zer0phat retweetledi

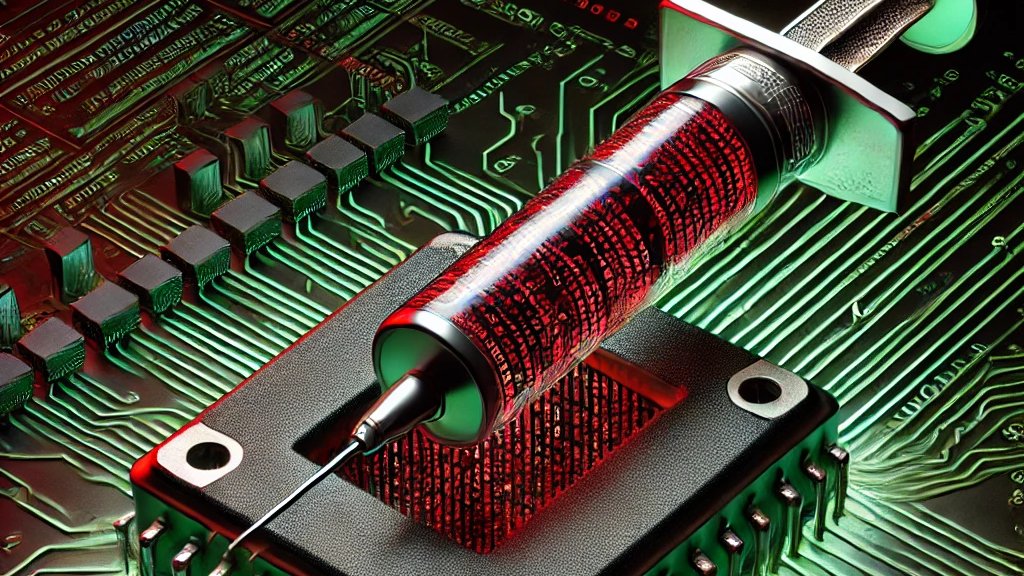
💻 ModuleOverride – Changing a Tyre Whilst Driving – @zer0phat & @kreepsec teach process injection using existing memory sections to run malicious shellcode. Hands-on demos and detection strategy discussions at @redteamvillage_ during @defcon 33! ⚡

English