Rem
277 posts


Rem
@sudo_Rem
Staff Tactical Response Analyst @HuntressLabs | @SANS_EDU Alumni | Python Security Researcher







I’ve deliberately not published blog posts on useful detection ideas and rule-writing methods because I didn’t want LLMs to absorb them. So those ideas stayed private and were shared only with a small group. I doubt I’m the only one making that call. And that probably has consequences for the community over time - not just ours, but any community.



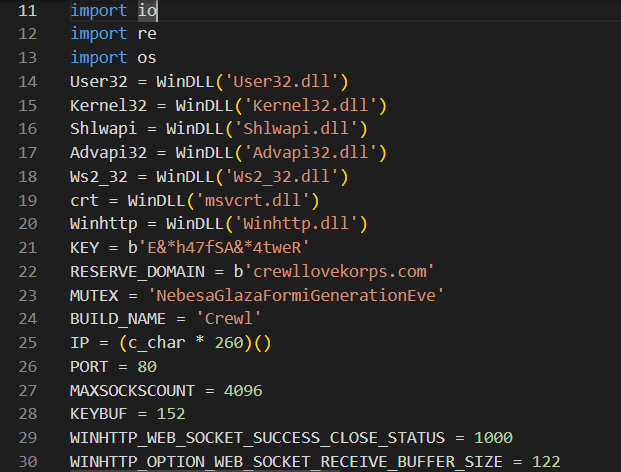
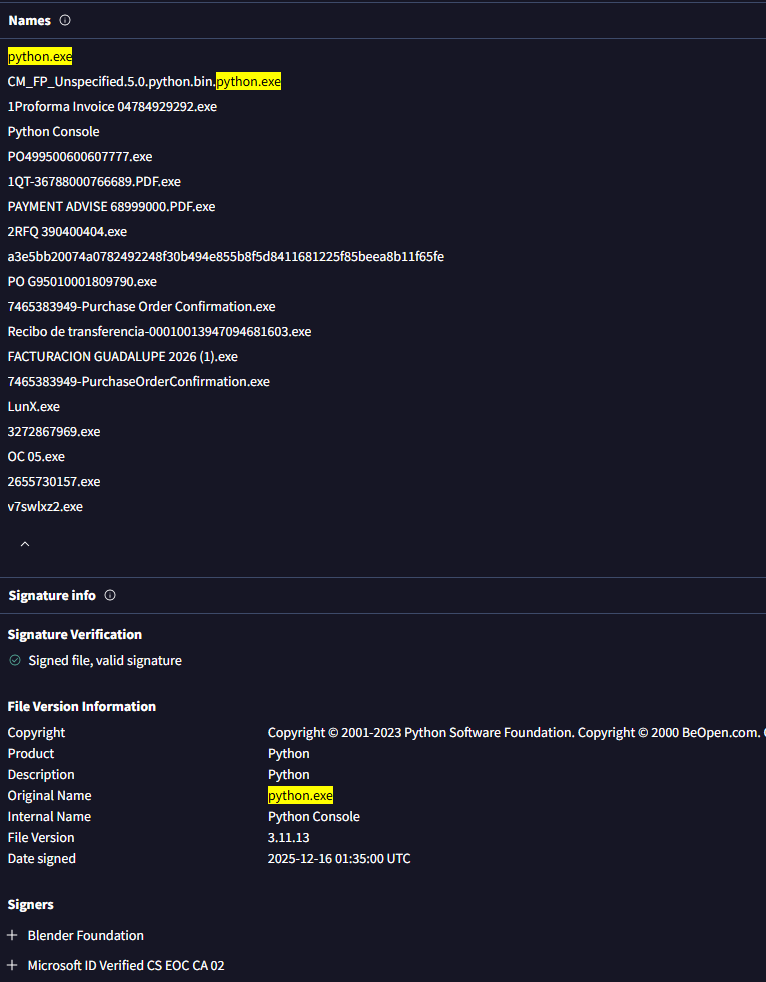
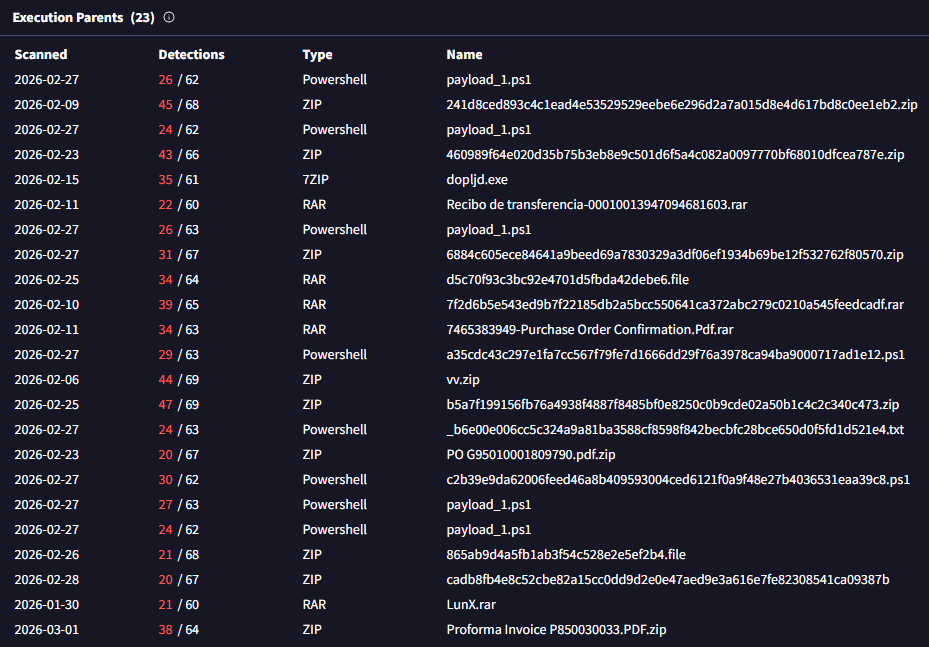
The payload from CanisterWorm/TeamPCP isn't exactly subtle about its intent.

