Tweet fixado

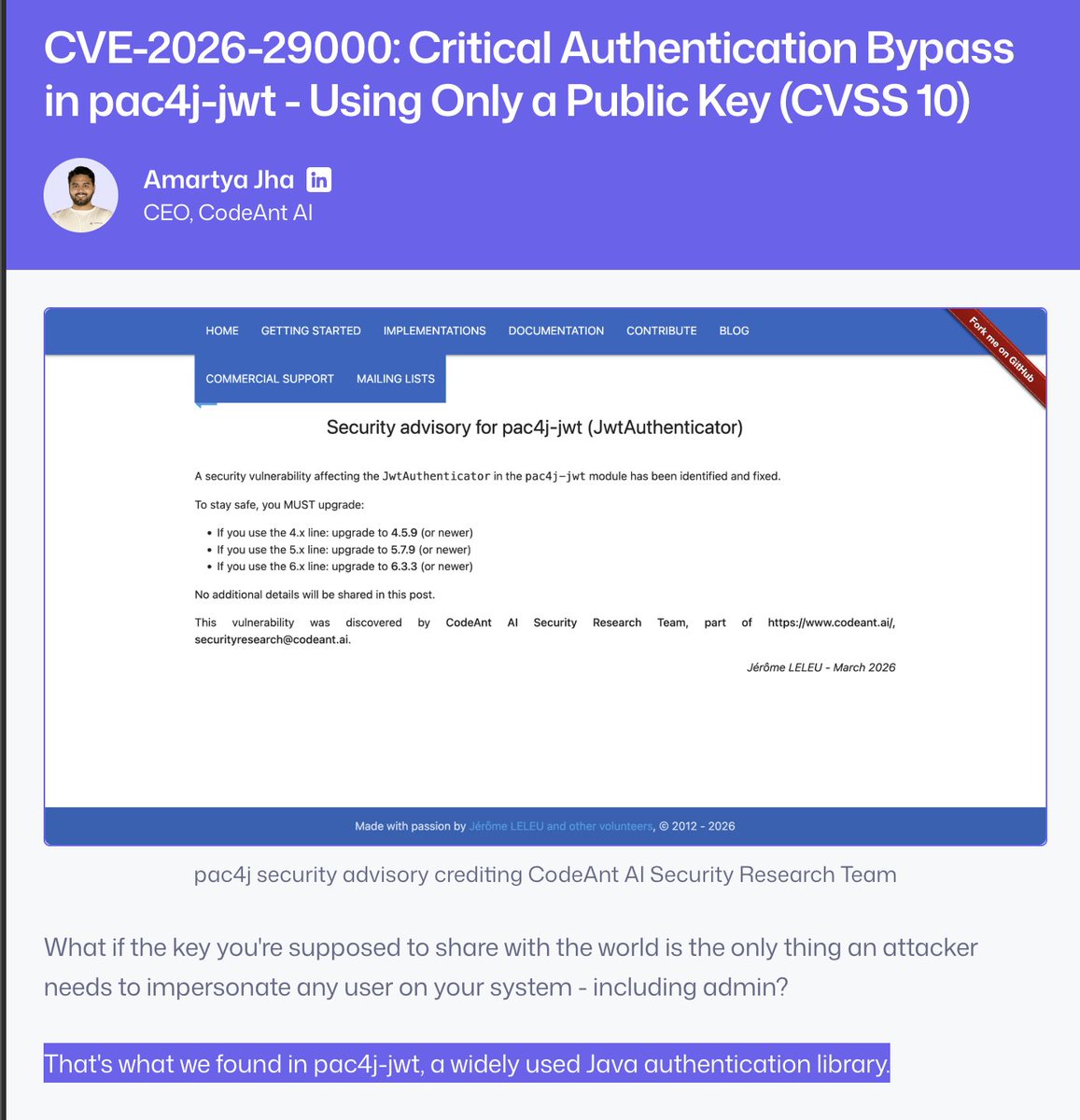
Our AI Code Review just found a CVSS 10.0 vulnerability.
