zayooko retweetledi

KeePwn: automate KeePass discovery and secret extraction securityonline.info/keepwn-automat…
English
zayooko
25 posts






🚨 We discovered 3 vulnerabilities in Microsoft Message Queuing (MSMQ) service, including #QueueJumper (CVE-2023-21554), a Critical vulnerability that could allow unauthorized attackers to remotely execute code. More details in our blog 👉 research.checkpoint.com/2023/queuejump… #PatchNow


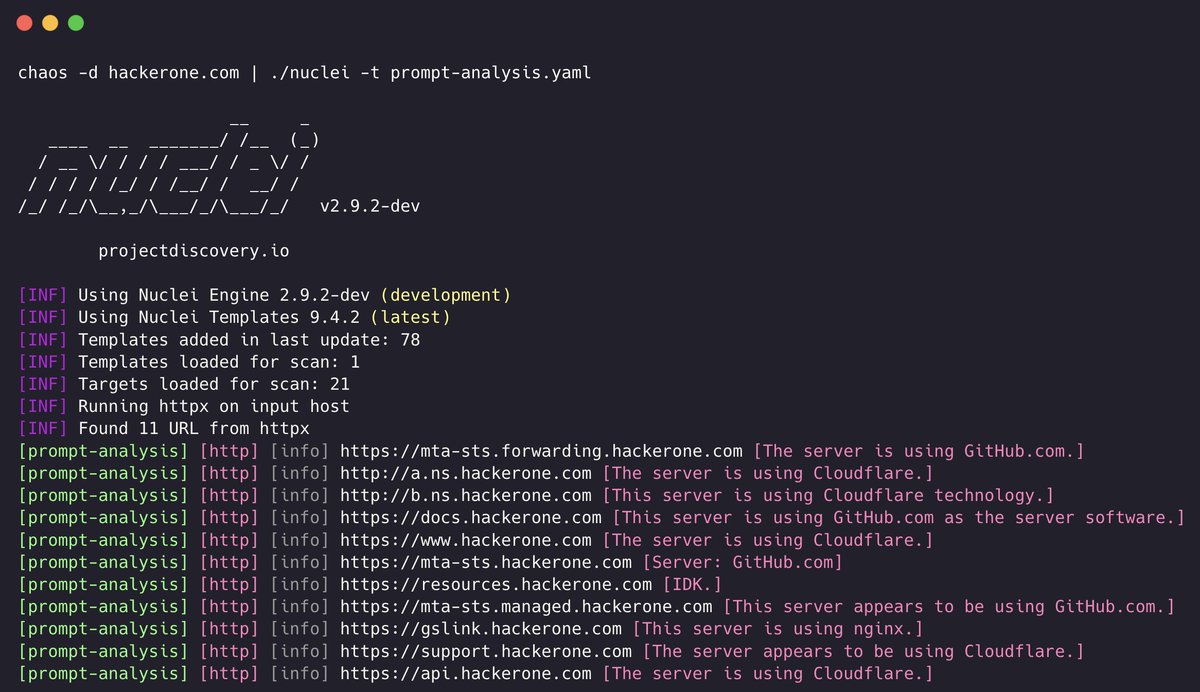

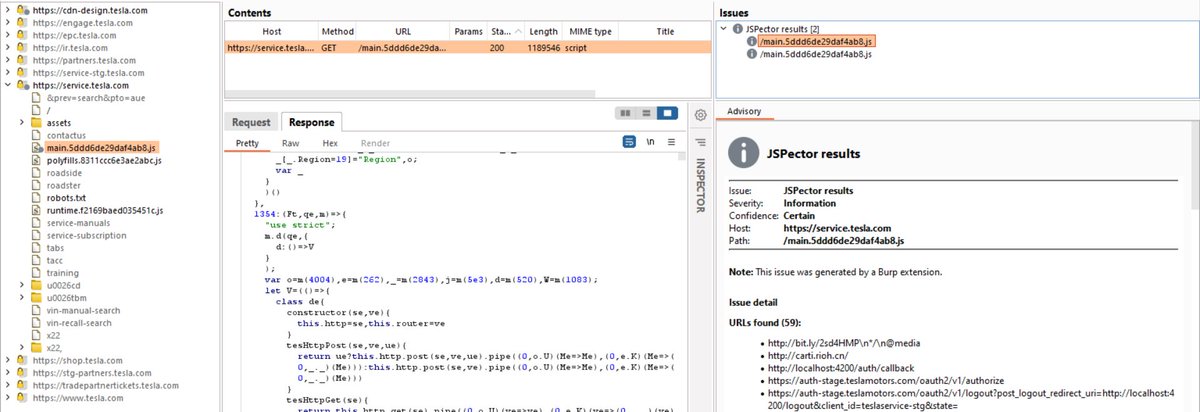
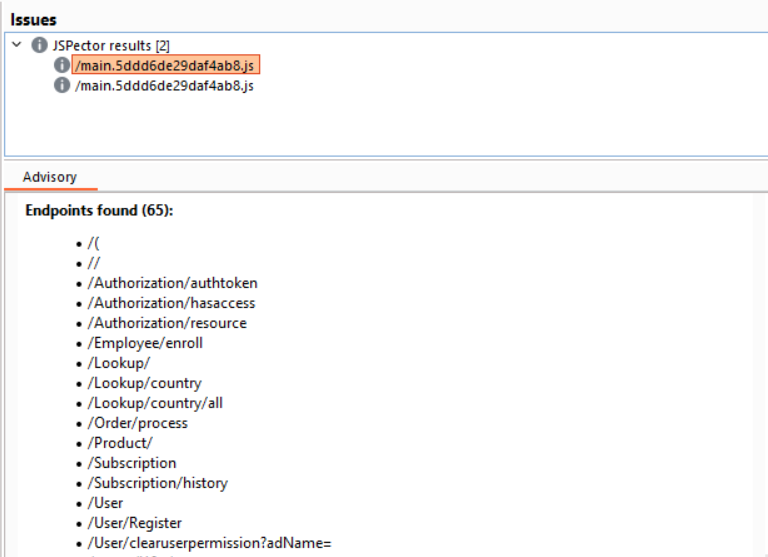
ALERTX Very fast #go tool for search subdomains. For example, it fin 111 tesla.com subdomains in 0.003 seconds. github.com/projectdiscove… Creator @pdiscoveryio