Normal
24 posts


Normal
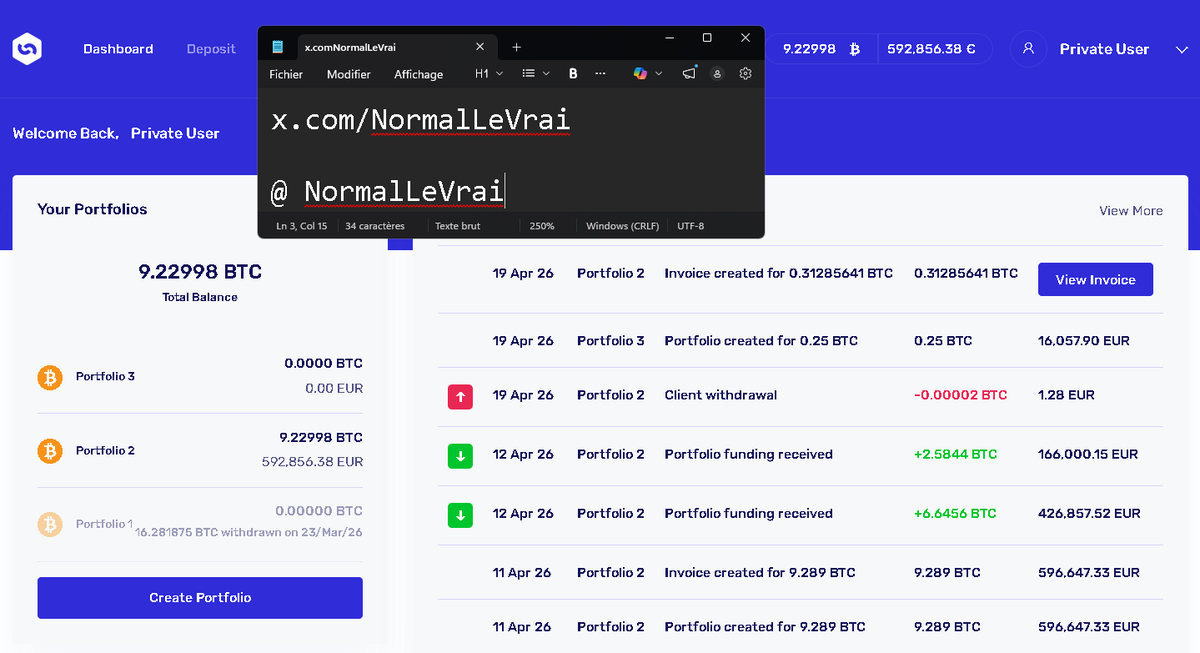
@NormalLeVrai
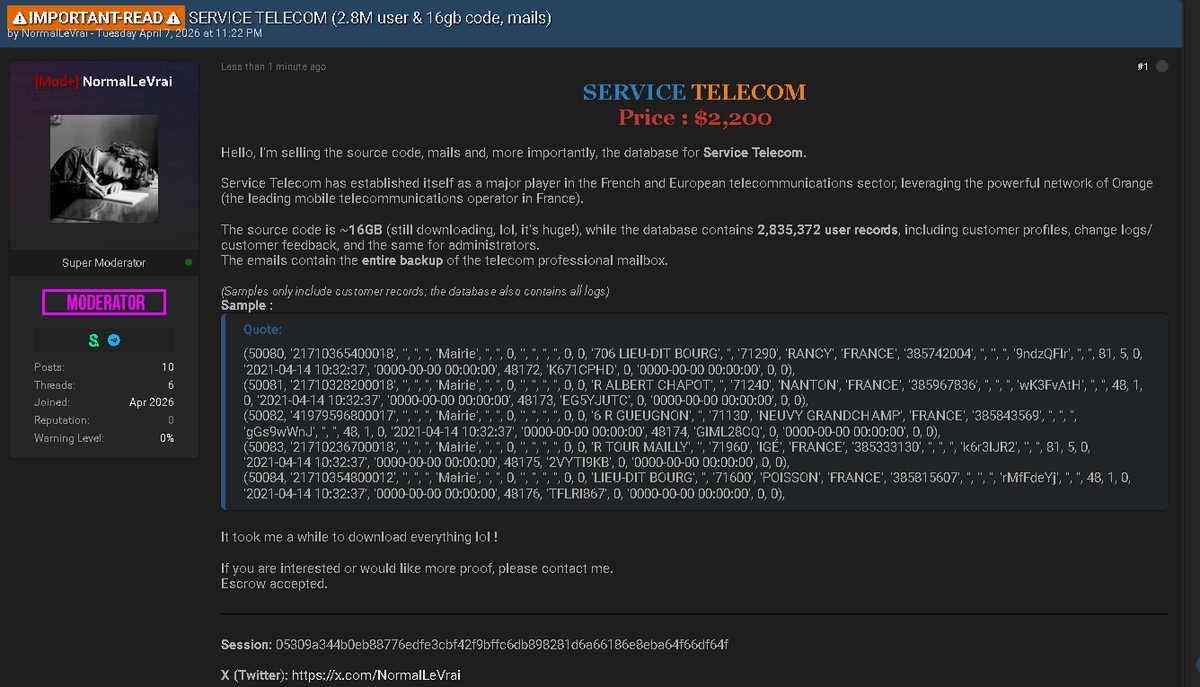
ShinyHunters Operator, Old LAPSUS$ member, Owner BreachForums & LeakForums | Elite cybersecurity collective based in France

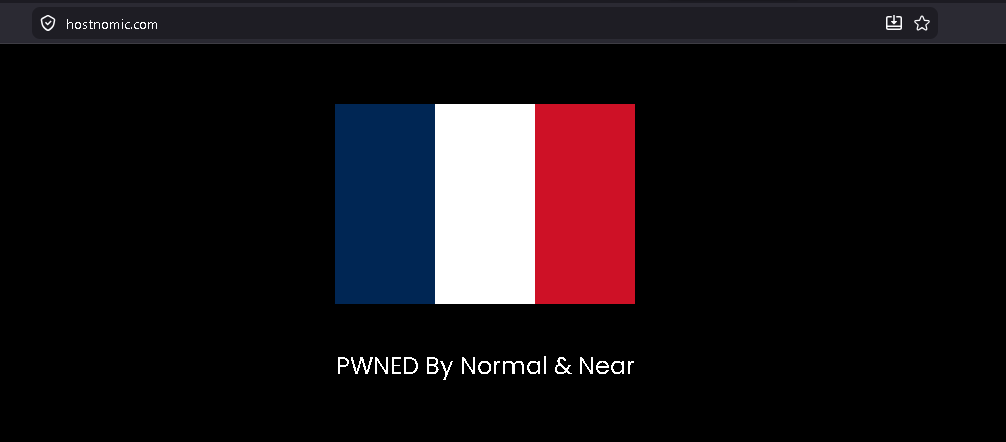
‼️🇮🇱 Galcomm (galcomm.com), one of Israel's largest ICANN accredited domain registrars and hosting providers, has allegedly suffered an unauthorized access of its internal systems, with its database and full source code published on a popular cybercrime forum. ⠀ ‣ Threat Actor: NormalLeVrai ‣ Category: Data Breach / Source Code Leak ‣ Victim: Galcomm (Communigal Communication Ltd) ‣ Industry: Domain Registration / Web Hosting ⠀ Galcomm is an Israel based registrar with over 20 years of operation, providing domain registration, hosting, and SSL services to customers in Israel and internationally. The actor has released both the database and source code for free download. The leak allegedly contains: ⠀ ▪️ 31,000 database lines ▪️ 2.32 GB of compressed source code ⠀ The sample posted shows entries from a form fields table (Ninja Forms schema), with field labels including Name, Email, Message, and Full Name, and a column flagging records as personally identifiable.








