Usameen
11.3K posts


Usameen
@uptown_crypto
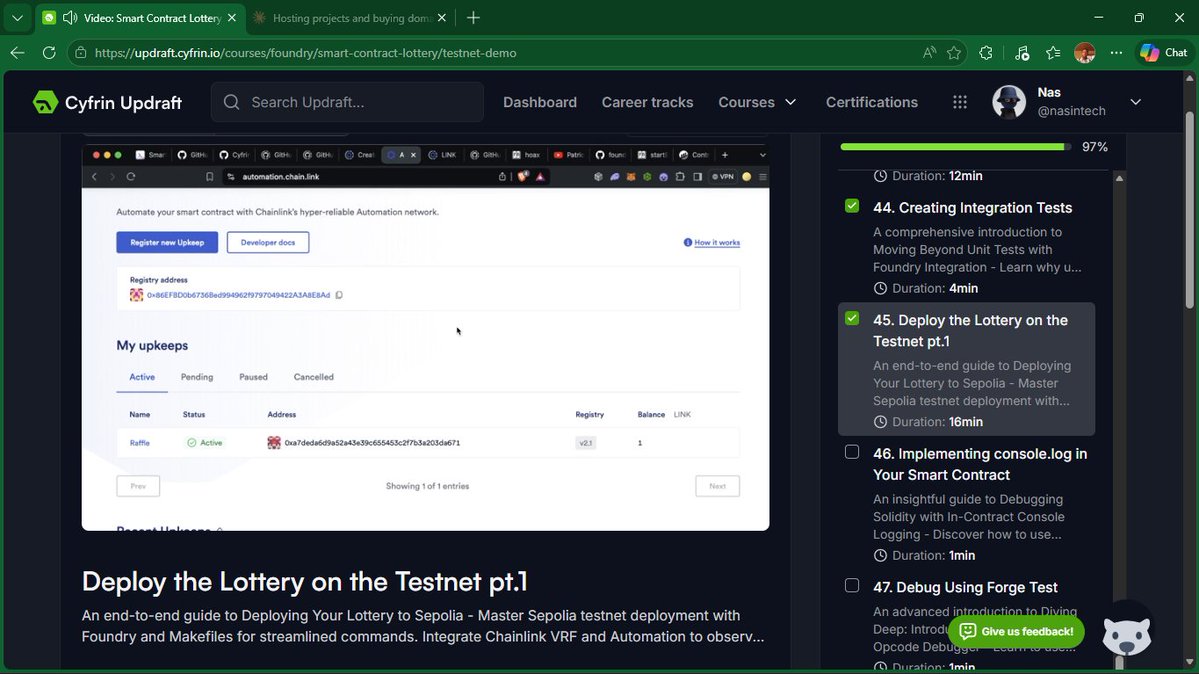
Trying to do better Learning Smart Contract Development & Security | Solidity & Vyper @CyfrinUpdraft | Documenting my journey in Web3
Kano, Nigeria Katılım Mayıs 2019
203 Takip Edilen385 Takipçiler
Sabitlenmiş Tweet


@Learnernoearner Thanks you for providing free signal and giveaway may God reward you
English
Usameen retweetledi

God abeg make i no kpai for "Rimin kebe" @uptown_crypto 😭😭
The Best@Thebestfigen
Entering Osaka via this highway should be considered a World Heritage Site. Japan is simply wonderful.
English

