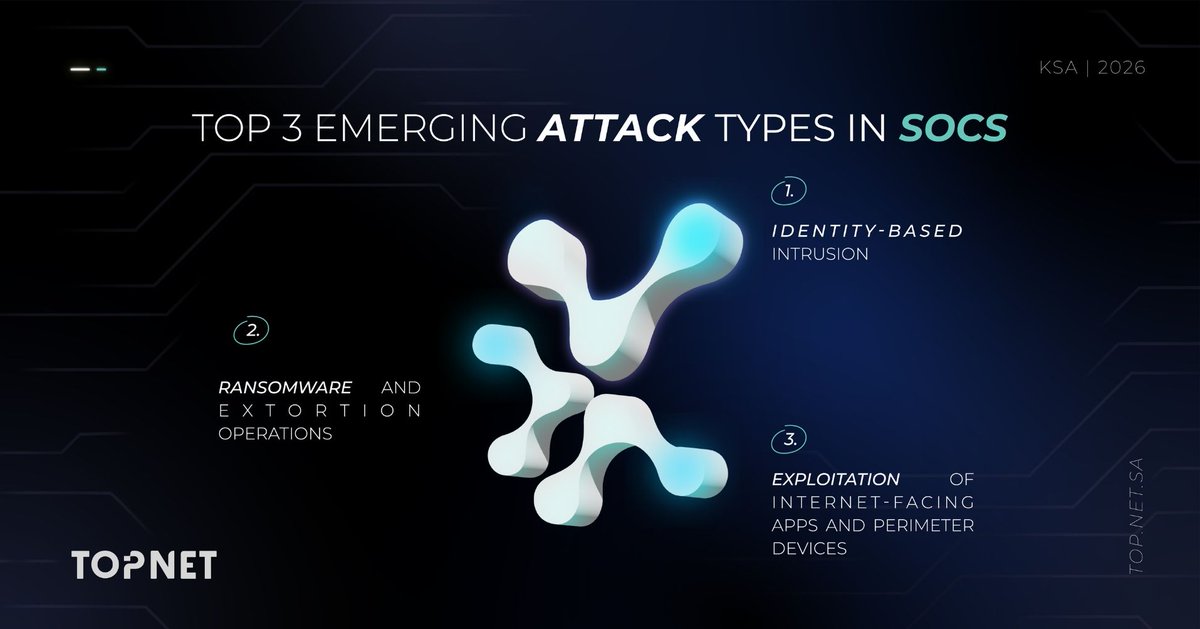
ما نلاحظه في كثير من الحالات هو أن الأنظمة تستمر بالعمل بشكل طبيعي بينما يبدأ الوصول بالتمدد داخل البيئة. لأن التحرك لا يعتمد على كسر الأنظمة، بل على استخدام وصول موجود ومصرح به بالفعل.
لهذا لم يعد السؤال فقط: كيف نمنع رسالة التصيد الأولى؟
السؤال الأهم أصبح: ماذا يمكن للحساب الوصول إليه بعد أول نقطة دخول، وما مستوى الرؤية والسيطرة الموجود داخل البيئة بعد تسجيل الدخول؟
العربية