Sabitlenmiş Tweet
xf0
19 posts


xf0
@xf0_st
You found xf0. Most people don't. - Threat Research
/dev/null Katılım Mayıs 2025
21 Takip Edilen9 Takipçiler

ShinyHunters has successfully hit the big leagues.
ShinyHunters successfully disrupting exams, schooling, grading, government funded research projects, dissertation work, graduations, financial aid, financial loss, potentially immigration complications, and more, has elevated this from "a silly shenanigan" to "major national security incident" and being labeled as an attack on United States critical infrastructure.
If I had to guess, the FBI, NSA, CIA, DIA, CISA, ICE, and DOE are all involved due to the disruption of this.
This isn't the largest extortion campaign I've seen, but this is definitely in the top ten. This is what the kids call a "Certified Hood Classic".
English

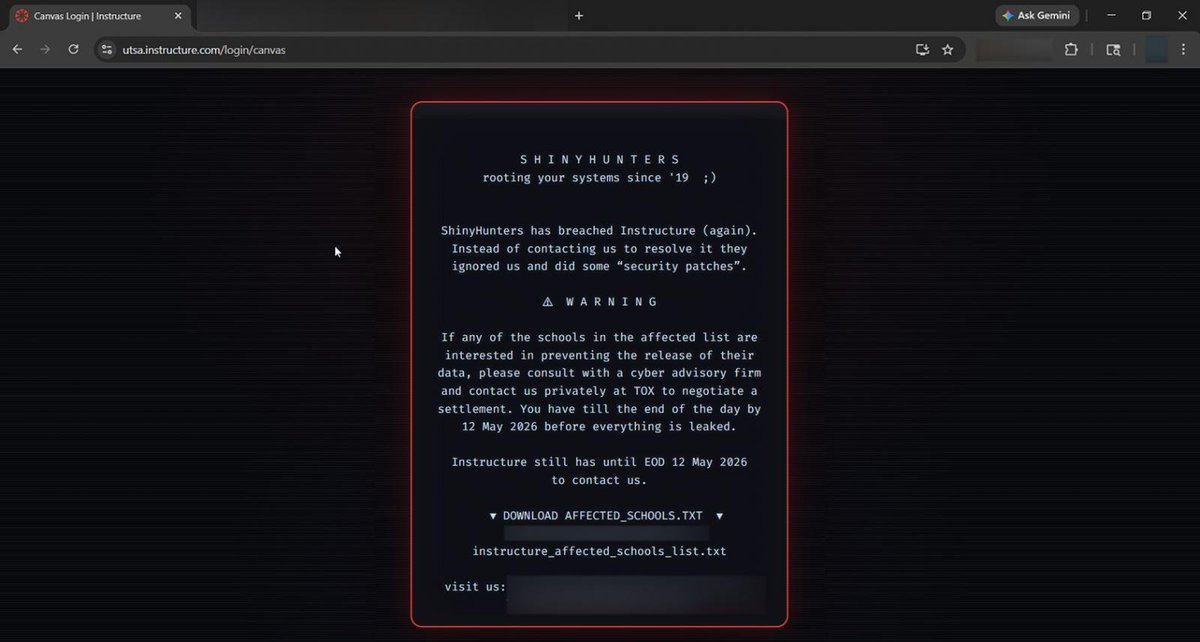
🚨 BREAKING: ShinyHunters defaced Canvas login portals for hundreds of colleges and universities today, replacing them with extortion demands tied to the recent Instructure breach.
Sources tell BleepingComputer that the hackers exploited another unpatched vulnerability in Instructure’s systems, allowing them to hijack approximately 330 Canvas portals and display ransom messages to students and staff.
What happened:
🔴 Canvas login portals were replaced with ShinyHunters extortion messages
🔴 The messages warned schools to negotiate before May 12 or student data would be leaked
🔴 The defacements also appeared inside the Canvas mobile app
The portals were visible for about 30 minutes before being taken offline as Instructure responded to the incident.
This follows last week’s breach where ShinyHunters claimed to have stolen 280 million student and staff records tied to thousands of schools using Canvas.
English

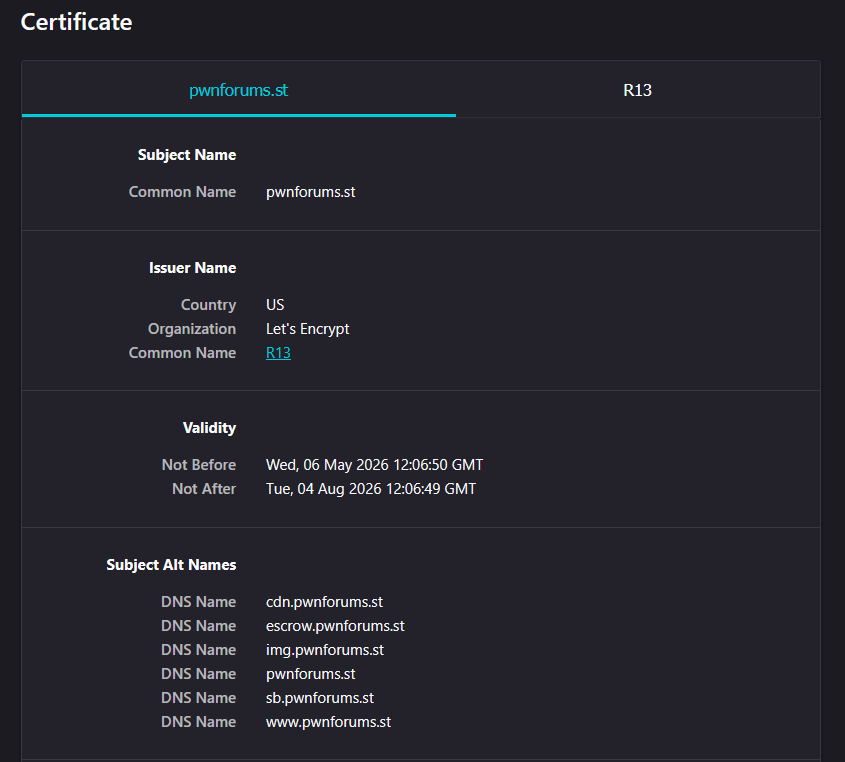
@CarTalkYumeship @DarkWebInformer That is because the owner is aligned with the federal government. Due to this, he has immunity by handing over any logs to the authorities if requested.
English

@DarkWebInformer Notice how Hackforums never has to deal with this
English

@discord_support
So you terminate my account with no warning 1 day after I purchase Nitro, then you say I have been suspended for violent content and fraud? Please get in contact with me to help me fix this. At least show me evidence.
English
xf0 retweetledi