on IBM Quantum machines within any 12-month period and have a non-trial account, you can opt in to a one-time offer of 180 minutes for the next 12 months.
This will help me run larger circuits outside of the usual 10-minute window. Thanks to @IBM for this.
More: ibm.com/quantum/blog/o…

English

@stevetipp Those visuals are incredible @stevetipp. Incredible work as always. 🔥
English

In my arXiv paper, and in this new Codex post-processed visualization of that result, these points, shown in white in the new visual, are high-amplitude key-recovery candidates on the modular interference structure. Points on the correct ridge map to the same key, here k = 7, through a + bk ≡ 0 mod 32. The highest points (circled in yellow) are the strongest attack vectors because that is where constructive interference most strongly reinforces the hidden relation. Lower valley points can still fit the ridge too, but they carry less probability mass.
English

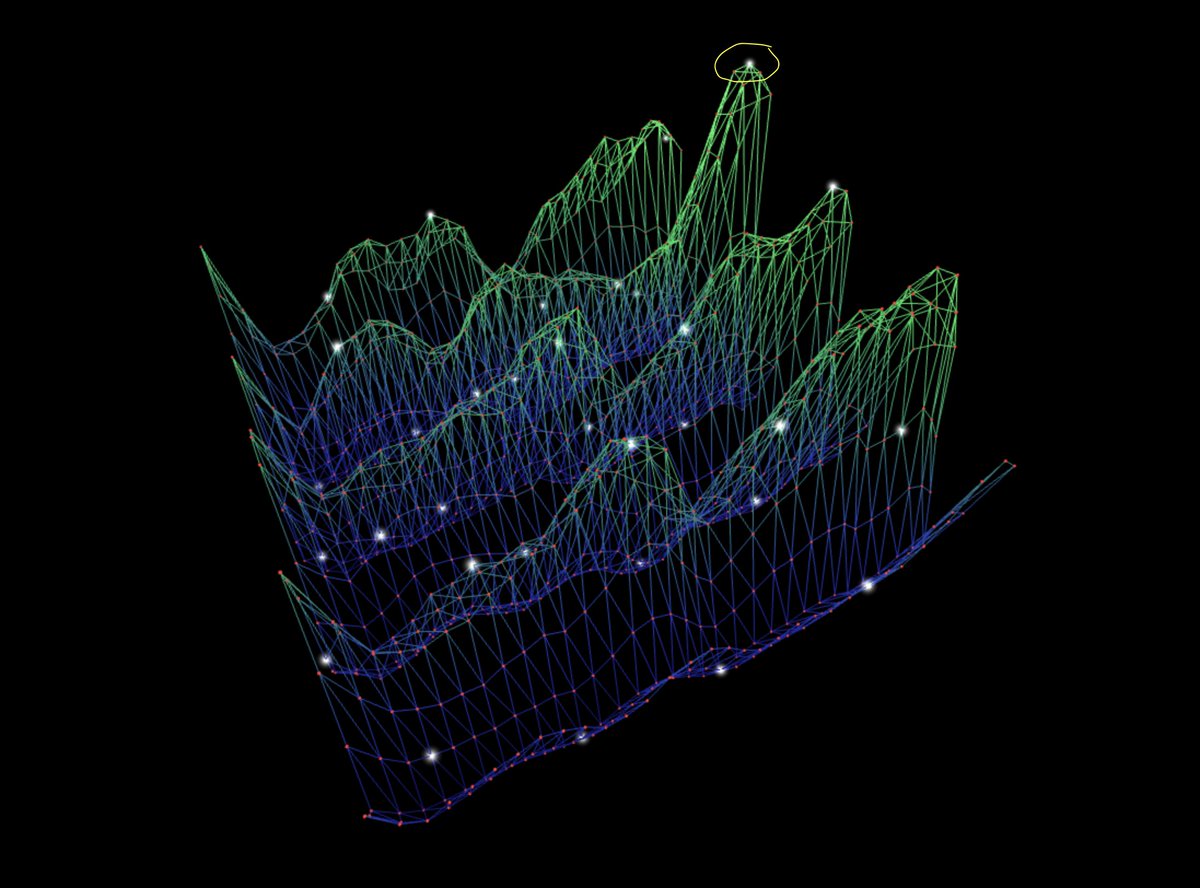
Here’s an update to the Three.js render that adds glowing white modular-ridge states using the Codex post-analysis of my arXiv paper. The surface shows the remapped, normalized, toroidally smoothed 5-bit probability grid, the red dots mark every lattice sample point, and the glowing points make the full a + 7b ≡ 0 (mod 32) ridge easier to see against the interference landscape. Interact with the render on Qwork: stevetipp.github.io/Qwork.github.i…
Steve Tippeconnic@stevetipp
English

