Normal retweetledi

‼️🇩🇪 Six hosting/registrar providers, described by the actor as "German registrars," have allegedly suffered an unauthorized access of their internal systems after threat actors pivoted through the Axmir panel, with 7.2 million database lines and 18.2 GB of source code put up on a popular cybercrime forum.
⠀
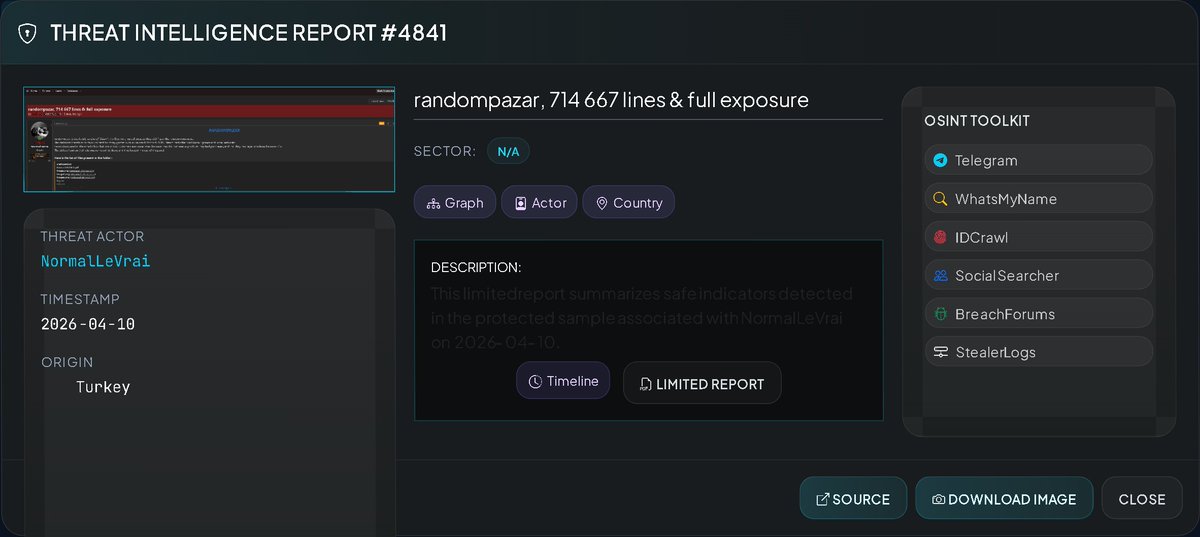
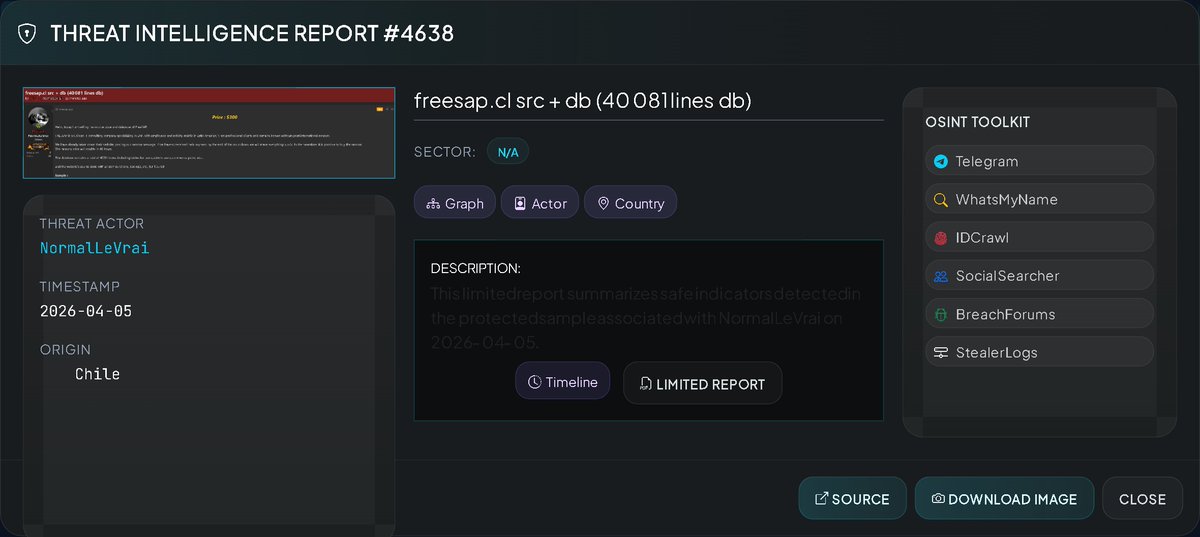
‣ Threat Actor: NormalLeVrai (in collaboration with "Near")
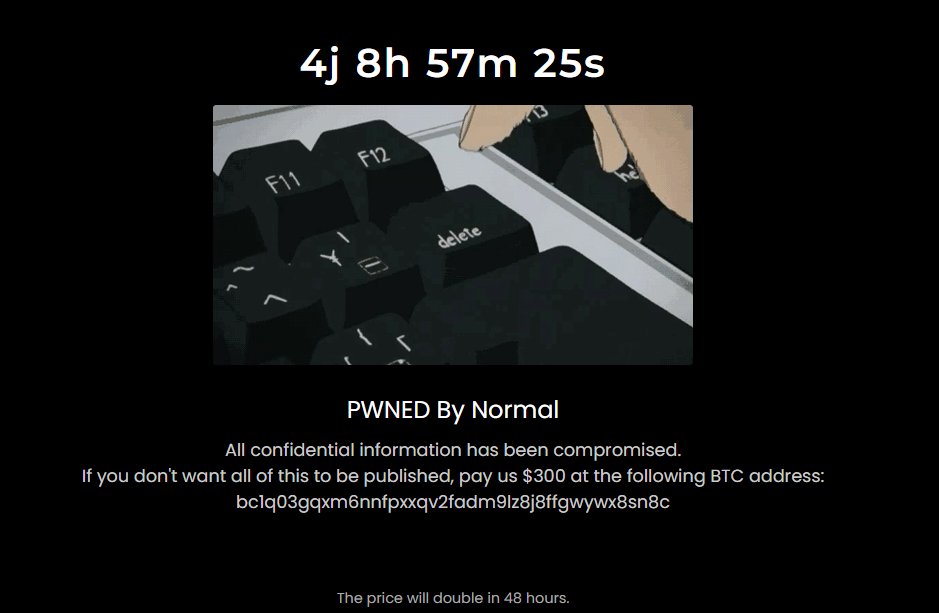
‣ Category: Data Breach / Source Code Leak / Website Defacement
‣ Victim: Axmir + 5 linked registrar/hosting domains
