
Tanic
72 posts

Tanic
@tzachyh
Curious, breaking stuff apart, failing my way through life, opinions are of one of the aliensrrr on Omicron Persei 8, where did I put my keys?
Katılım Kasım 2018
96 Takip Edilen36 Takipçiler
Tanic retweetledi

After two years of research that started at @alephsecurity and ended at @CyberarkLabs, I'm very excited to present my research on attacking ISPs via layer-2 PPPoE protocol live at @defcon!!!!
#defcon #defcon30 #pppoe #ppp @CyberArk
forum.defcon.org/node/242004
English
Tanic retweetledi
Tanic retweetledi

#Ruckus has confirmed six additional CVEs for my latest research. I will present new RCEs on Ruckus devices using these vulnerabilities at #defcon28 #DEFCONSafeMode

English

After a long wait, my 2nd blogpost on Homograph attacks. Specifically, bypassing chrome's IDN policy.
Aleph Research@alephsecurity
After some delay, here's the 2nd part of our Homograph research in which we show how we bypassed browsers IDN policy and take a deep dive into Unicode definitions. alephsecurity.com/2020/07/23/rev…
English
Tanic retweetledi

#defcon teams are investing so much effort in #defcon28 safe mode and I feel so honored to be part of this year's talks. Get ready for some #ruckus :)
DEF CON@defcon
It’s #defconsafemode 🚨 alert 🚨 time again! The main track talk schedule for #defcon28 is now #live! Permission to get psyched is #granted. More announcements on the way! This. Is. Happening. defcon.org/html/defcon-sa……/defcon-s…/dc-safemode-schedule.html
English
Tanic retweetledi

Small @GHIDRA_RE script that colors executed instructions to ease the debug procedure. Hope soon will add regs state to it :))
github.com/alephsecurity/…

English
Tanic retweetledi

There is an open position for a senior researcher on my team (located in Herzliya). Please contact me if relevant. @alephsecurity
English
Tanic retweetledi

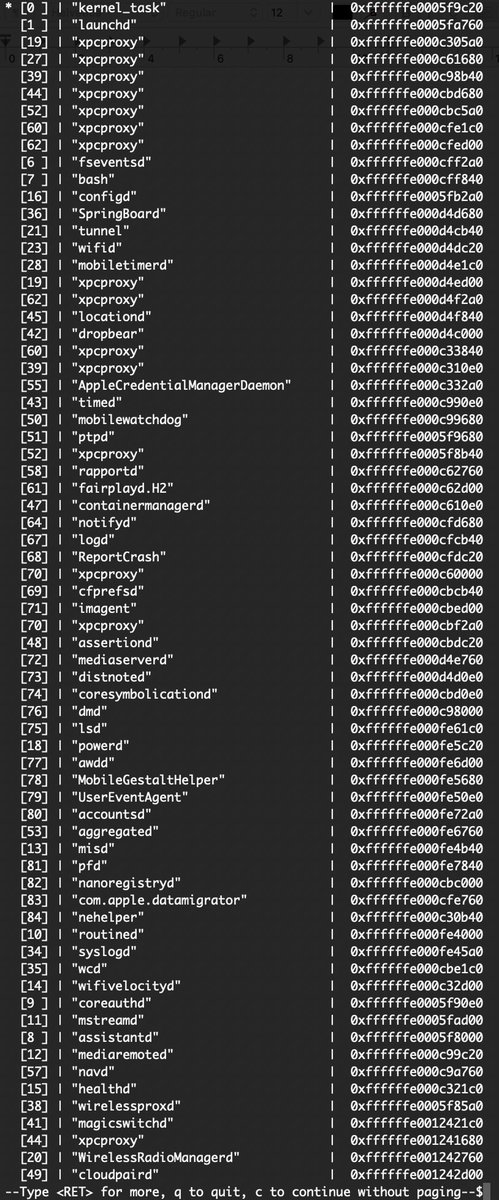
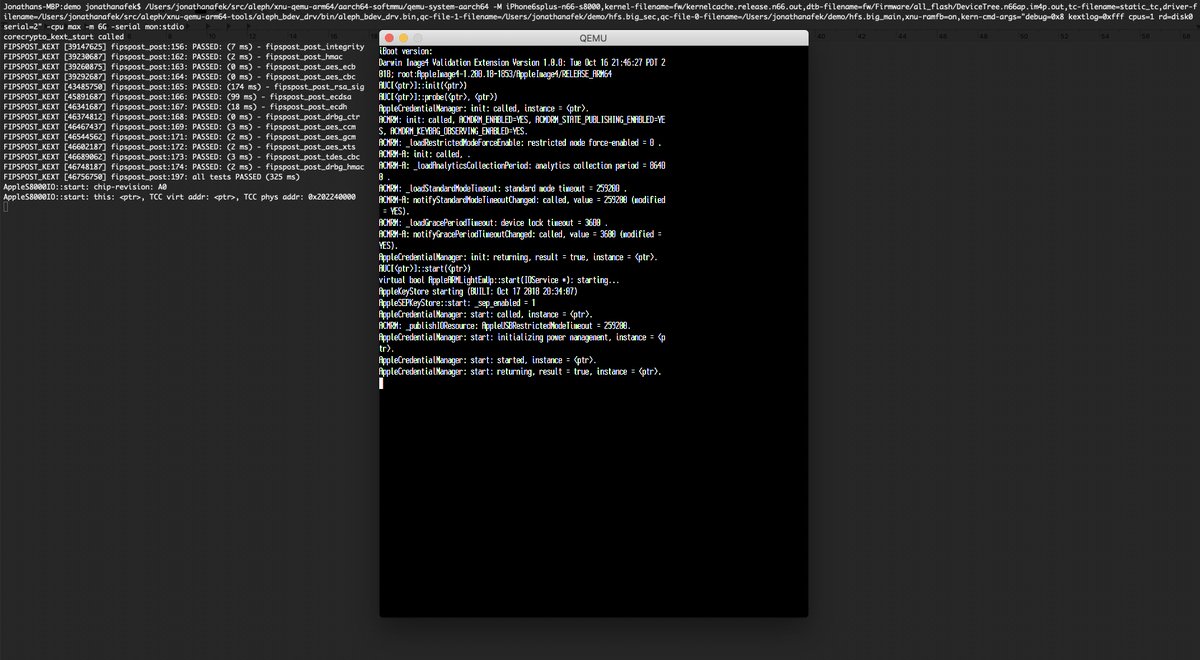
@offensive_con has been amazing! Truly the best conf I have been to. A special thanks for having the opportunity to present the research #iOS on #QEMU that me and my team were working hard on. The slides and the code with the new features are now released. Enjoy!
English
Tanic retweetledi

