McSam
1.6K posts

McSam retweetledi
It started as an idea, now it’s a platform that creates opportunities for young Ghanaians to become the nation’s digital defenders.
#brCTF2025 #OsagyefoEdition #DigitalSovereignty #CaptureTheFlagGH #NSCAM2025
English
@RabbitPro @FlashbackPwn @pedrib1337 I also enjoyed the dns exploitation very much. When will you be uploading new videos?
English
McSam retweetledi
Join our 2-day Adversarial Tradecraft & Detection training; hands-on tactics, real-world defence.
📅 23rd–25th Oct | 📍Kobi’s Event Center, Accra
💰 GHC 1,900
🔗 Register: breakthecodectf.com/adversarial-tr…
#brCTF2025 #OsagyefoEdition #DigitalSovereignty #CaptureTheFlagGH #NSCAM2025

English
McSam retweetledi
The codes are cracking.
The teams are ready.
The flag awaits. 🚩
Be there for #brCTF2025 – The Finals!
📍Venue: Kobis Event Centre
🗓️Date: 24th–25th October
Don’t miss Ghana’s biggest cybersecurity showdown
#brCTF2025 #OsagyefoEdition #DigitalSovereignty #CaptureTheFlagGH
English
McSam retweetledi
The long awaited is finally here‼️
The brCTF Osagyefo Edition Qualifiers kicks off today
Start: 10AM today
End: Sunday, 11:59PM
#brCTF2025
#OsagyefoEdition
#DigitalSovereignty
#CaptureTheFlagGH
#NSCAM2025
👉 Sign up now: brctf.africa

English
McSam retweetledi

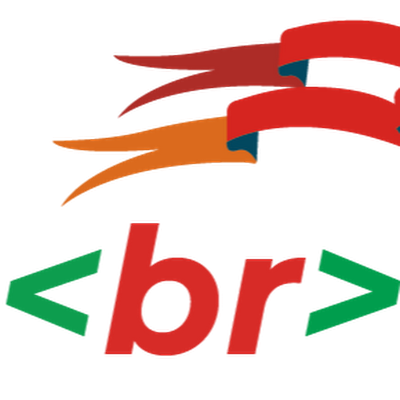
🧑💻🔎From Logs to Insights: Bridging the Gap between AI and Security Operations ⭐️
Security teams often spend hours digging through alerts, logs, and vulnerabilities. What if you could just ask a question in plain English and get the answer instantly?
I’ve built an AI agent that connects directly to Wazuh SIEM using the Model Context Protocol (MCP). This means you can chat with your security data in real time:
“Show me critical vulnerabilities on web servers.”
“Which agents are offline?”
“Are we meeting PCI-DSS requirements?”
Instead of running complex queries, you get clear, actionable answers—fast.
The goal is simple: democratize AI for SOC teams, threat hunting, and SecOps.
No more barriers between your data and your decisions.
I believe this is a step towards making AI a real partner in everyday security operations.
Would you add this to your SOC?
#CyberSecurity #AI #SIEM #SecOps #ThreatHunting #Wazuh #SecurityOperations #SOC #InfoSec #ArtificialIntelligence #MCP #SecurityAutomation #CyberDefense #DemocratizingAI #NextGenSOC


English

To celebrate our badge launch, we're giving away FIVE free 6-month licenses to @pentesterlab.
✅ Comment BADGELIFE and retweet this post to enter.
Additionally, pre-order a custom badge at shop.bugbountydefcon.com for a chance to win one of FIVE Annual VIP+ subscription to @hackthebox_eu. Purchasing a badge helps us run and fund the village.
That's a total of TEN WINNERS! Winners will be picked on August 1st. Good luck!
Note: Badges are pre-order only. Order online, pick up in village. No shipping. #BadgeLife #DEFCON33 #BugBounty
English
McSam retweetledi

Hackers, this Saturday is the day — mark your calendars!
Byte Time Sessions@bytetimesession
📢 BYTE TIME SESSIONS: BINARY EXPLOITATION WEBINAR 🎯 Topic: Bending the Bytes of Software — Basics of Binary Exploitation In the world of hacking, understanding software at the binary level is essential. (1/5)
English
McSam retweetledi

Hi, I'm John Umoru, a medical doctor from Nigeria, and I just passed the OSCP from @offsectraining
why is a doctor writing the OSCP, you may ask? well, if you followed the journey, you would understand better.
A thread!...

English

@theMcSam @BLVCKPRINXE yea same but i'm not ga so i dunno how true that is & yes we're in a new dispensation 🥂
English
@1bp7l_ @BLVCKPRINXE Ohh thought it was just a wordplay of the name Phillipa. Sorry oo, she’s Abena or Junior. ✋😂🤚
English

@BLVCKPRINXE @theMcSam chale he's ruining it, i hate the meaning of that name but that's what they used to call me in grade school. stopped responding to it because of it's meaning in ga or so
English
To help others test the vulnerability in a controlled environment, I’ve included a setup script for Gogs: github.com/theMcSam/CVE-2…
I hope it helps others better understand and validate this issue.
(4/4)
English
I've documented the full process, including technical insights and a step-by-step breakdown, on my blog: themcsam.github.io/posts/gogs-RCE…
The PoC exploit code is available here: github.com/theMcSam/CVE-2…
(3/4)
English