The @threejs visual below represents the Codex reanalysis of the 5-bit Shor-style result grid after the measured bitstrings were remapped into (a,b) coordinates, normalized into probabilities, and smoothed with the same toroidal 3 x 3 box filter used in visualize_ridges.py. The horizontal plane encodes all possible reanalyzed outcomes as a 32 x 32 grid, where each coordinate (a,b) corresponds to one lattice cell in the joint measurement space. The vertical height of the surface shows the magnitude of the smoothed probability at each location. The blue-to-green mesh encodes the full Codex-smoothed output distribution, with blue indicating lower-probability valleys and bright green marking higher-probability peaks. The white dots trace every point satisfying the modular ridge condition a + 7b ≡ 0 mod 32. All red dots represent the discrete lattice sample points across the full grid, positioned directly on the surface so their height matches the smoothed probability at each bin. The surface is wave-animated as a visual effect to improve the view of the interference geometry. Interact with the render on Qwork: stevetipp.github.io/Qwork.github.i…
English

One interesting detail in the Codex reanalysis is the ordering of the top three ridge candidates. The highest scoring slopes were k = 0, k = 16, and k = 7 (the true key).
The first two have simple modular symmetries in mod 32.
k = 0 corresponds to the zero-slope ridge a ≡ 0, which often collects probability because of marginal bias in the measured grid.
k = 16 is the half-modulus slope in mod 32, which introduces a natural reflection symmetry.
What’s interesting is that k = 7 still appears as a stable third ridge, even against these symmetry-favored competitors.
English

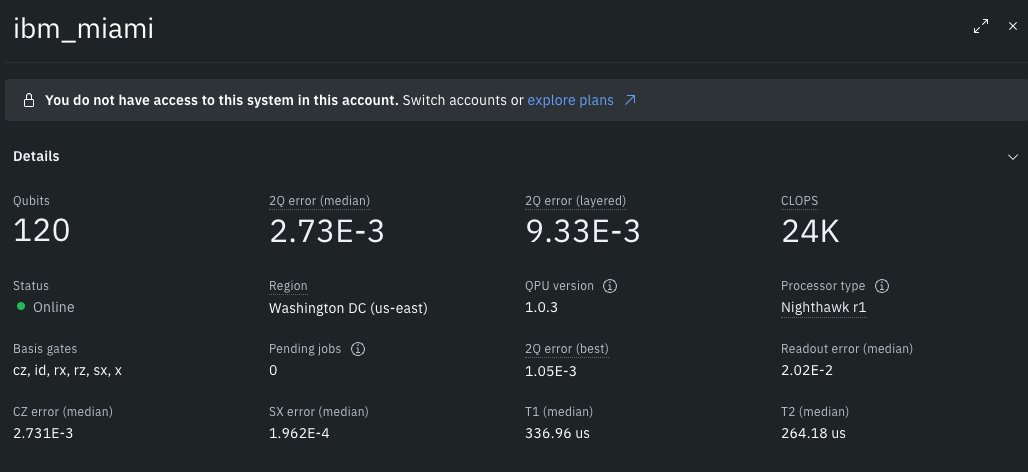
The new @IBM Nighthawk r1 processor has an interesting topology. It’s currently restricted to paid plans. Curious whether the tighter lattice could benefit grid-structured or phase-encoded Shor-style layouts.

English

The representation does not map public keys to private keys. It fixes a finite subgroup basis so the unitary group action of a known public element Q can be implemented. The circuit is constructed from public P and Q only, and the discrete log k is inferred from phase interference after the QFT, not supplied to the oracle.
English

