
Anonymous Quant
656 posts










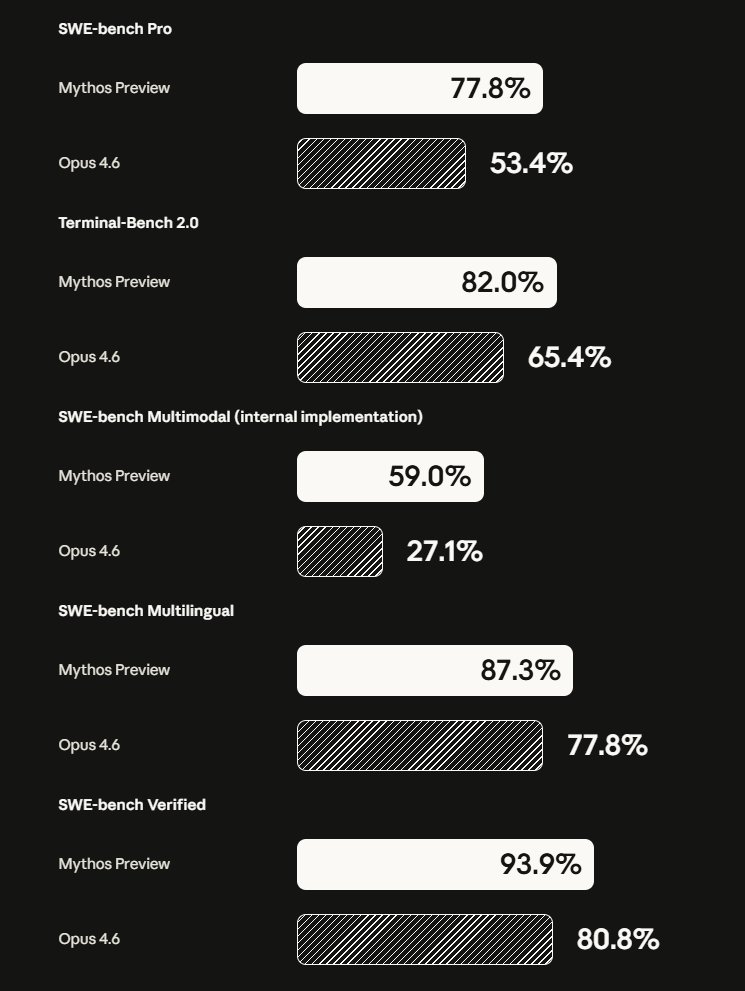
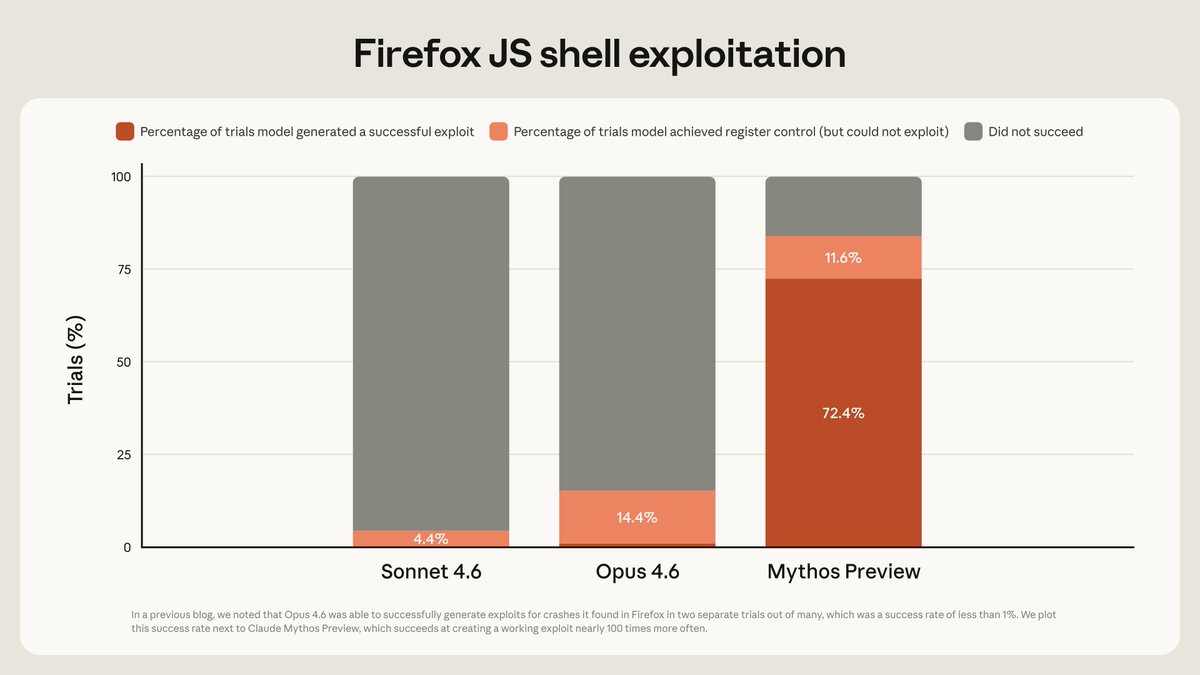
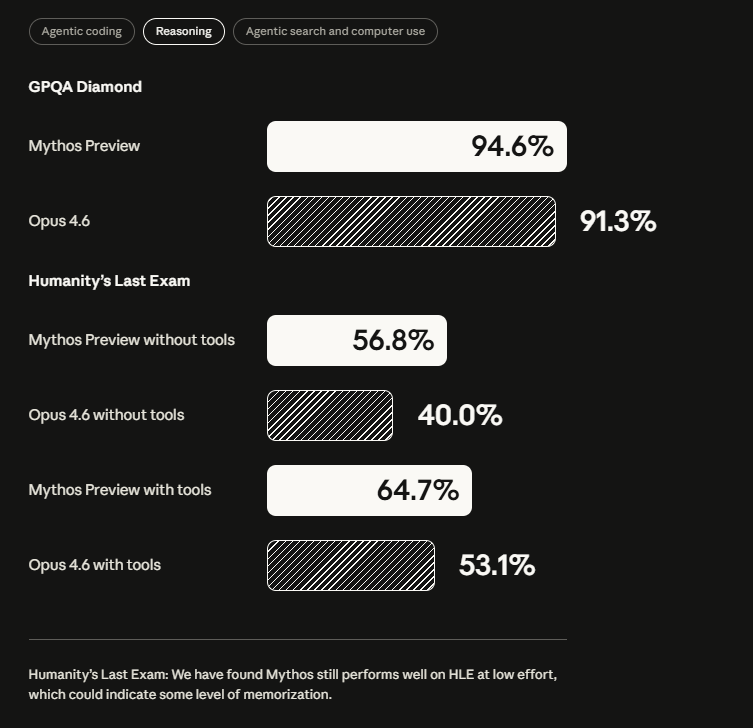

