strukt retweetledi
strukt
125 posts

strukt
@strukt93
LSR @Spearbit - Triage @Hacker0x01 | ex-@Quantstamp | ex-@HalbornSecurity
Katılım Mayıs 2024
135 Takip Edilen68 Takipçiler
strukt retweetledi
strukt retweetledi

Announcing the Solana Audit Arena ⚔️
A free, weekly security competition for Solana security researchers.
Every Monday I drop a new Anchor program, built using the safe-solana-builder tool and real-world DeFi implementation.
Why?
→ Junior researchers have no clear path to prove themselves
→ No practice ground with realistic Solana programs
→ AI is raising the floor; you need to be above it
github.com/Frankcastleaud…

English
strukt retweetledi

I Saved Injective's $500M. They Pay Me $50K.
I like hunting bugs on @immunefi . I'm decent at it.
- #1 — Attackathon | Stacks
- #2 — Attackathon | Stacks II
- #1 — Attackathon | XRPL Lending Protocol
- 1 Critical and 1 High from bug bounties (not counting this one)
Life was good. Then I found a Critical vulnerability in @injective .
This vulnerability allowed any user to directly drain any account on the chain. No special permissions needed. Over $500M in on-chain assets were at risk.
I reported it through Immunefi. The next day, a mainnet upgrade to fix the bug went to governance vote. The Injective team clearly understood the severity.
Then — silence. For 3 months. No follow up. No technical discussion. Nothing.
A few days ago, they notified me of their decision: $50K. The maximum payout for a Critical vulnerability in their bug bounty program is $500K. I disputed it. Silence again. No explanation for the reduced payout. No explanation for the 3 month ghost. No conversation at all. To be clear: the $50K has not been paid either.
I've seen others share bad experiences with bug bounty payouts recently. I never thought it would happen to me. I can't force them to do the right thing. But I won't let this be forgotten.
I will dedicate 10% of all my future bug bounty earnings to making sure this story stays visible — until Injective pays what I deserve.
Full Technical Report: github.com/injective-wall…
English
strukt retweetledi

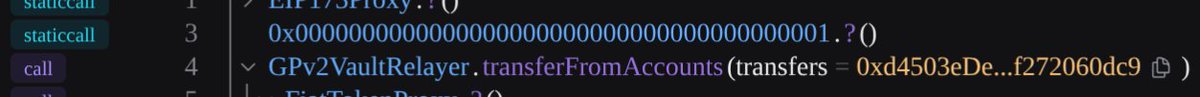
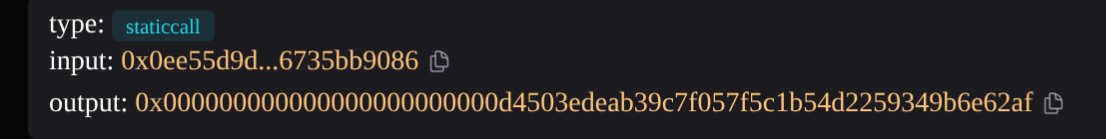
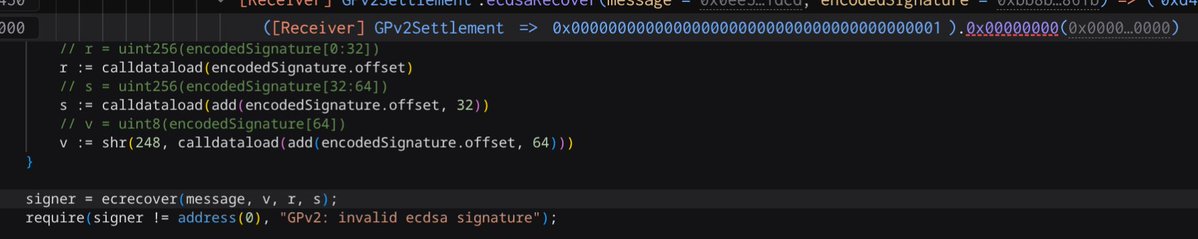
How is it possible that a call to address(1) returns data?
Precompiles
address(1) = call to ecrecover
transaction
tx-graph-eight.vercel.app/tx/0x1a696cad4…
English
strukt retweetledi
✨Introducing evmresearch✨✨
A knowledge graph of nearly everything I've learned about the EVM in the past six years
The graph structure emulates the brain, exponentiating research speeds for both humans and agents
evmresearch.io
English
strukt retweetledi

I audited an OTC escrow protocol on @solana
3 Criticals + 4 Highs
Every single critical came from a different root cause
But they all shared the same origin:
the program made assumptions about accounts
it never actually enforced
English
strukt retweetledi

#PeckShieldAlert The IoTeX[.]io Bridge @iotex_io has been hacked for over $8M worth of crypto due to a compromised private key.
The hacker has swapped the stolen funds to $ETH and has started bridging them to #BTC via #Thorchain.

English
strukt retweetledi

Published a writeup about a password reset flow using HMAC. An attacker could create valid tokens for other accounts by manipulating the values around the boundaries when the values got concatenated. asdf.foo/2026/02/13/usi…
English
strukt retweetledi
strukt retweetledi
strukt retweetledi
strukt retweetledi
Thanks for participating in this challenge! I analyzed the qs parser source code and wrote about the inconsistency between the backend and frontend query parsers, along with two possible solutions. Hope you enjoy it!
blog.voorivex.team/when-two-parse…

AmirMohammad Safari@AmirMSafari
Can you spot the XSS vulnerability? 👀 Test it out live at: pwnbox.xyz
English
strukt retweetledi

We're hiring across multiple @cantinaxyz teams!
Check out our open positions below 👇
jobs.ashbyhq.com/spearbit
Reach out if you want to find out more🤝
#cantina #spearbit #hiring #web3 #security #ai

English

@lonelysloth_sec @m4rio_eth That still takes a big deal of guesswork though
English
strukt retweetledi

AI bots like @openclaw's Clawdbot surface 1000s of vulnerabilities every day.
So we had to act. 🦞
Introducing ClawdStrike.ai: a free terminal skill to analyze any ClawdBot build, derived from our AI security expertise protecting the most complex production systems.
See how it works:
English
strukt retweetledi

Cantina's AI Code Analyzer just found a high-severity bug in @provenancefdn.
We discovered that a single transaction could trigger a panic in the EndBlocker and halt the entire chain, which their team promptly fixed.

English