Continuing the iOS exploit development series:
Part 1: Heap Exploit Development: azeria-labs.com/heap-exploit-d…
Part 2: Heap Overflows and the iOS Kernel Heap azeria-labs.com/heap-overflows…
✨NEW: Part 3: Grooming the iOS Kernel Heap azeria-labs.com/grooming-the-i…
English
Tanic retweetledi

#INFILTRATE20 Speaker Highlight: Jonathan Afek (@JonathanAfek) will be presenting 'Simplifying iOS Research: Booting the iOS Kernel to an
Interactive Bash Shell on QEMU' infiltratecon.com/conference/spe…

English
Tanic retweetledi

Windows / Linux Local Privilege Escalation Workshop (Materials included !) 🥳
github.com/sagishahar/lpe…
English
Tanic retweetledi
Tanic retweetledi

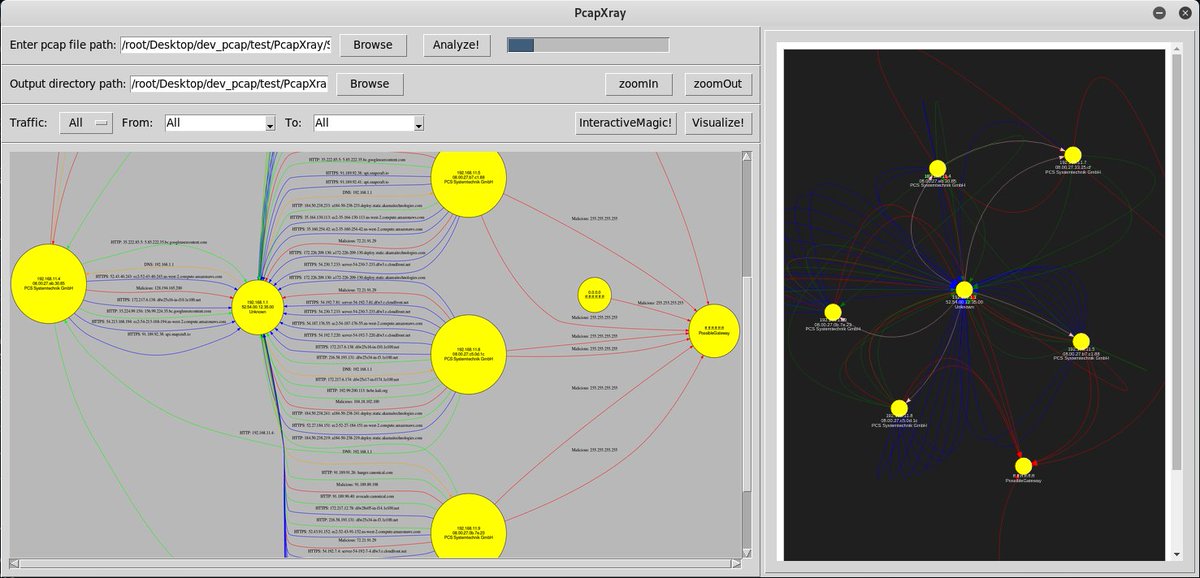
Given a Pcap File, plot a network diagram displaying hosts in the network, network traffic, highlight important traffic
#infosec #pentest #redteam #blueteam
github.com/Srinivas11789/…
English
Tanic retweetledi

I wrote some automation around gophish, evilginx2, and postfix for faster phishing deployment. Looking for feedback and pull requests :D
lockboxx.blogspot.com/2020/01/gophis…
github.com/ahhh/phish_com…
English
Tanic retweetledi

Can't wait to present the progress we've made since #BHEU at @offensive_con! tfp0, full disk mounts with our own block device driver, most of the iOS services running, ssh and a textual framebuffer. #offensivecon

English

@juliocesarfort @alephsecurity BTW, this research has started at the beginning of 2019 so I didn't have some of the references that available today.
English

Phishing is anyone's problem, but now it can get you in ways you didn't expect and for many users, no proper mitigation is currently available. Check it out: alephsecurity.com/2019/12/29/rev…
English

@juliocesarfort @alephsecurity Just saw your presentation, great work! Regarding the Australian paper, I couldn't find it, do you have some reference to it by any chance? Also, the references are in the links.
English
Tanic retweetledi

➦ 36C3 - SELECT code_execution FROM * USING SQLite;
»
freie-welt.eu/de/1360575/Vid…
English
