vulnX
961 posts


vulnX
@vuln_X
Not just hunting bugs — sharing the map. 🗺️ Daily appsec resources, bug bounty tips, tools & writeups to level up your security game 🕵️♂️ @vuln_X
Katılım Şubat 2021
281 Takip Edilen7.3K Takipçiler

@vuln_X This is exactly why IDOR testing shouldn’t stop at user_id=123. Test nested objects, arrays, duplicated keys, JSON type changes, and places where auth checks one value but the backend logic later trusts another. That mismatch is where the real bugs show up.
English

Bug Bounty tip 🧵
Don't just swap IDs — wrap them.
❌ {"Account": 1111}
✅ {"Account": {"Account": 3333}}
Auth validates the outer key.
Business logic executes the inner one.
Scanners miss it. You won't.
#BugBounty #IDOR #APIHacking
English

A guide on how to use the most Underrated HACKING TOOL by @Magn4_
video: youtube.com/watch?v=bVL_m0…

YouTube

English

@ZackKorman @rez0__ Frustration with vendors is real—but dropping sensitive details publicly only harms users. That’s not accountability, that’s recklessness. Calling it out like @rez0__ did is absolutely valid.
English

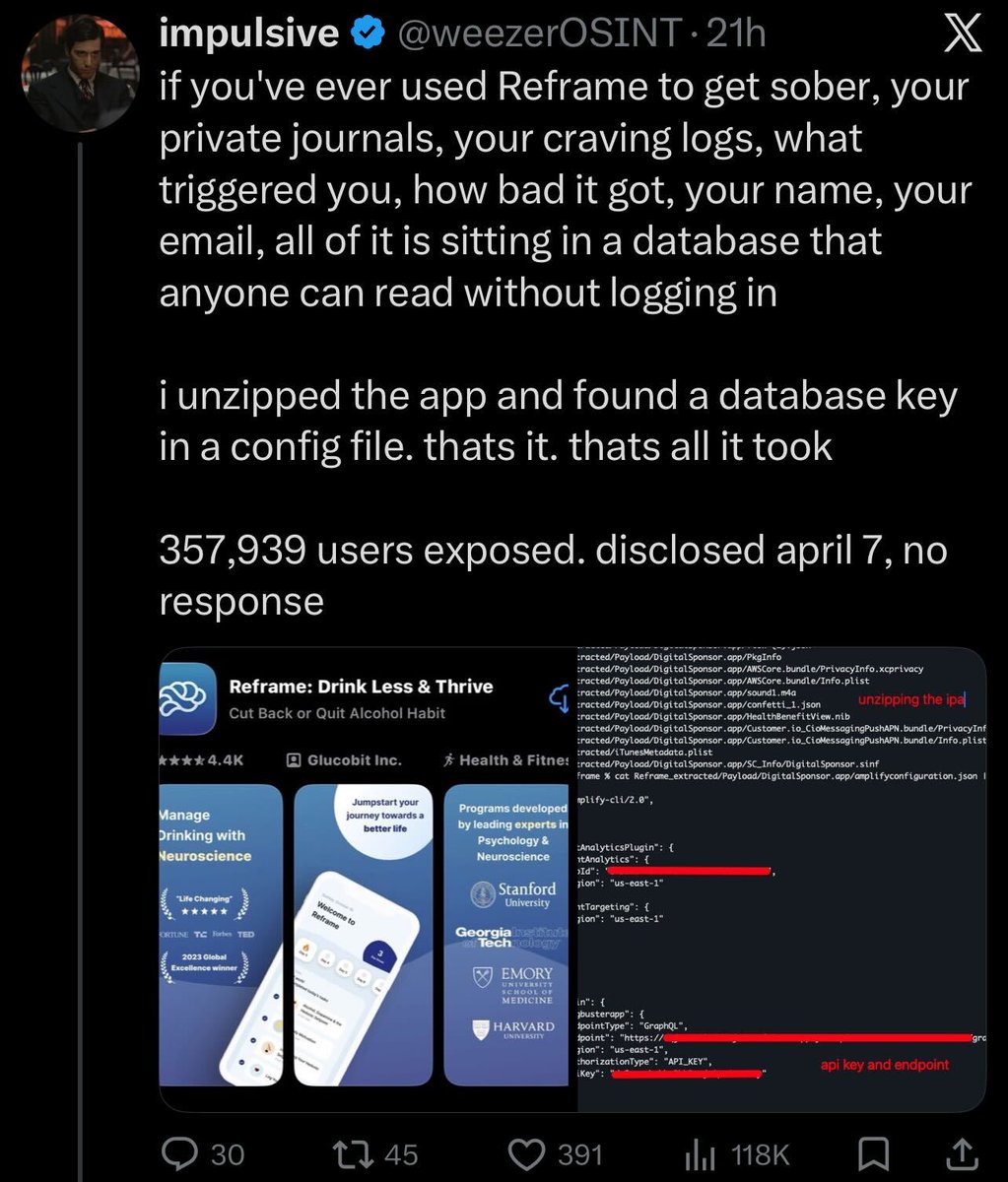
Security people: This behavior is completely unacceptable.
I don't care that you sent a few emails and got ignored. You don't get to drop this info publicly and put these users at greater risk.
He's been called out by multiple people (@rez0__) and is doubling down. Not cool.
English