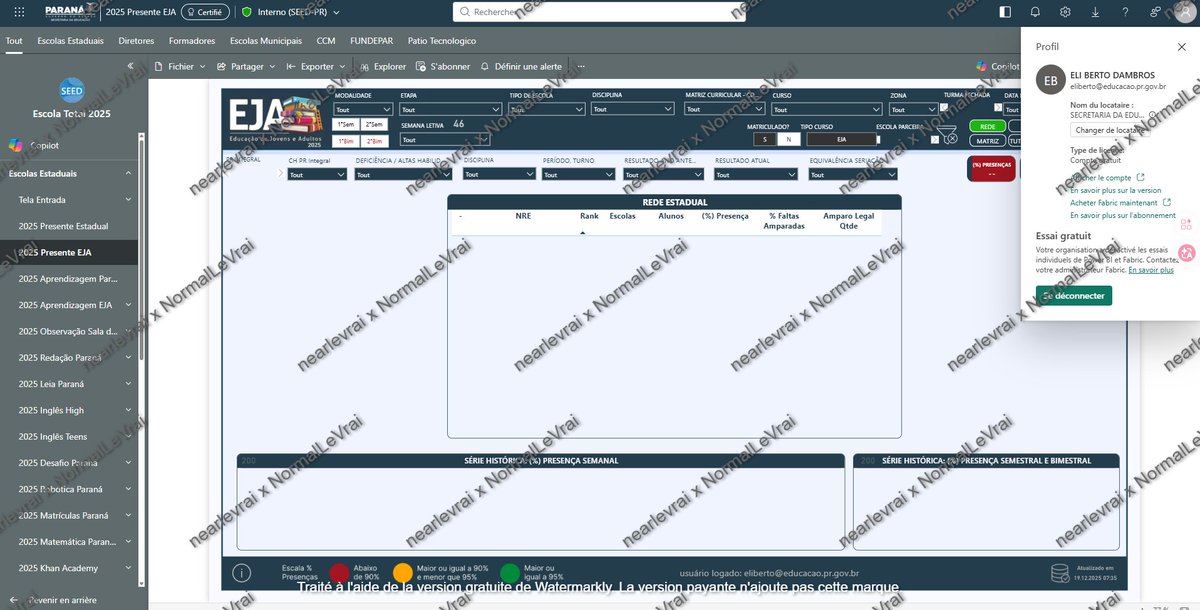
Brazilian Government with @nearlevrai 😋









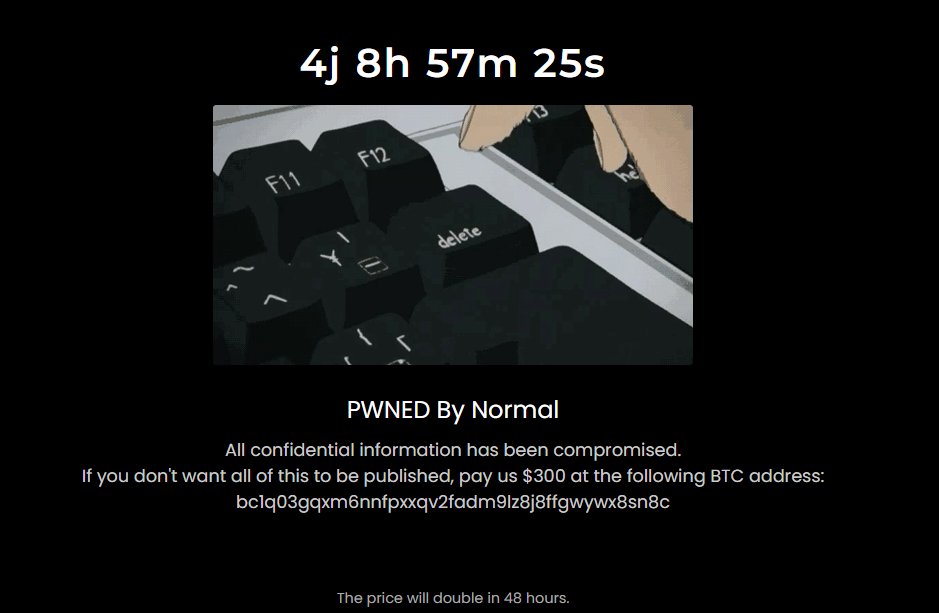
Chile 🇨🇱 - FreeSAP has allegedly suffered a data breach and extortion attack, resulting in the theft of its website source code and a database containing over 40,000 rows of user and admin information. dailydarkweb.net/chilean-it-fir…