Sabitlenmiş Tweet

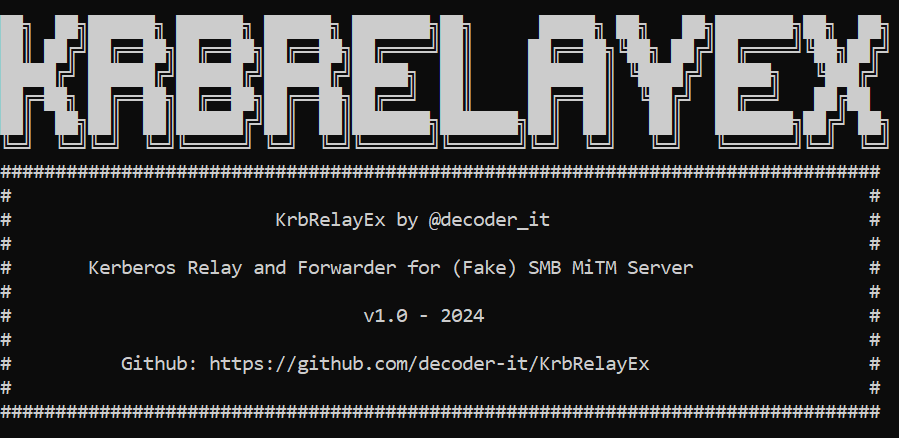
SharpADWS is an Active Directory Recon and
Exploit tool for Red Teams via the ADWS protocol, Inspired by @FalconForceTeam
Without the LDAP protocol, it can easily bypass most traffic monitoring for LDAP
#BloodHound #redteam #Pentesting #CyberSecurity
github.com/wh0amitz/Sharp…
English