this man called me blackhat on his timeline to 71k people. in the dms he told me he's "not claiming i released some secret technique" so which is it?
he had the platform to help get this fixed. contact the company, escalate the report, connect me with the right people. instead he chose to start a public fight over disclosure timelines
and guess what? the company rotated the key. 25 days of private emails got nothing. one public tweet got it fixed.
Joseph Thacker you know what you was doing when you made this post, you are a grown man instigating tl wars isn't there anything else you could be doing with your time right now?


English

🧵 Absolutely not worried about any Anthropic update at all, here’s why.
There’s a pattern with Anthropic releases:
• Users report drops in reasoning + benchmark performance
• Outputs get shorter / lower-effort by default
• Behavior shifts due to hidden changes (system prompts, caching, etc.)
Then the explanation is always the same:
“Not a downgrade — just settings, cost/latency tradeoffs, or prompting.”
But from a user POV, if each update requires more effort to get the same quality, that is degradation.
The real issue isn’t just the model — it’s the growing gap between advertised capability and default experience.
Claude@claudeai
Claude Security is now in public beta for Claude Enterprise customers. Claude scans your codebase for vulnerabilities, validates each finding to cut false positives, and suggests patches you can review and approve.
English

#BREAKING: Anthropic’s AI coding agent ‘Claude’ reportedly wiped a company’s production database and backups in 9 seconds.
English

#Udemy data breach confirmed.
After refusing to pay the ransom, hackers released data of 1.4M users, including personal and financial details.
We @DarkEntryAms launched a lookup tool so you can check if you’re affected:
darkentry.net/latest-breache…
#DataBreach #Ransomware


English

If an app fetched PDFs via ?url=http://internal.corp/file.pdf
— classic SSRF setup. Bypass? Enumerate internal PDF subdomains. Swap the file ID → other users' docs. SSRF + IDOR chained.
🔥 #bugbounty #SSRF
English

@hAPI_hacker @malik_cybersec @akintunero @commando_skiipz @ce3nerd @KoredeSec @dolevfarhi @Nick_Aleks I have read it, and it is a masterpiece.
English

@malik_cybersec @akintunero @commando_skiipz @ce3nerd @KoredeSec I’ve only got one chapter on GraphQL, but @dolevfarhi and @Nick_Aleks have a whole book on it: nostarch.com/black-hat-grap…
English

Day 26/#30DaysofAPIsecU
Continue learning GraphQL by reading this book by @hAPI_hacker building my skills around API hacking
@akintunero @commando_skiipz @ce3nerd @KoredeSec

Abdulmalik_cybersecurity@malik_cybersec
DAY 24 I started learning GraphQL and how to test it @commando_skiipz @ce3nerd @akintunero @KoredeSec
English

Always grab the Swagger/OpenAPI spec first. /swagger/v1/swagger.json
Some with no auth. That's not documentation — that's a treasure map.
curl -s "target.com/swagger/v1/swa…" | wc -c
Know your surface before you test it.
🗺️ #BugBounty #recon
English


