Sabitlenmiş Tweet

NoSQL Exploitation Framework v2.0 Released , Added features,
github.com/torque59/Nosql…
#MongoDB #couch #redis #hbase #nosql @OpenSecurity_IN
English
Francis Alexander
236 posts





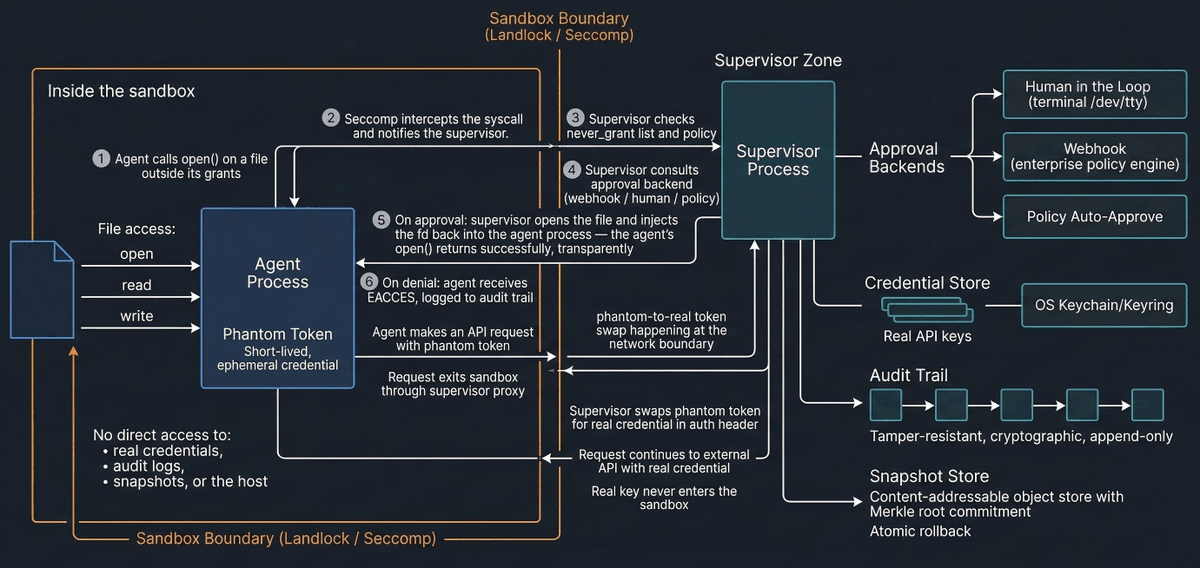


Big skill drop from @trailofbits today! Here are 10 new skills we publicly released from our internal repository: 🧵


For those of you who ever wanted to hear the sweet sweet sound of a turbofan engine starting up. 😍