Marc Hollenbach
8.5K posts


Marc Hollenbach
@HollenbachMarc
I like creative commons



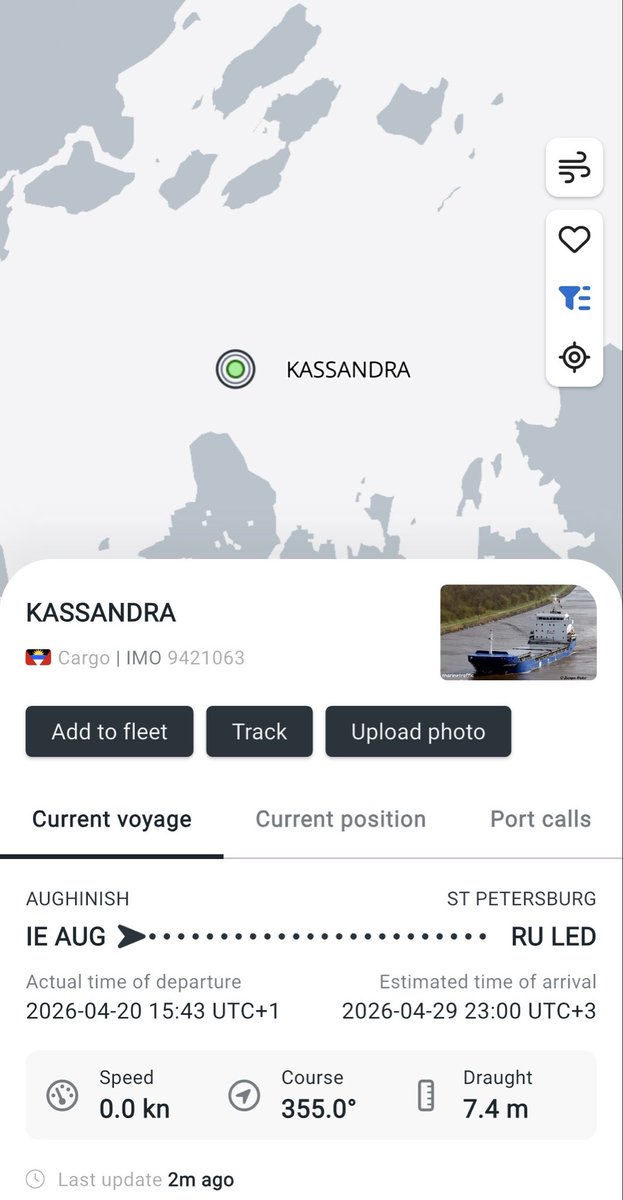
🚨Latest Trans-Alumina Express™️ cargo ship is just about to depart Aughinish pier in Ireland to deliver Alumina to St Petersburg The ship. KASSANDRA, is owned by Hansa shipping - an Estonian company. Contacts below Alumina is a vital war time resource @OckersM @Kama_Kamilia






🚨Latest Trans-Alumina Express™️ cargo ship is just about to depart Aughinish pier in Ireland to deliver Alumina to St Petersburg The ship. KASSANDRA, is owned by Hansa shipping - an Estonian company. Contacts below Alumina is a vital war time resource @OckersM @Kama_Kamilia










🇸🇰✈️❌ Fico publicly stated that 🇱🇹Lithuania and 🇱🇻Latvia have already informed Slovakia they will not allow his government plane to fly through their airspace for the planned trip to Moscow on May 9, 2026, for Russia’s Victory Day celebrations (the 81st anniversary).












Bypassing #EU #AgeVerification using their own infrastructure. I've ported the Android app logic to a Chrome extension - stripping out the pesky step of handing over biometric data which they can leak... and pass verification instantly. Step 1: Install the extension Step 2: Register an identity (just once) Step 3: Continue using the web as normal The extension detects the QR code, generates a cryptographically identical payload and tells the verifier I'm over 18, which it "fully trusts". This isn't a bug... it's a fundamental design flaw they can't solve without irrevocably tying a key to you personally; which then allows tracking/monitoring. Of course, I could skip the enrolment process entirely and hard-code the credentials into the extension... and the verifier would never know.

Hacking the #EU #AgeVerification app in under 2 minutes. During setup, the app asks you to create a PIN. After entry, the app *encrypts* it and saves it in the shared_prefs directory. 1. It shouldn't be encrypted at all - that's a really poor design. 2. It's not cryptographically tied to the vault which contains the identity data. So, an attacker can simply remove the PinEnc/PinIV values from the shared_prefs file and restart the app. After choosing a different PIN, the app presents credentials created under the old profile and let's the attacker present them as valid. Other issues: 1. Rate limiting is an incrementing number in the same config file. Just reset it to 0 and keep trying. 2. "UseBiometricAuth" is a boolean, also in the same file. Set it to false and it just skips that step. Seriously @vonderleyen - this product will be the catalyst for an enormous breach at some point. It's just a matter of time.

Congrats to our winner @JordyP1993 🎉