MYTHOS BENCHMARKS, OFFICIAL. HOLY MOLY Anthropic cooked!!


Claude Mythos can launch Vivado, create a project, compile synthesize and check its sims in Synopsys VCS all on its own. Wild.








🚨 CRITICAL: Active supply chain attack on axios -- one of npm's most depended-on packages. The latest axios@1.14.1 now pulls in plain-crypto-js@4.2.1, a package that did not exist before today. This is a live compromise. This is textbook supply chain installer malware. axios has 100M+ weekly downloads. Every npm install pulling the latest version is potentially compromised right now. Socket AI analysis confirms this is malware. plain-crypto-js is an obfuscated dropper/loader that: • Deobfuscates embedded payloads and operational strings at runtime • Dynamically loads fs, os, and execSync to evade static analysis • Executes decoded shell commands • Stages and copies payload files into OS temp and Windows ProgramData directories • Deletes and renames artifacts post-execution to destroy forensic evidence If you use axios, pin your version immediately and audit your lockfiles. Do not upgrade.


Mid term drawdowns produced 100% win rate returns 1 year out $SPY



damn this is so good and encapsulates everything I've been seeing/saying in the last few months - a spec that is sufficiently detailed to generate code with a reliable degree of quality is roughly the same length and detail as the code itself - so don't review those things, just review the code at that point, if you care enough about that level of abstraction - unless you're vibing side projects or prototypes (yes, even zero-to-one software), you ABSOLUTELY SHOULD care about the code at that level of abstraction - you need to find SOME way to get more leverage over coding agents though, because just reading all that code is a pain, esp when a lot of it is slop - the default/dare-i-say-decel way is to go back to "i own the execution, and give little things to the agent, check it along the way" - the accel-but-safe-way is to find something - NOT A SPEC (the word "spec" is broken anyway) - NOT 3 INVOCATIONS OF AskUserQuestion - that lets you resteer the model *before* it slops out N-thousand LOC













