Unhandled0xD
3.5K posts


Unhandled0xD
@trap_handler
Offensive Security Researcher, Interested in physics and neuroscience
Katılım Temmuz 2022
368 Takip Edilen5.1K Takipçiler

lol It will never hits opening IDA and Windbg at 3AM with a cold drink, disassembling the driver, starting to find bugs and that quiet moment hits when the decompiler throws out something wrong and your brain goes in god mode trying to find root cause and build the attack vector
Anthropic@AnthropicAI
Introducing Project Glasswing: an urgent initiative to help secure the world’s most critical software. It’s powered by our newest frontier model, Claude Mythos Preview, which can find software vulnerabilities better than all but the most skilled humans. anthropic.com/glasswing
English
Unhandled0xD retweetledi
Unhandled0xD retweetledi

Stealthy WMI lateral movement - StealthyWMIExec.py
ghaleb0x317374.github.io/2026/03/15/Ste…
English

@_CryptoCat Touching pizza is more better than touching grass, enjoy man !
English

@C5pider When we talk about stability and reliability we talk about havoc m8, great work Paul !
English

I release a short demonstration of the Kaine Extension System, allowing the operator to fully configure what features and evasion capabilities the agent should have and contain.
youtube.com/watch?v=a8YZPl…

YouTube
English

@_CryptoCat @LiveOverflow I want this documentary to not finish
English
Unhandled0xD retweetledi

@0x_shaq I always tell people to stop involving AI into everything, Just enjoy the stuff as it is with its complexity and its challenges otherwise it’s boring you doing nothing just watching your LLM doing all the fun stuff and you setting waiting for result
English
Unhandled0xD retweetledi

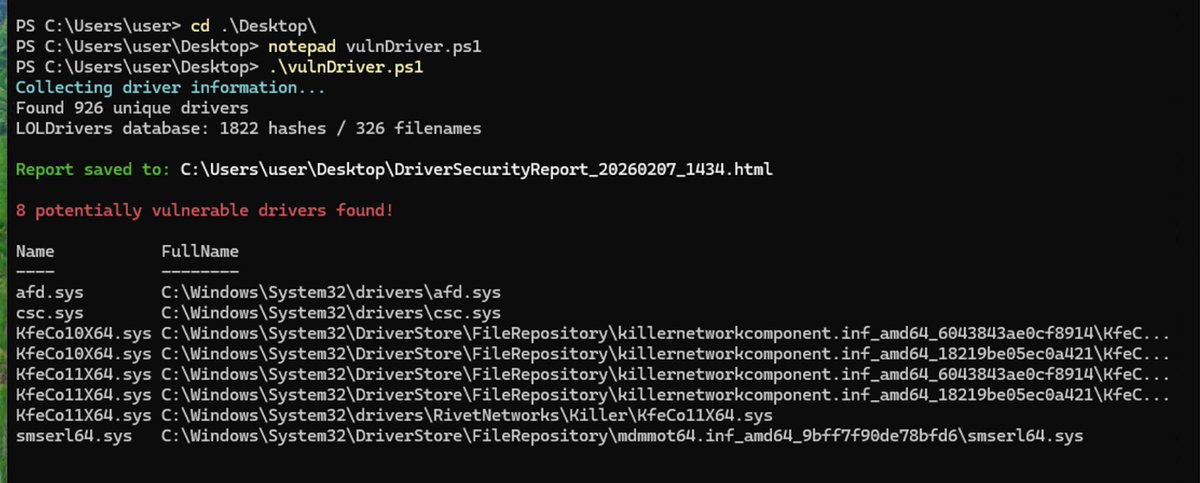
@UK_Daniel_Card On different builds the hash changes so maybe I have 2 windows 10 machines with different builds and afd.sys for example is on both of them but the hash is different in the 2 machines
English

@trap_handler why don't you think a hash comparison is accurate?
English
Unhandled0xD retweetledi

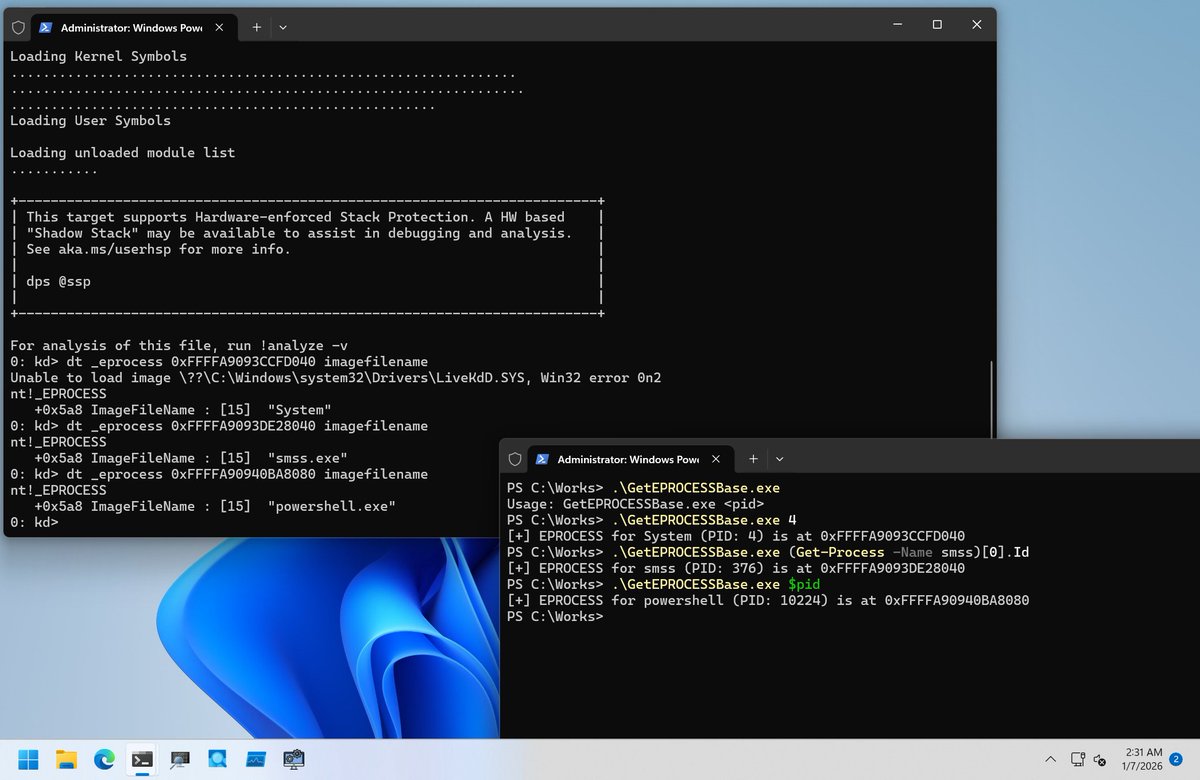
I'm tired to check EPROCESS address of a target process with !process command in Kernel Debugger.
So I wrote a small program to get it quickly.
github.com/daem0nc0re/Tan…
English

@ipurple It’s not enough, we need a BOF loader that loads a BOF loader that loads a BOF
English

InlineExecuteEx: A BOF that's a BOF Loader github.com/0xTriboulet/In…
English
Unhandled0xD retweetledi