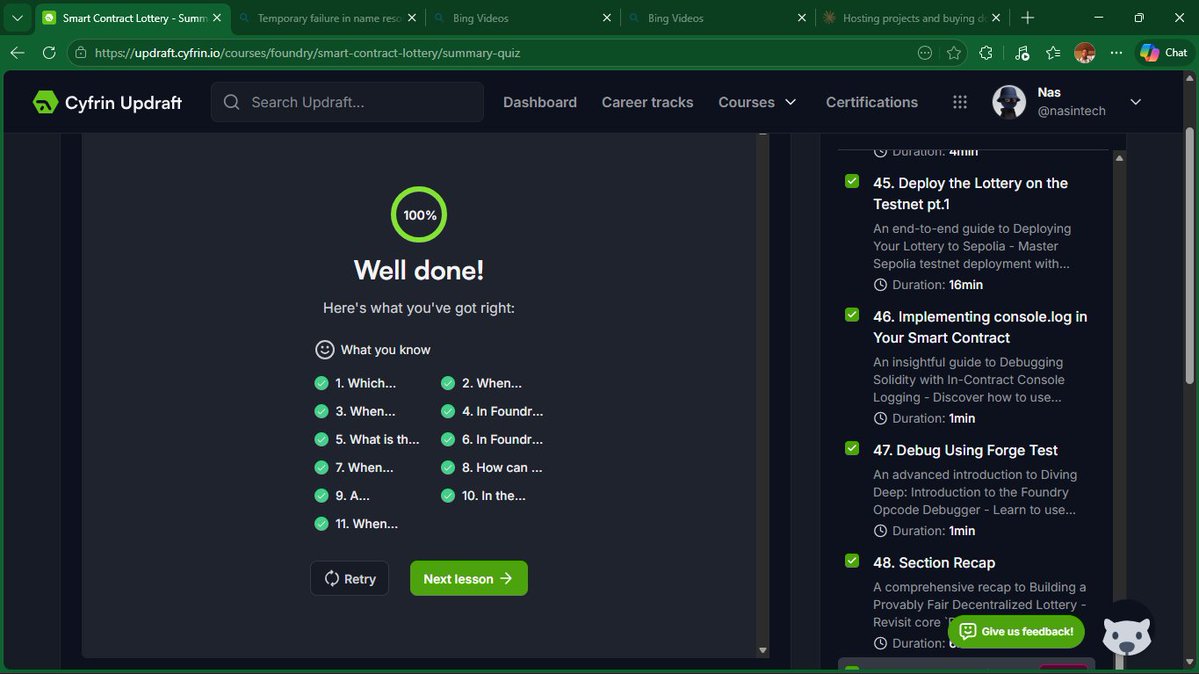
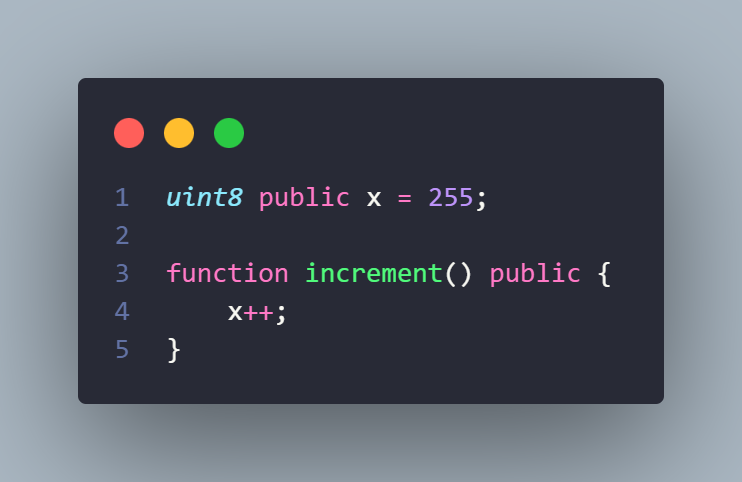
✅ QUIZ #6 ANSWER — C) The transaction reverts
Solidity 0.8.0+ reverts on overflow with Panic(0x11).
uint8 max = 255. 255 + 1 overflows uint8 → revert.
For wrap-around behaviour in 0.8.0+: 👇
Pre-0.8.0: answer was B (silent wraparound). This was the biggest 0.8.0 breaking change — SafeMath libraries are no longer needed.

