zolutal retweetledi

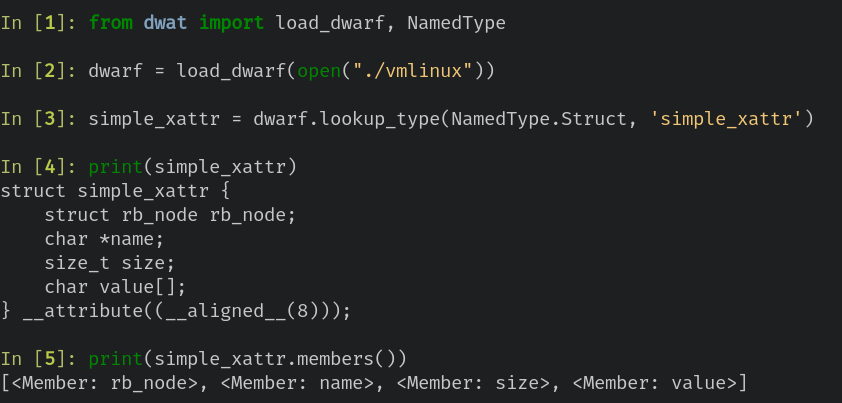
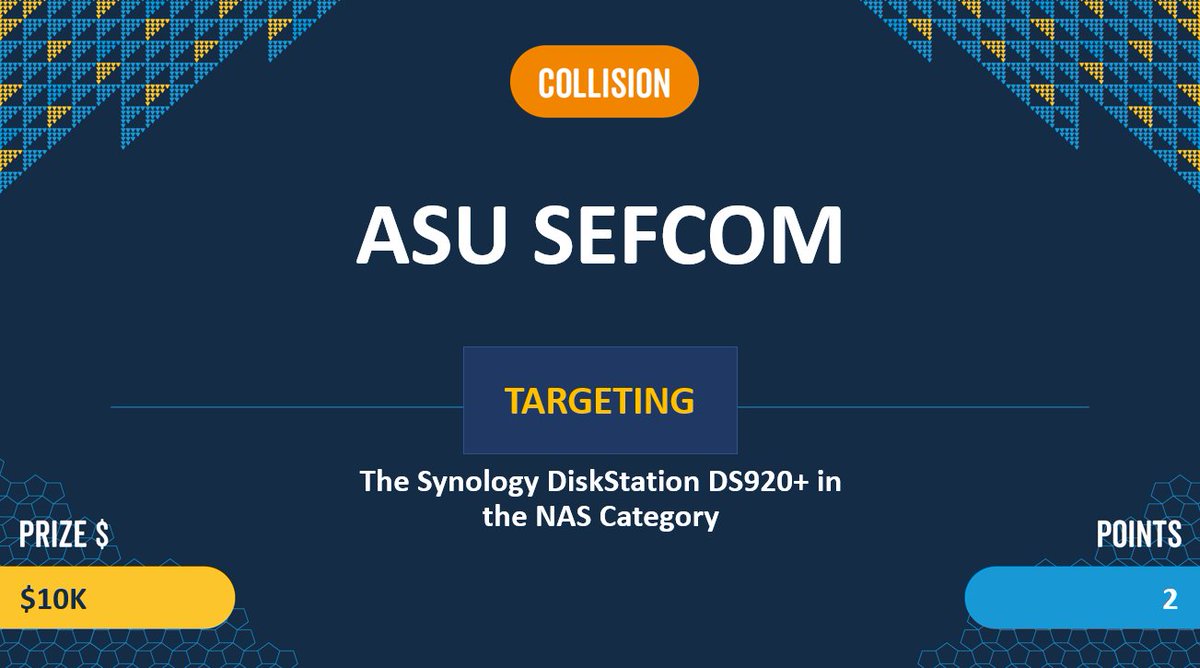
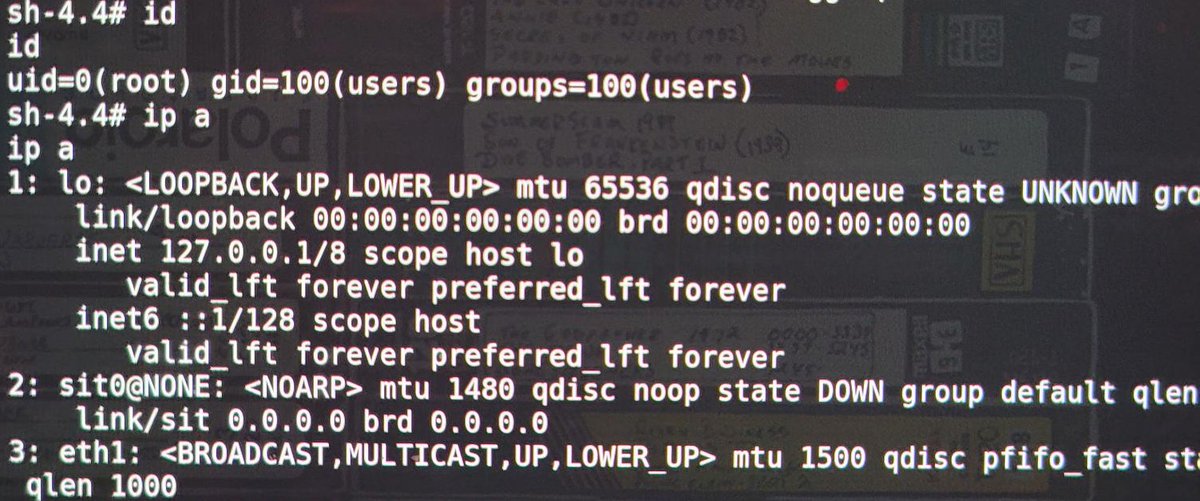
AI Cyber Challenge Semifinal Competition results are in! Congratulations to the top seven scoring teams who will advance to finals, and to all the competitors who worked to help safeguard the code that underpins critical infrastructure. More: darpa.mil/news-events/20…

English