Anya Skirko
34 posts


Anya Skirko
@u_feature
Blockchain Security Researcher









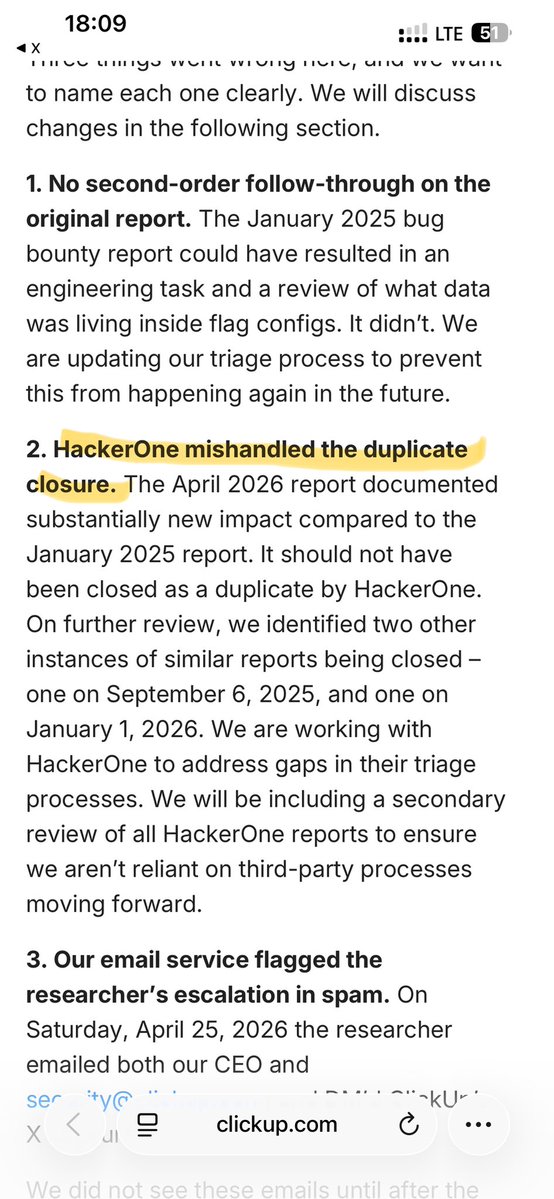


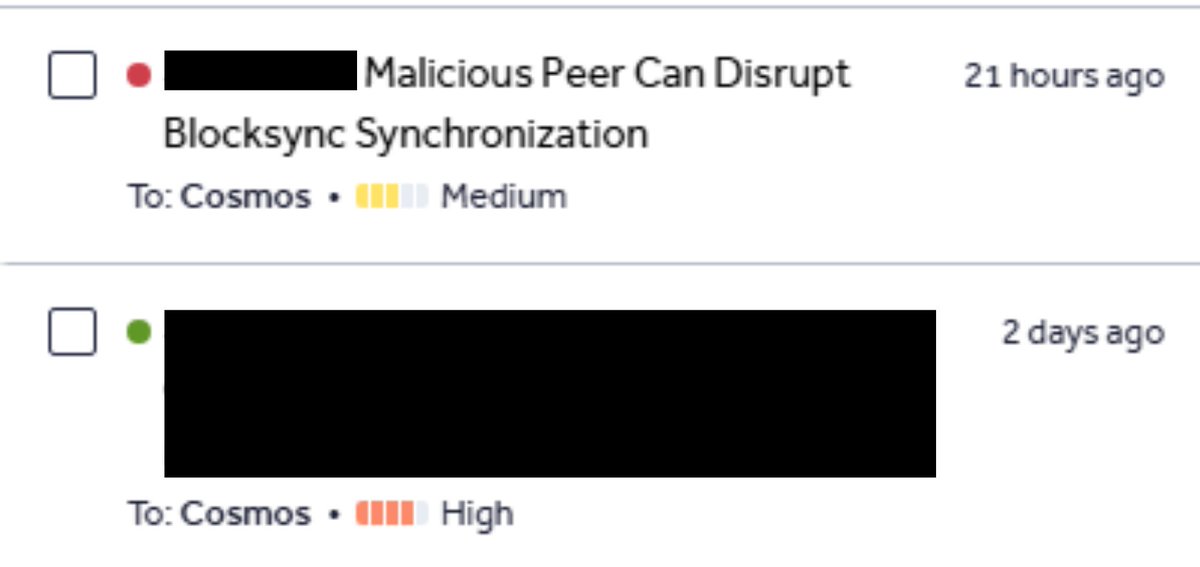
1. You reported 2 bugs to Cosmos. One Medium, and one High. You went with the escalation of Medium (not High) to the end. You disclosed it. If you were that confident about the High one you’d have escalated it instead. 2. Then after the escalation of the Medium, the vendor allegedly recognized the mistake on the other report and rewarded you with a bounty. While retaining the position with regards to the Medium one which already went public together with discrediting facts about their process which you shared. 3. There were no releases in cosmos-sdk, cometbft, evm, ibc-go, ibc-solidity-eureka, wasmd between the moment when the vendor stated they’ll review your reports and the moment your High report was closed with the bounty. Not clear where the fix went and where the advisory is. Please, share if the advisory was issued. It’s unlikely that the report was closed before the fix got implemented. And the vendor is required to publish the advisory since downstream projects need to update their dependencies. 4. The same day you got paid you dropped a discrediting post and edited the GitHub issue by removing all the facts that were pointing out at the vendor's irresponsible behavior. After that you interfered multiple times with my attempts to establish technical truth by continuously claiming “but the vendor’s assessment” and downplaying the impact. Which directly cancels your claim that “we share the same position on technical truth.” The vendor’s assessment remained the same. Nothing changed there. And as per your initial statement you cared about the community. This part has changed as you dropped discrediting evidence as soon as you received the payment. You surrendered your legitimate bug and you surrendered your credibility. You can’t make a way out of this via LLM-generated text that contradicts reality. It only proves my points.

@ehdus829 @cosmos Let's keep it here so everyone could see that @ehdus829 decision to drop the post wasn't influenced by money.