English

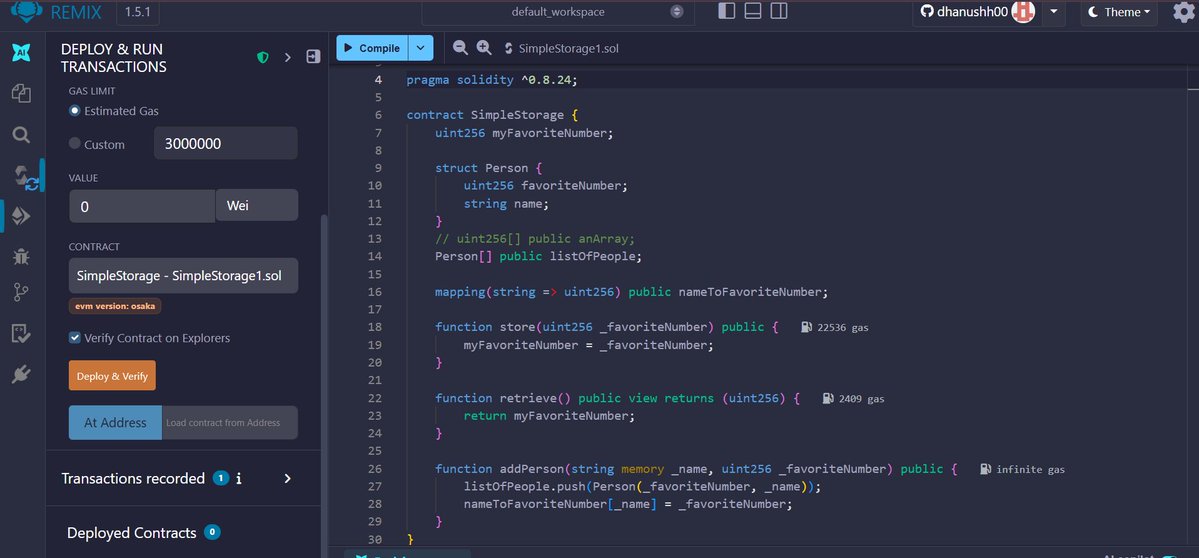
SOLIDITY QUIZ #6
What is the value of x after calling increment()?
A) 256
B) 0
C) The transaction reverts
D) Compiler error
Reply + explain why 👇Full answer in 24 hrs in comment section.
Solidity quiz will keep coming daily, my goal is to make sure every developer and auditor benefit from it.
English

Yeay, I was awarded for my first valid submission on
@HackenProof
hackenproof.com #hackenproofed #bugbounty

English
Usameen retweetledi
Usameen retweetledi
Usameen retweetledi

🔓 YESTERDAY'S BUG — REVEALED.
The vulnerability: integer overflow in increaseLockTime().
function increaseLockTime(uint256 secondsToAdd) external {
lockTime[msg.sender] += secondsToAdd;
}
In Solidity below 0.8.0, uint256 arithmetic wraps silently on overflow. An attacker exploits this to escape their time lock early:
Attack sequence:
1. User deposits. lockTime[attacker] = block.timestamp + 1 weeks
(roughly: 1,700,000,000 + 604,800 = 1,700,604,800)
2. Attacker calls increaseLockTime with:
secondsToAdd = type(uint256).max - lockTime[attacker] + 1
3. lockTime[attacker] overflows and wraps to 0
4. withdraw() checks: block.timestamp > 0 — TRUE
5. Attacker withdraws immediately, before their lock expires
This is an Ethernaut Level 15 challenge — it has caught many experienced developers off guard because the function name sounds protective. "Increasing" the lock sounds safe. But the arithmetic has no ceiling.
FIXED FUNCTION: 👇
This is why arithmetic boundaries always deserve explicit scrutiny — especially in functions users can call themselves.

