ゆ
314 posts


ゆ
@verd1c_
anti-cheats, mobile security, video games | @0tolerance_ctf 🇬🇷 🇳🇱
Amsterdam, The Netherlands Katılım Ekim 2014
259 Takip Edilen405 Takipçiler

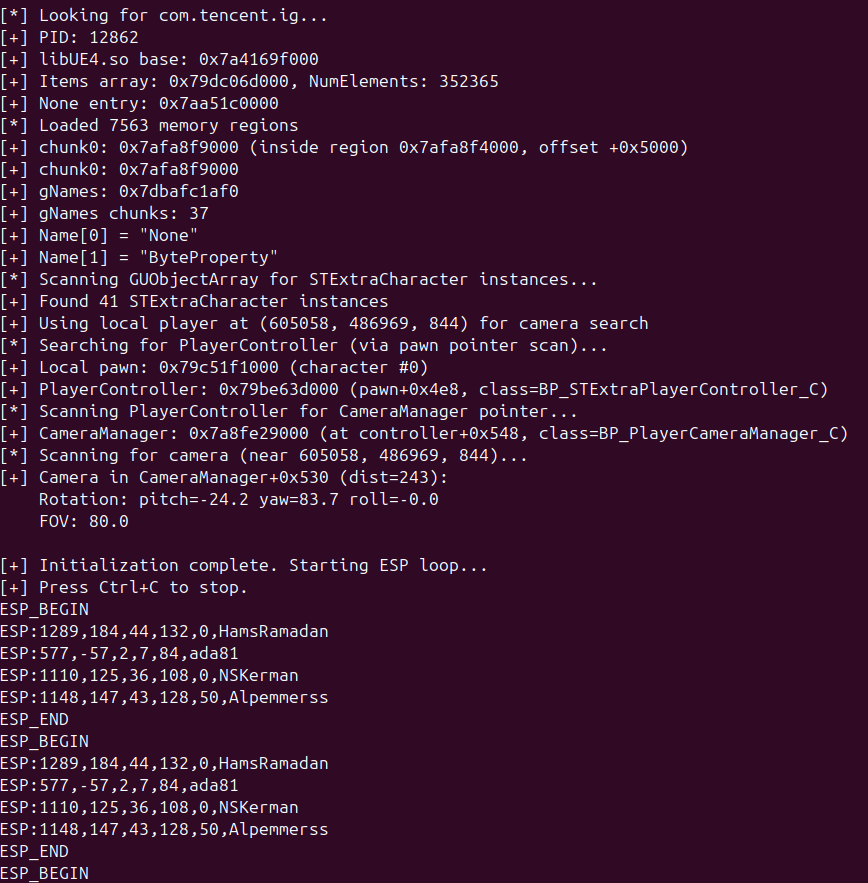
yeah it has this intl.anticheatexpert.com and its heavy obfuscated, but I don't think it cared much about the anticheat with this way of reading
It did also use Frida for the initial recon/reversing and bypassed the crashing detections which was just a /proc/self/maps read, so I expect it has more detections that do delayed bans instead of crashing
English

@verd1c_ @vmxoff @mottikraus finding offsets is impressive for sure, did it have access to dynamic analysis or only static?
English

@vmxoff @mottikraus undetected based on how my setup for mem reading is, not because I am not banned. The setup was given to claude as ready mcp tools, it didn't come up with it itself.
But regardless, my point was that it managed to find the offsets without any guidance, just with the right access
English

ไม่แนะนำให้ใช้นะโอกาศโดนแบน SSID สูงมากเพราะมันเป็น Internal อะ ถ้าอยากเล่นไม่โดนแบนไปใช้ Arduino ที่เป็น External เถอะ
ในเว็บพวก Unknowcheat แจกกันเต็มครับ อย่าเอา Token ไปใช้กับอะไรที่มันไม่เป็นประโยร์ช 5555555555555
ゆ@verd1c_
Turns out that given enough MCP tools for undetected process R/W without frida/hooking, Opus was able to oneshot an undetected ESP for PUBG mobile in a few hours :) Will write it up some time, definitely a new era in the anti-cheat cat & mouse game
ไทย

@skshadan_ Got something similar to work x.com/verd1c_/status…
ゆ@verd1c_
Turns out that given enough MCP tools for undetected process R/W without frida/hooking, Opus was able to oneshot an undetected ESP for PUBG mobile in a few hours :) Will write it up some time, definitely a new era in the anti-cheat cat & mouse game
English
ゆ retweetledi
ゆ retweetledi
ゆ retweetledi
ゆ retweetledi
ゆ retweetledi
ゆ retweetledi
ゆ retweetledi
ゆ retweetledi

BO6 has an interesting protection.
I noticed something weird when posting the screenshot of my previous tweet!
A 🧵

Maurice Heumann@momo5502
My emulator now manages to emulate larger parts of Call of Duty: Black Ops 6. It automatically uncovers some of the anti-debugging and anti-tampring techniques 🥳
English
ゆ retweetledi