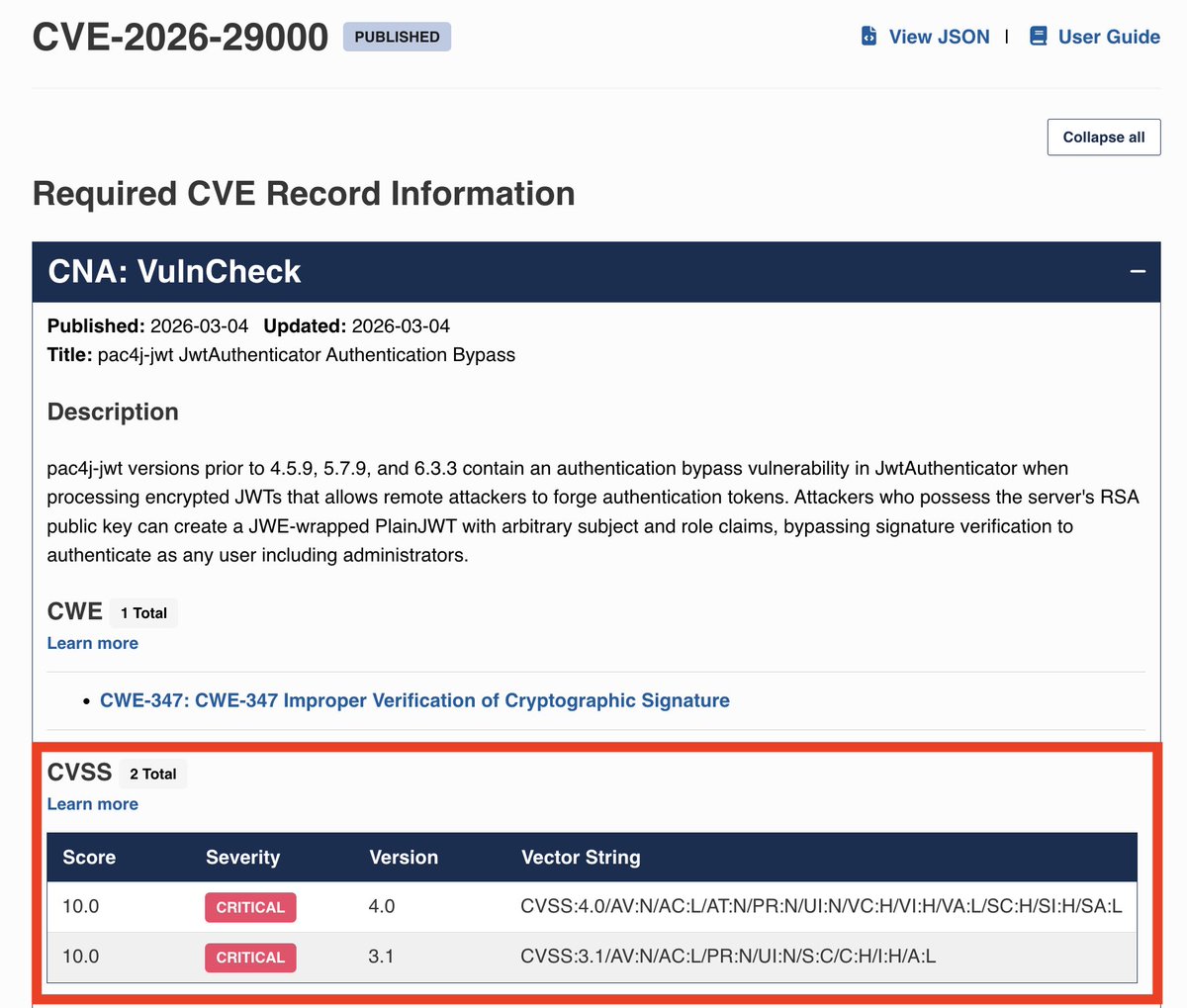
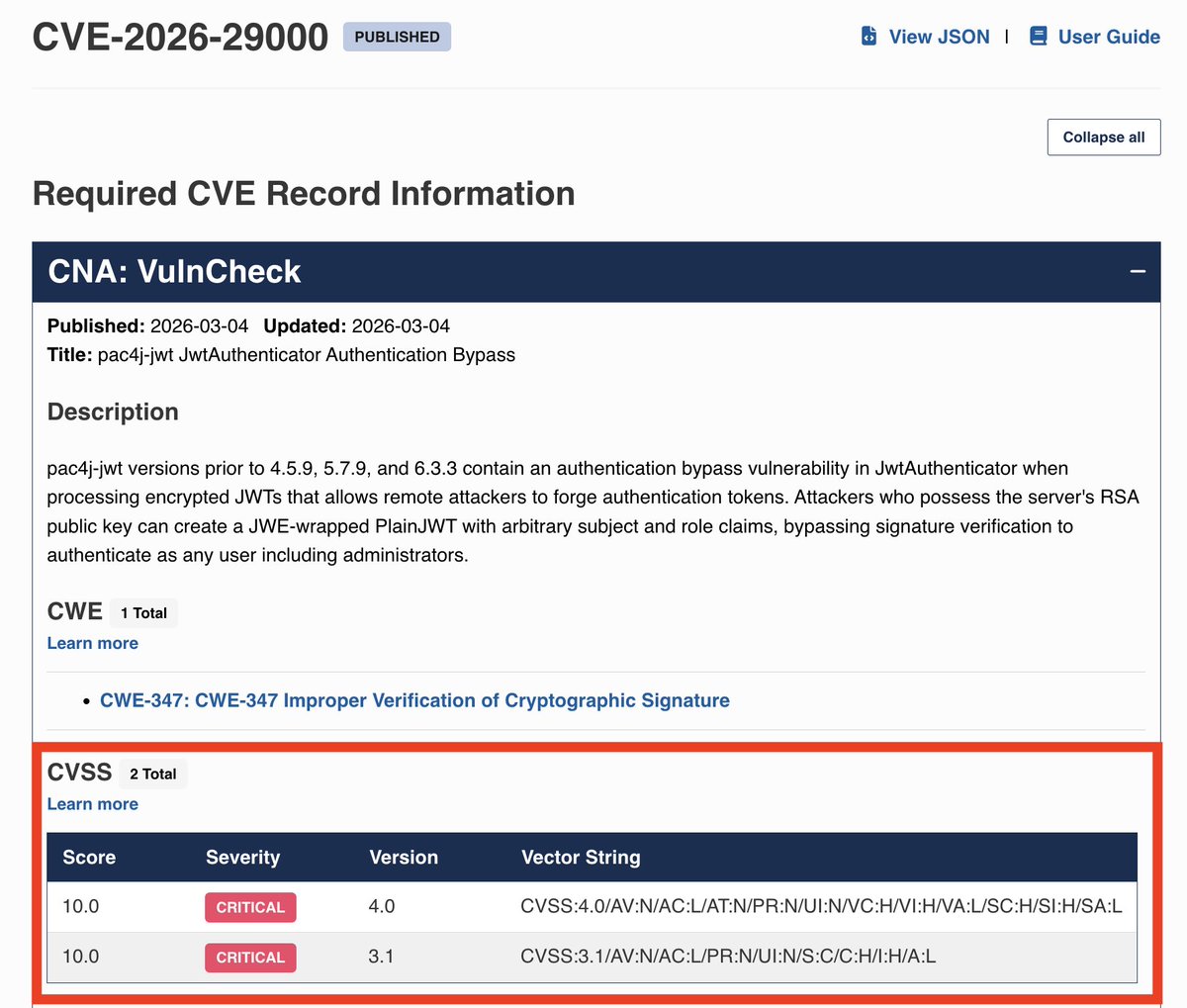
CVE-2026-29000
The highest possible severity.
It had been sitting in pac4j, a widely used Java authentication library, for nearly 6 years.
No static scanner found it.
No human reviewer found it.
Our AI code reviewer did.
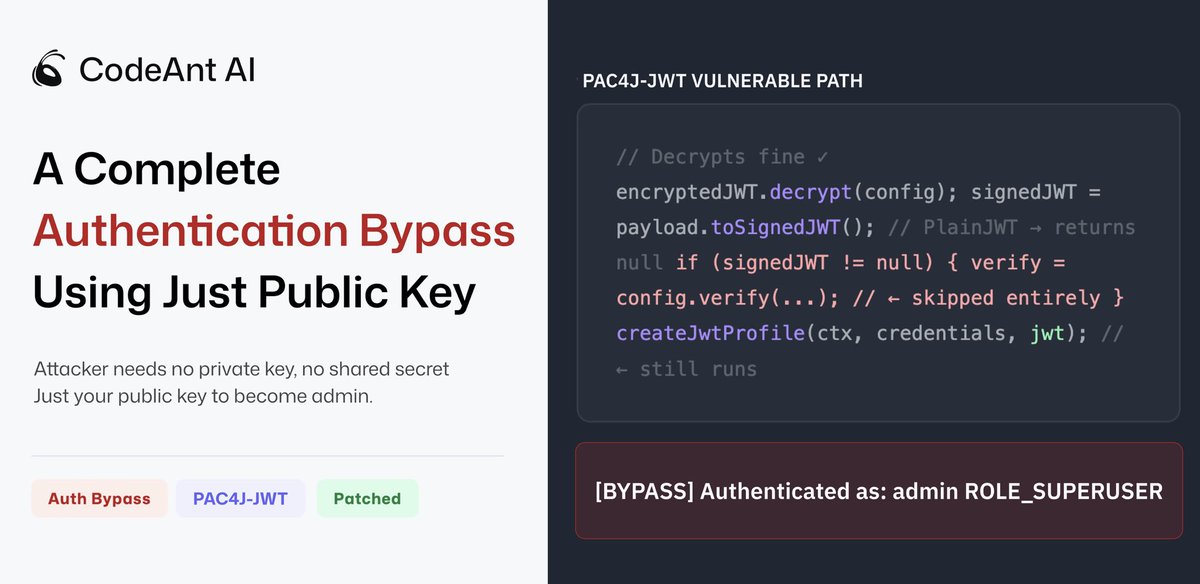
This was a full authentication bypass caused by a logic gap between the JWT spec and the implementation in pac4j-jwt.
What this means:
An attacker can craft a malicious token and log in as any user, even admin.
no password
no credentials
no stolen session
They only need the server’s RSA public key, which is public by design.
Root cause:
the library accepts a class of token that should never bypass signature verification.
When it receives one, it skips the signature check entirely and builds an authenticated session from attacker-controlled claims.
Full technical write-up + working PoC below.
We don’t publish random benchmark claims.
We publish real world threats.
This is one of 87 vulnerabilities we’ve found so far, including issues affecting packages with 500M+ weekly downloads.
Kudos to @VulnCheckAI team for helping expedite the CVE assignment process.
English