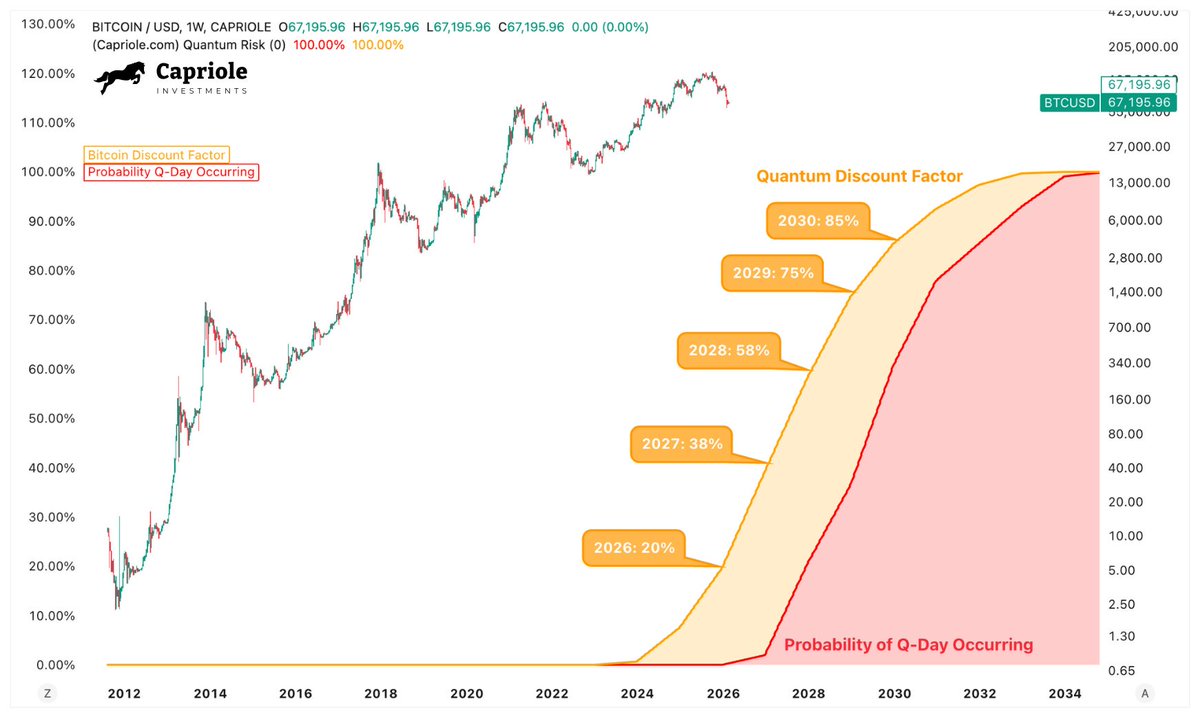
New Research: Discounting Bitcoin's Value for Quantum Risk
When you consider the statistics for when Q-Day is expected to occur, the rational investor is discounting the fair value of Bitcoin by 20% today. That discount factor doubles every year we don't progress quantum proof code on Bitcoin.
In little over a year, Bitcoin will be worth half as much if we do not progress quantum proof code.
A must read for every Bitcoiner.
Share this with your friends and get it in front of the Bitcoin core developer team. We must act to resolve the quantum threat in 2026.
caprioleio.substack.com/p/discounting-…
English

That thread critiques the 5-bit arXiv paper and 6-bit experiment against claims the work doesn’t make and misstates several technical points. The experiment is a proof-of-principle demonstration of Shor-style phase interference for a fixed ECDLP instance on real IBM NISQ hardware. The oracle is constructed from the public instance (P, Q), and the private scalar k is not embedded in the oracle. The hardware executions were run on IBM backends despite depth-limited fidelity, and the reported result is not single-bin key recovery but the repeatable emergence of a non-uniform interference structure relative to a uniform baseline. I’ve addressed these points in detail here: x.com/stevetipp/stat…
English

@caprioleio Lol. No. x.com/BobMcElrath/st…
The fact that you don't even understand how big of a fraud that is shows you are completely unqualified to analyze this issue at all.
Bob McElrath@BobMcElrath
5/6-bit ECC has NOT been broken by a quantum computer. 1. The answer was provided to the compiler to build the circuit 2. The circuit was too deep to run on real hardware 3. The results are indistinguishable from random noise Cc: @lopp @brian_trollz @nic_carter @stevetipp 🧵
English

@aniekan_Q Thanks for the question! This experiment isn’t an encryption technique. It’s an experimental demonstration of recovering a toy ECC scalar using quantum interference on hardware. The goal is to study how discrete logarithm structure appears in quantum phase space.
English

@stevetipp Is this the closest we have to a new ecc encryption technique?
English

Full open source paper version of this experiment is now available here: github.com/SteveTipp/Qwor…
Steve Tippeconnic@stevetipp
English

The @threejs interferometric renderer below visualizes the measured Fourier-domain output of the 5-bit phase-only Shor-style scalar recovery experiment executed on ibm_marrakesh. The horizontal plane encodes the complete joint measurement space as a 32 x 32 grid, where each coordinate (u,v) = (a,b) corresponds to the two quantum registers after application of Quantum Fourier Transforms. The vertical structure shows the observed probability distribution obtained directly from backend measurement counts, taller regions indicate outcomes constructively amplified by interference under the encoded global phase relation ϕ(a, b) = 2π/32 (a + kb), corresponding to the unitary phase factor e^iϕ(a,b). The green wireframe surface renders the full amplitude landscape across all measured outcomes, while red markers denote the discrete histogram cells corresponding to individual (a,b) measurement results, rising proportionally to their observed frequency. A yellow sphere marks the dominant experimentally measured peak extracted directly from the data, identifying the Fourier mode where interference concentrates probability mass. The surface is sinusoidally animated for visualization, allowing the interference geometry to appear as a localized standing-wave structure in Fourier space. Interact with this render on Qwork: stevetipp.github.io/Qwork.github.i…
Green Mesh = Amplitude surface over the full joint outcome space (a,b)
Red Dots = Raw backend measurement counts at each (a,b) cell (height proportional to frequency)
Yellow Sphere = Dominant measured Fourier peak determined from result data
English

@YuviLightman @QuantumCanary_ Thank you Yuvi, possibly! Just sent a dm to hear more.
English

@stevetipp Amazing project Steve! Are you interested in doing an interview about it for @QuantumCanary_ ?
English

