Zero Day Engine
18 posts

Zero Day Engine
@zerodayengine
Zero Day Engineering Supplies • Private Intelligence: @zerodayalpha • Community: https://t.co/ASQmvN9Jz4
Katılım Haziran 2021
50 Takip Edilen2.3K Takipçiler
Sabitlenmiş Tweet

Analysis of VMware vCenter heap overflow vulnerability exploited at Matrix Cup competitions in China, June 2024 (CVE-2024-38812):
blog.sonicwall.com/en-us/2024/10/…
Another one in same code, 2023:
blog.sonicwall.com/en-us/2023/12/…
** Both are RCE to management console, not a hypervisor VM escape!
English

Interestingly, the elevation of privilege part of the chain is still not known
Tracker issue🔒 issues.chromium.org/issues/3561969…
English

[Browser Exploitation] Insightful little analysis of v8 CVE-2024-7965: bi.zone/eng/expertise/…
PoC: github.com/bi-zone/CVE-20…
Logic bug in Turbofan's "sea of nodes" IR implementation allows for OOB array access!
Exploit in-the-wild reported by Google & CISA on 26th August 2024
English
Zero Day Engine retweetledi

Slides: "Fuzzing from First Principles": zerodayengineering.com/research/slide…
I heard that the podcast reached all-time-highest number of viewers, thank you for coming to see me!

English
Zero Day Engine retweetledi

(CVE-2024-3914)[330759272][Pwn2Own 2024][DOMArrayBuffer]DOMArrayBuffer confused about ownership of backing buffer -> UAF is now open with PoC and exploit
issues.chromium.org/issues/3307592…
PoC:
issues.chromium.org/action/issues/…
Exploit:
issues.chromium.org/action/issues/…
WP:
issues.chromium.org/action/issues/…
@0x10n
xvonfers@xvonfers
(CVE-2024-3914)[330759272][DOMArrayBuffer]UAF in v8. "Removing this newly introduced CHECK to be able to merge fixes in this area - we still violate this invariant but the fixes are a step into the right direction."😅 chromium-review.googlesource.com/c/chromium/src… chromium-review.googlesource.com/c/chromium/src… @0x10n
English

Short and to the point, patch analysis + PoC of Windows Kernel ntoskrnl LPE bug (CVE-2024-38106), by @b1thvn_: pixiepointsecurity.com/blog/nday-cve-…
This bug is being exploited in-the-wild, as part of a browser exploit chain with Chrome v8 RCE (CVE-2024-7971), reported in August 2024
English
Zero Day Engine retweetledi

0-Day Insights - Deep Dive: Qualcomm MSM Linux Kernel & ARM Mali GPU 0-day Exploit Attacks of October 2023 zerodayengineering.com/insights/qualc… (by @alisaesage)
English

Tracking bug for v8 the_hole bug class mitigations bugs.chromium.org/p/chromium/iss…
English
Zero Day Engine retweetledi

