Karsten Hahn
9.4K posts


Karsten Hahn
@struppigel
MalwareAnalysisForHedgehogs, Principal Malware Researcher at GDATA, he/him 🦔🌈🏳️⚧️




HWInfo and CPU-Z both compromised. Millions about to be PWNED! CPU Z: hybrid-analysis.com/sample/eff5ece… HW Monitor: hybrid-analysis.com/sample/4968501…




if ppl could stop communicating with threat actors, that would be really great











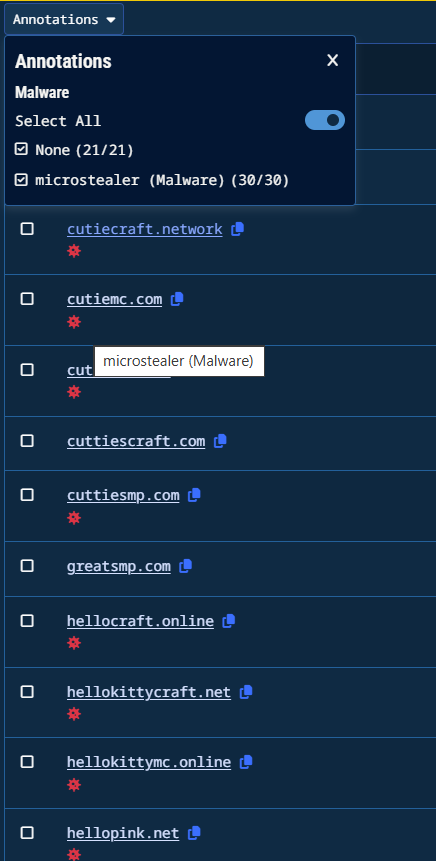
In collaboration with @rifteyy, G DATA's Karsten Hahn describes how the SugarSMP Minecraft server is scamming users to install Spark stealer disguised as Minecraft mods. Similar-looking servers distribute Electron-based stealers. blog.gdatasoftware.com/2026/03/38390-…




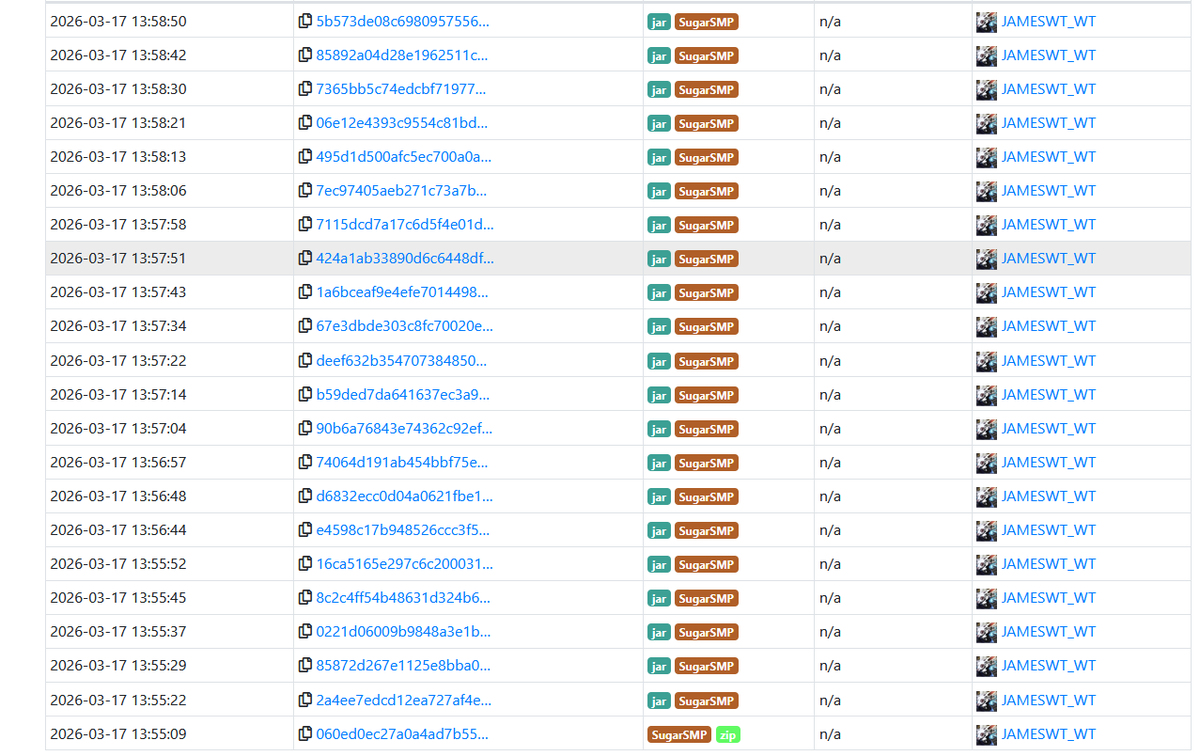
I wrote an article about SugarSMP Minecraft scams, Spark stealer and hacked accounts After a brief contact to the threat actor, we talked to two victims and followed the trail. Analysis in collaboration with @rifteyy #GDATATechblog @GDATA #GDATA blog.gdatasoftware.com/2026/03/38390-…