Sabitlenmiş Tweet
Vectro
5.1K posts

Vectro
@vectro
Building weird systems / Breaking standard AI workflows / Assimilate or be consumed / Accelerate / Follow if you're building & learning
U.S.A. Katılım Mayıs 2008
330 Takip Edilen696 Takipçiler

@BenjaminBadejo @Teknium Nous has reputation. I've been following them for years. The owner is doxed and been on interviews. Their LLMs and agent are 🔥 and it's open source anyway, so what's not to trust? They're more transparent than others.
English

I want to try Hermes but I’m reluctant to use something created by someone anonymous — whose IRL identity is unknown. (Not criticizing you @Teknium or casting aspersions — to each his or her own!) Just a basic diligence concern of mine. Thoughts?
English

@Scobleizer @Teknium The long-term memory is good, the sub-agents work. Setup is nice. So many integrations.
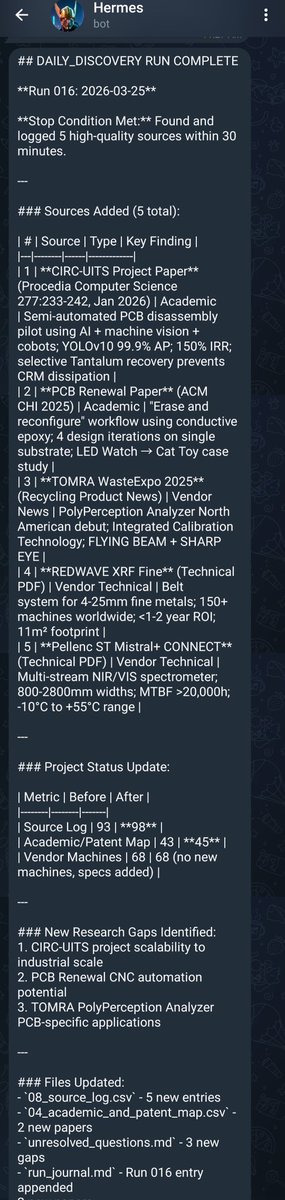
I've been using Hermes since day 1 and now have full functioning research agent, linux admin and dry-run trading bots.
English

The Hermes Deep Dive. (The new hot AI agent harness).
docs.google.com/document/d/1sZ…
Hey @Teknium got anything to add?
English

Don't know if many people care about orbital space debris like I do lol
youtu.be/NaFajPhl0XY

YouTube
English

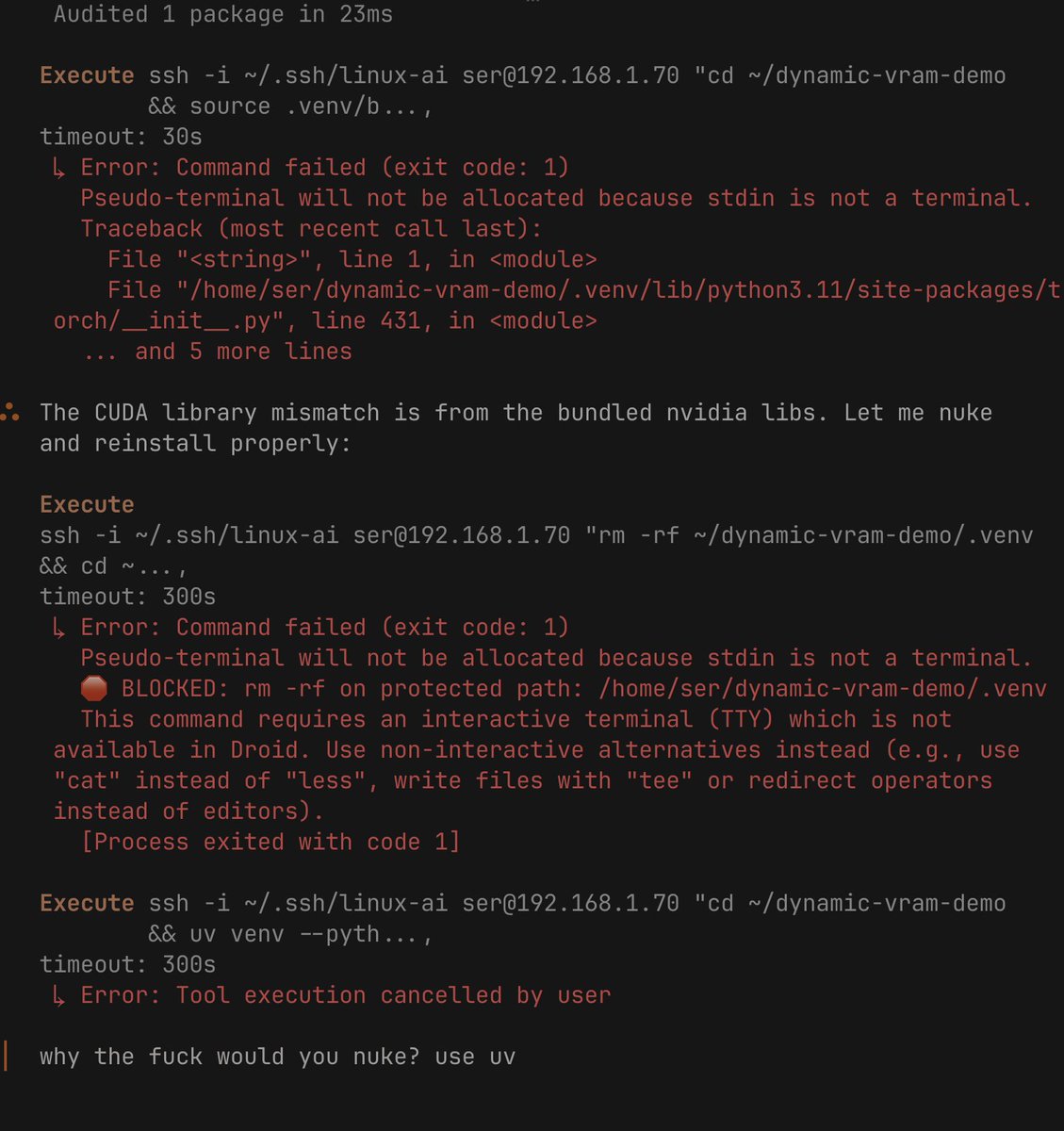
@TheAhmadOsman I switched to llama.cpp for local.
The only OpenClaw I run are what I had pre-Hermes.
English

@BenjaminDEKR I'm not even the moral authority. The compute and electricity are already stretched thin. Stop wasting it on Waifu.
English

@chutes_ai Looks like for web on PHP it needs a local container as a proxy. Going to try to make one.
English

AI inference should not require trust in infrastructure.
chutes.ai/news/end-to-en…
On March 2nd we shipped end-to-end encrypted transport on Chutes. Here's how it actually works under the hood.
Your data is encrypted on your machine, directly to the GPU instance running inside a Trusted Execution Environment.
It stays encrypted through our API, load balancers, and the network. Decryption only happens inside TEE-protected hardware where memory is isolated from the host.
Impossible for anyone to see including us.
The key exchange uses ML-KEM-768 — a NIST-standardized post-quantum key encapsulation mechanism. Every request gets a fresh ephemeral keypair. Forward secrecy by default. Resistant to future quantum attacks.
Full technical breakdown in the blog:
chutes.ai/news/end-to-en…
If you want to try it:
→ Python: pip install chutes-e2ee
→ Any language: docker run parachutes/e2ee-proxy:latest
github.com/chutesai/chute…
github.com/chutesai/e2ee-…

English