‣ Industry: Web Hosting / Domain Registration
⠀
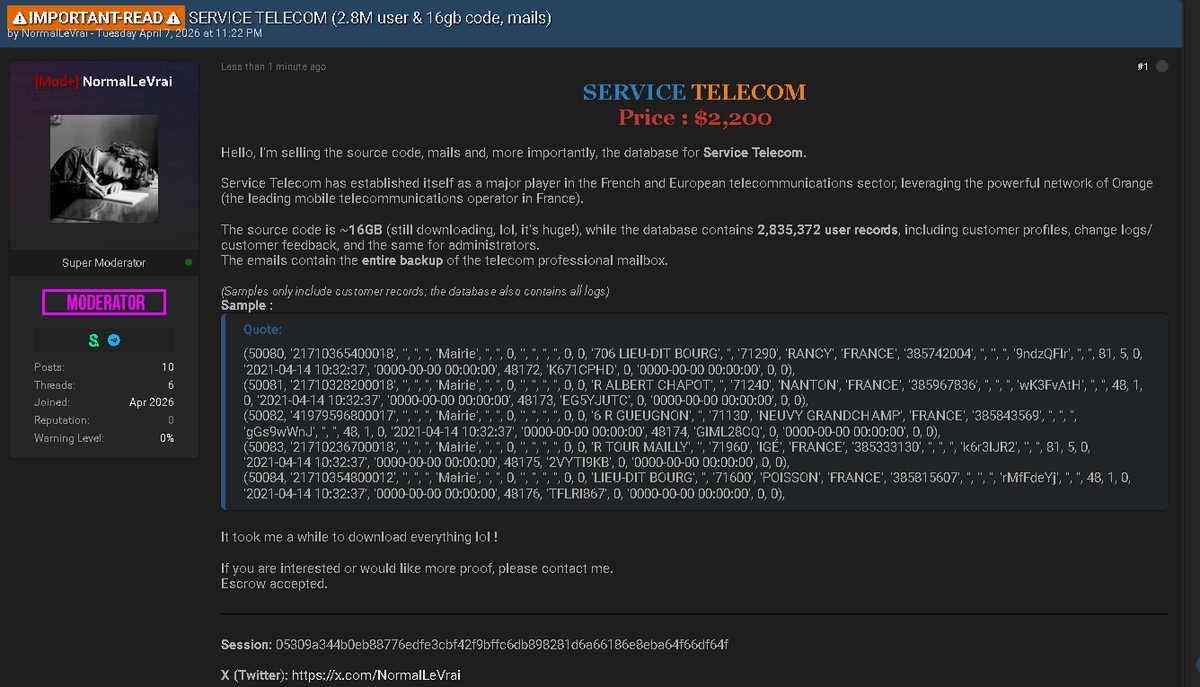
The actor claims to have gained access to the Axmir panel, which was itself linked to five other registrar/hosting domains, allowing them to pull databases and source code from all six. The affected domains are:
⠀
▪️ axmir.xyz
▪️ ajkerhoster.com
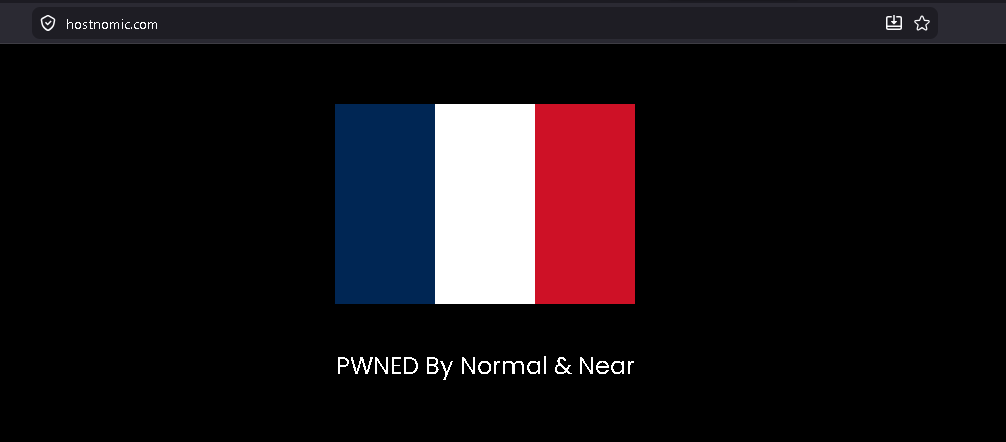
▪️ hostnomic.com
▪️ khandakarit.com
▪️ mnhost.top
▪️ rapidhostbd.com
⠀
Note: despite the "German registrar" framing, the domain names and branding on several of these providers (ajkerhoster, khandakarit, rapidhostbd) suggest Bangladeshi operators. The "German" label may refer to upstream hosting infrastructure rather than corporate origin.
⠀
The dump allegedly includes:
⠀
▪️ 7,242,212 database lines
▪️ 18.2 GB of compressed source code
▪️ 13 subdomains also breached
▪️ 2 sites defaced
⠀
Hosting/registrar compromises of this type typically expose highly sensitive customer data. Potential exposure across the affected providers includes:
⠀
▪️ Customer account credentials (usernames, password hashes)
▪️ Billing and contact information
▪️ Domain registration WHOIS records
▪️ Hosting control panel access data
▪️ Payment and transaction history
▪️ API keys and internal configuration


English