0xZulkifilu 💎🥷@0xZulkifilu
🔴 SPOT THE BUG — This time-lock contract has a flaw that lets users escape early. A user can withdraw before their lock expires. How? This is a real Ethernaut challenge pattern. Drop your answer
English

Security researcher @Ehsan1579 just brought home $300,000 from a critical report via Immunefi.
He's absolutely on fire in 2026.
If you pledge $IMU behind him, you both earn $IMU when he finds more bugs:
immunefi.com/pledge/bpop232…

English
Usameen retweetledi

$1M+ milestone ✅ just in 90 days, bro is absolute beast & web3sec gem..
he is just getting started ig, 9months left i think $5M+ by the year end?
Immunefi@immunefi
Security researcher @Ehsan1579 just brought home $300,000 from a critical report via Immunefi. He's absolutely on fire in 2026. If you pledge $IMU behind him, you both earn $IMU when he finds more bugs: immunefi.com/pledge/bpop232…
English
Usameen retweetledi

I want to share something honestly in my early days, the one and only person I was learning from was @PatrickAlphaC
He’s incredibly smart, highly credible, and truly one of the most legit people in the space.
If you don’t know him yet, then you’re seriously missing one of the best voices in Web3.
If you’re looking for someone solid to learn from, he’s absolutely one of the best, especially if you’re a developer or you want to be.

English

@justice95441214 @icekied @NigeriaStories But this is single birth no matter how rich you're you have no power over this 🤷♀️ unless you want to kill the whole pregnancy
English

@icekied @NigeriaStories Was about asking same thing. Why always the poor?
English


@hamidonsolo Alhamdulillah may Allah see us through and may Allah bless you for this exceptional help you're doing for free
English

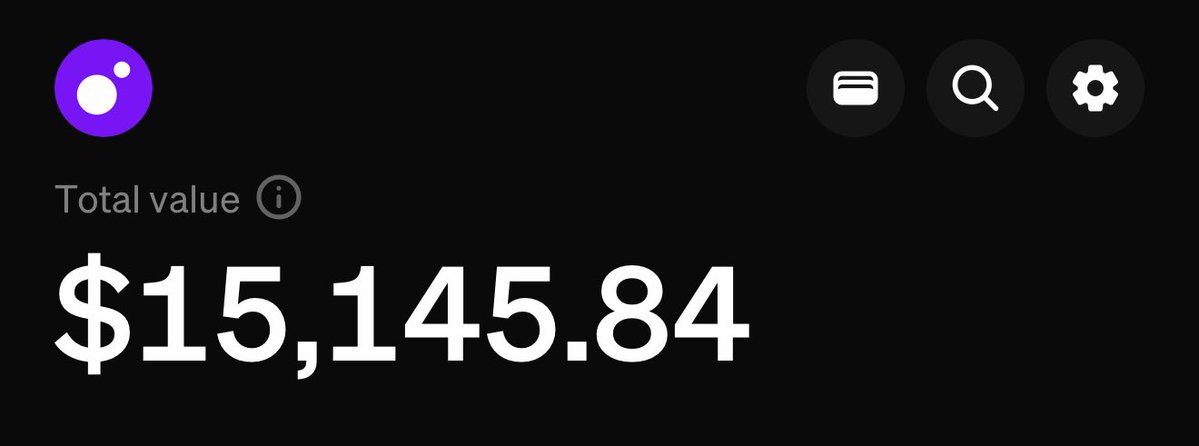
70% of people will scroll past this.
20% will save it and do nothing.
10% will go to the comments and drop a duaa 🤲 or a motivation quote.
That 10% gets personally from me:
→ Free registration link to my hacking course
→ Early waitlist access — 2,000 spots only
This is the exact methodology I used to go from $0 → $15,129 in 7 months.
19 years old. Morocco. No degree. No mentor. Just obsession.
I'm not selling anything.
I don't want your money.
I just want to make the world a little better than I found it.
discord.gg/PVaw2dZ5
Free. لله. No fees. No catch. Ever.
My full mission 👇
onehacker.space/mission.html
Now go to the comments.
Type a duaa. Type something that keeps you going.
Or stay quiet and don't blame God, don't blame life — look in the mirror.
🔁 RT — someone on your timeline needs this today

English
Usameen retweetledi

ETH is a commodity!!
Ft. @songadaymann
...But in this video, I'd like to bring your attention to something else.
English