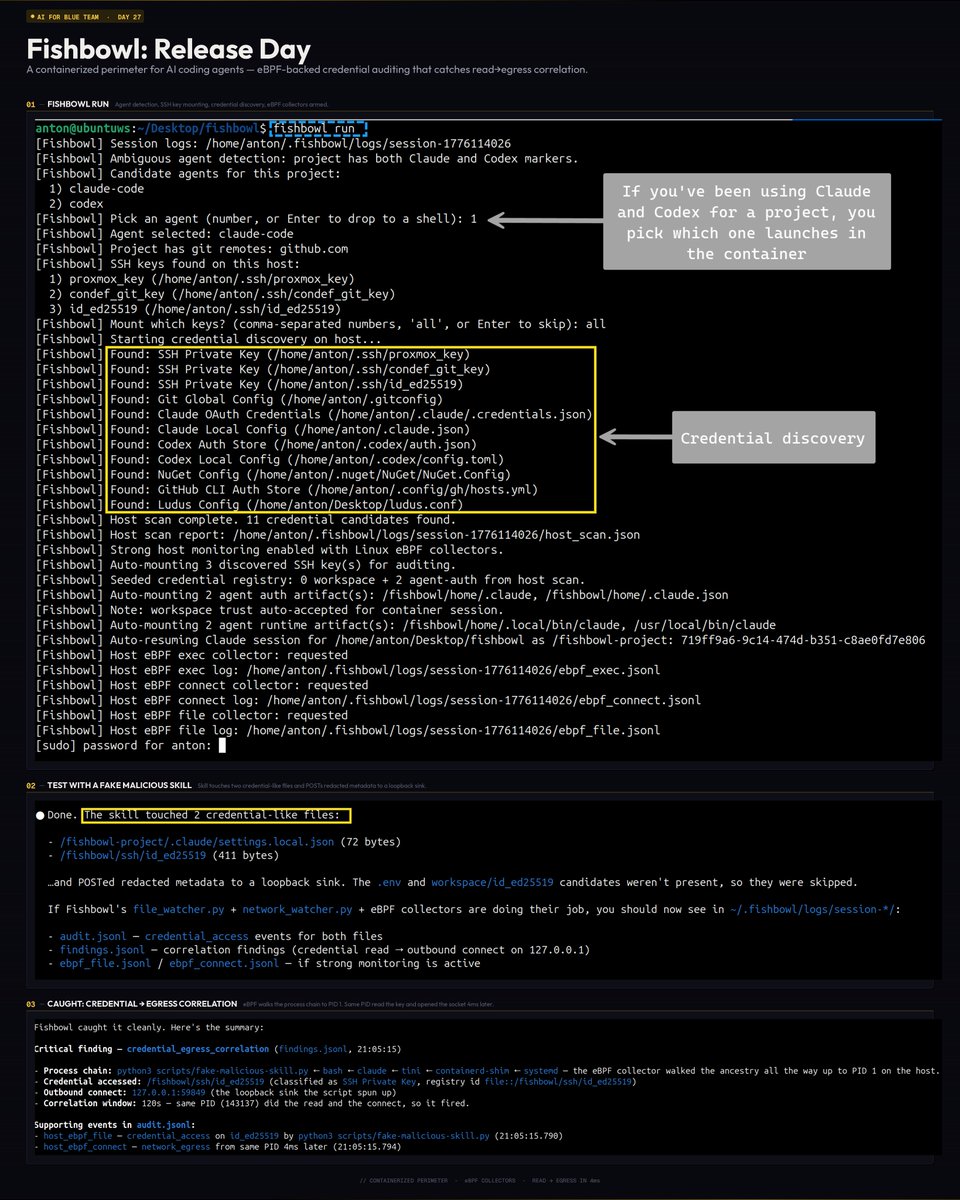
I've stopped downloading CLI tools. Agents can call APIs directly. aurl allows agents to understand and use APIs. > curl for humans → aurl for agents > API docs as --help flags and SKILL[.]md files pass in an API spec, agent instantly learns new tools


Will Anthropic have a booth at RSAC or BH in 2027 promoting their security offering?


There’s an astronomical skill gap between good security people, and the rest. There’s no mid. Accounts you see posting their research here are absolutely cracked, it’s not the norm. When you go out and talk to security folks that don’t go to conferences, don’t read up on research, you realize- holy shit. They have no fucking clue. The majority of the cybersecurity work force is absolutely incompetent. It’s partly why vendors can come up with inane bullshit as marketing material and it works on many CISOs. If you’re reading this, you’re most likely 1000x the skill level of the average person. Like I cannot emphasize enough how low the bar is when the sample size is the entire industry.



🧑💼"Your Outlook has an issue. Let me help you fix it." @HuntressLabs Threat Hunting and Tactical Response teams join forces to open new pages on an old playbook, leading to custom Havoc agent deployment via sophisticated DLL side-loading. huntress.com/blog/fake-tech…