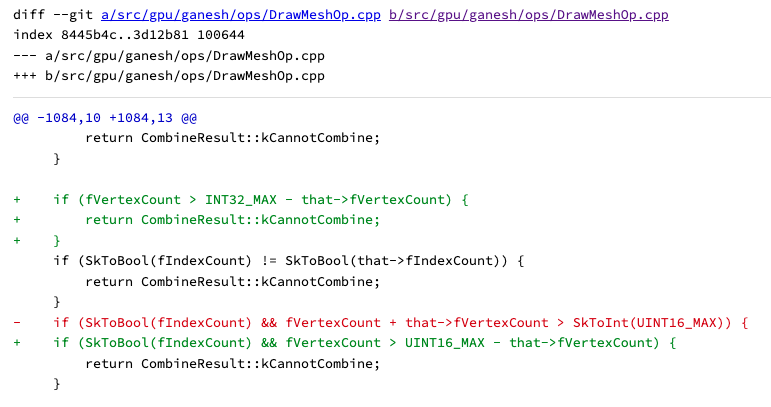
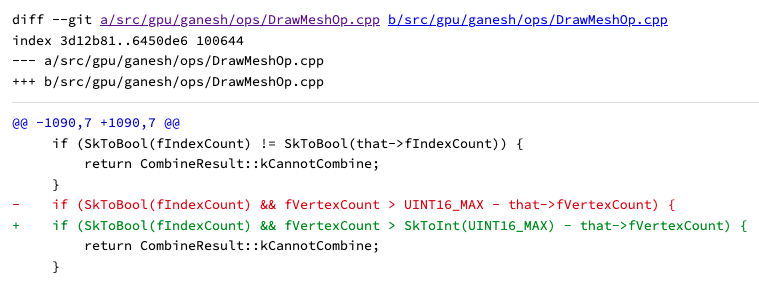
Research insights on recent Chrome 0day in Skia (CVE-2023-6435) from our lab:
1. The bug is an integer overflow in Skia, an open source library for rendering 2D graphics which which is used in Chromium backend.
2. The bug can be used to escape browser sandbox in Chrome app on Android.
3. At least one more bug -in one of the renderer subsystems, such as v8- is required to complete the attack with a full chain exploit. Google did not disclose the other bug at this time.
4. The bug cannot be used to achieve a full sandbox escape on common desktop deployments of Google Chrome.
5. Based on the above, we hypothesize that the original 0day attack vector and the exploit chain was targeting Android devices specifically.
6. The bug seems to be available and reachable in broad-scope Chromium (including common desktop deployments of Chrome browser), but an additional 3rd vulnerability would be required to execute arbitrary code with the same level of privilege as in the original 0day attack in most popular deployment configurations. Therefore, overal impact of the bug is somewhat scoped.
7. The bug will strongly affect Chrome embedders which use unsandboxed GPU process. We did not look further into this, but Chrome-based systems such as electron framework and derivatives should be patched quickly.
8. The bug is not explicitly related to the previous 0day in Skia (CVE-2023-2136).
I.e. it's not a patch bypass of the latter, and not located in the same subsystem of code.
9. Both bugs (6435 and 2136) are focused on bypassing in-code checks, which implicitly suggests the same specialized bughunting workflow, and therefore, possibly the same attacker.
10. The bug is not very trivial to reproduce. Strong familiarity with GPU-level graphics internals is required.
Chrome release notes: chromereleases.googleblog.com/2023/11/stable…
Patchset: skia.googlesource.com/skia.git/+log/…
Issue tracker (restricted): crbug.com/1505053
Analysis by @alisaesage
English

Chromium [WIP] internal fuzzing map by source code directory, official dashboard analysis.chromium.org/coverage/p/chr…
English

Chromium Mojo & IPC internals keyou.github.io/blog/2020/01/0… by keyou (in Chinese)
English

List of Chromium security bugs (with technical details) that received top bounty rewards from Google VRP: bugs.chromium.org/p/chromium/iss… Congrats to bug finders!
English

Another #itw0days discovered by @_clem1! CVE-2023-3079 in v8. Patch released by Chrome within 4 days of report!
chromereleases.googleblog.com/2023/06/stable…
English

⚠️ #CVE-2023-3079 has also been added to the Known Exploited Vulnerabilities Catalog. More at go.dhs.gov/Z3Q
CISA Cyber@CISACyber
🚧 @CISAgov added #CVE-2023-33009 & CVE-2023-33010 to the Known Exploited Vulnerabilities Catalog. Keep up with 🆕 additions & protect yourself from a malicious #cyberattack. More at: go.dhs.gov/Z3Q #cybersecurity #InfoSec #VulnerabilityManagement
English

Latest In-The-Wild Google Chrome V8 type confusion vulnerability (CVE-2023-3079) is patched[1] by fixing store handler selection for arguments objects [2] during inline caching [3]:
1- chromium.googlesource.com/v8/v8.git/+/e1…
2- developer.mozilla.org/en-US/docs/Web…
3- mathiasbynens.be/notes/shapes-i…
English

Some quick notes about the CVE-2023-3079(V8 type confusion), no PoC yet.
gist.github.com/MaxBWMinRTT/bd…
English