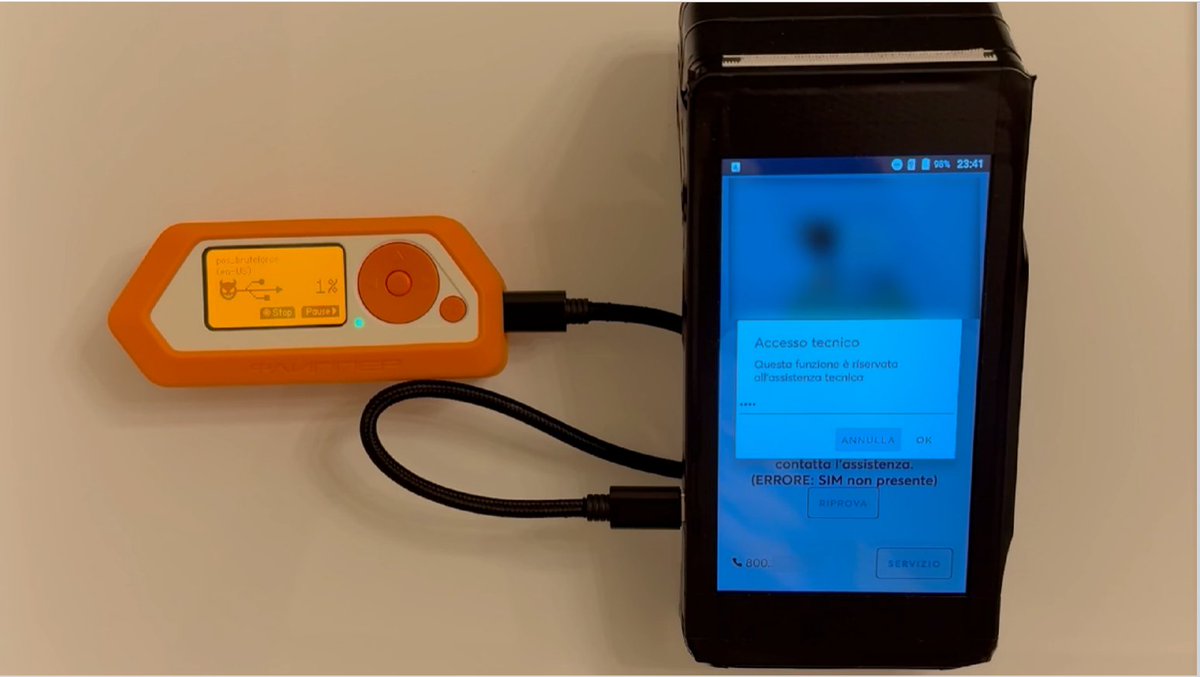
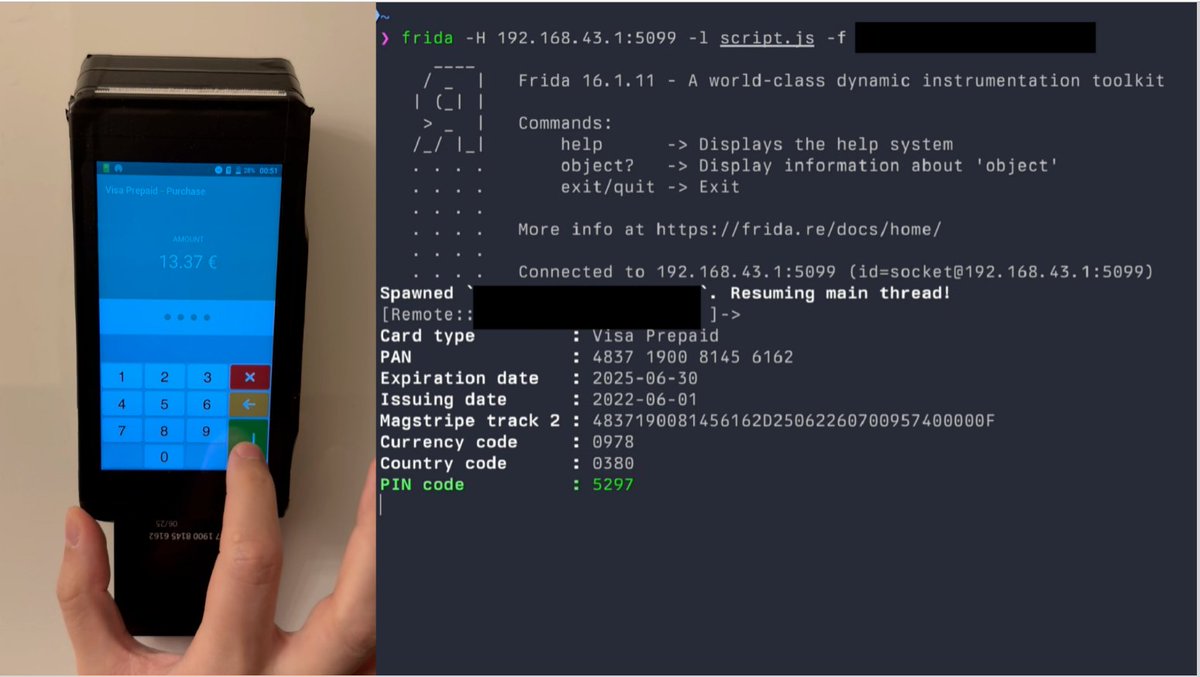
Rooting an Android POS "Smart Terminal" to steal credit card information:✅
Paper "Exploring and Exploiting an Android 'Smart POS' Payment Terminal", by Jacopo Jannone.Paying with a POS will never feel the same for me.
PDF: nohat.it/slides/2024/ja…
Video: youtu.be/a9BFGlxP71Y
YouTube
English
ゆ retweetledi
ゆ retweetledi