Chainkit cyber integrity automation
2K posts


Chainkit cyber integrity automation
@chainkit
Automate and attest to the integrity of any data, of any type, in motion and at rest—in real-time | Ransomware, APT Detection | Forensics | Compliance


⛓️💥 Unleash next-level #AI and #HPC performance with the @AMD Instinct™ MI325X GPU on Vultr! With 256 GB HBM3E memory and 6 TB peak bandwidth, it's perfect for large-scale inference, data analytics, and more. #CloudComputing #GPUPower #DataAnalytics blogs.vultr.com/MI325X

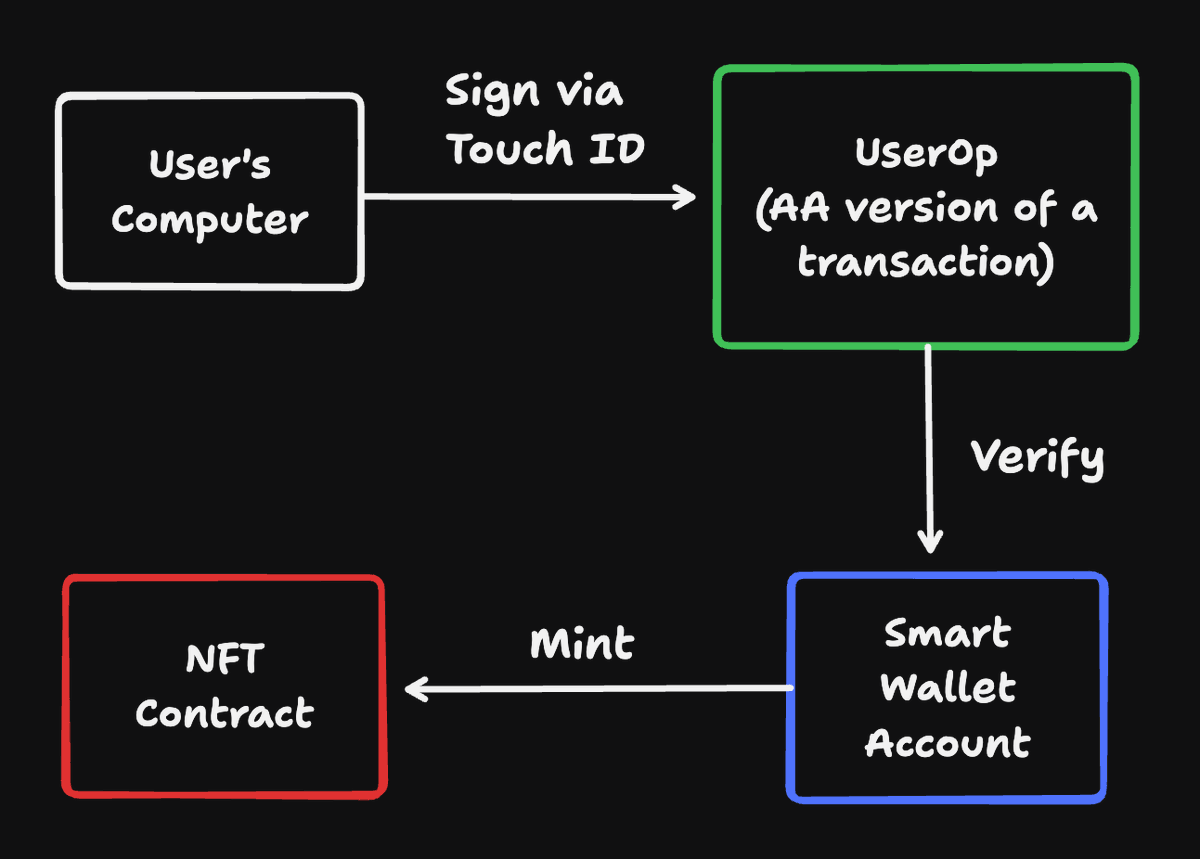




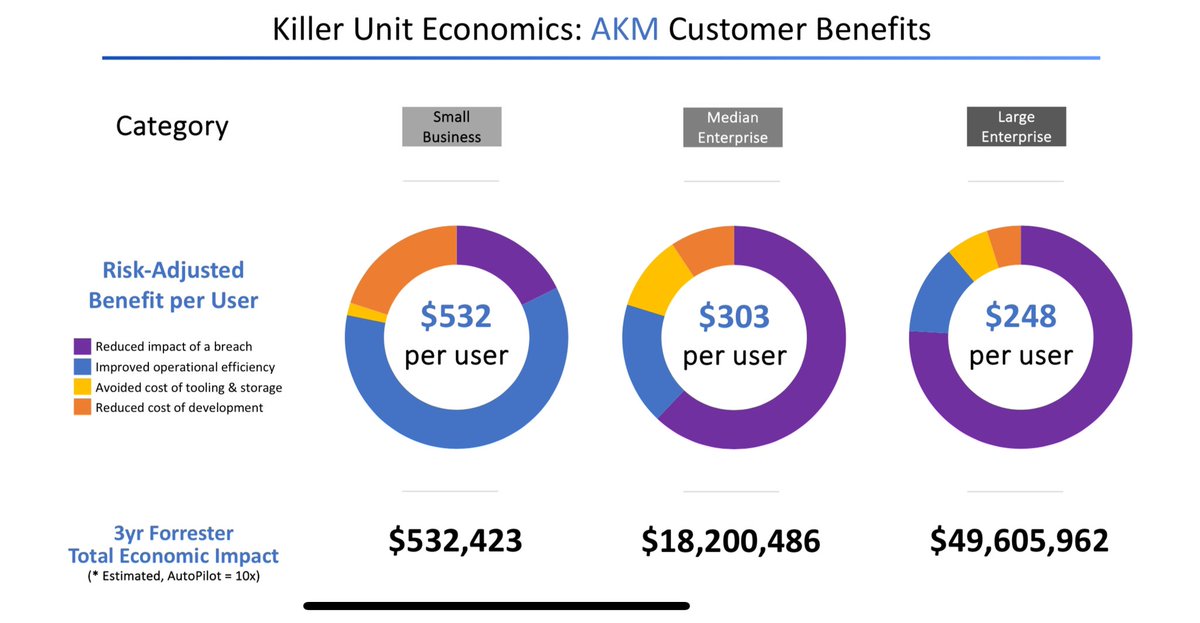
Booting up AutoPilot for CyberSecurity linkedin.com/pulse/autopilo…

Booting up AutoPilot for CyberSecurity linkedin.com/pulse/autopilo…


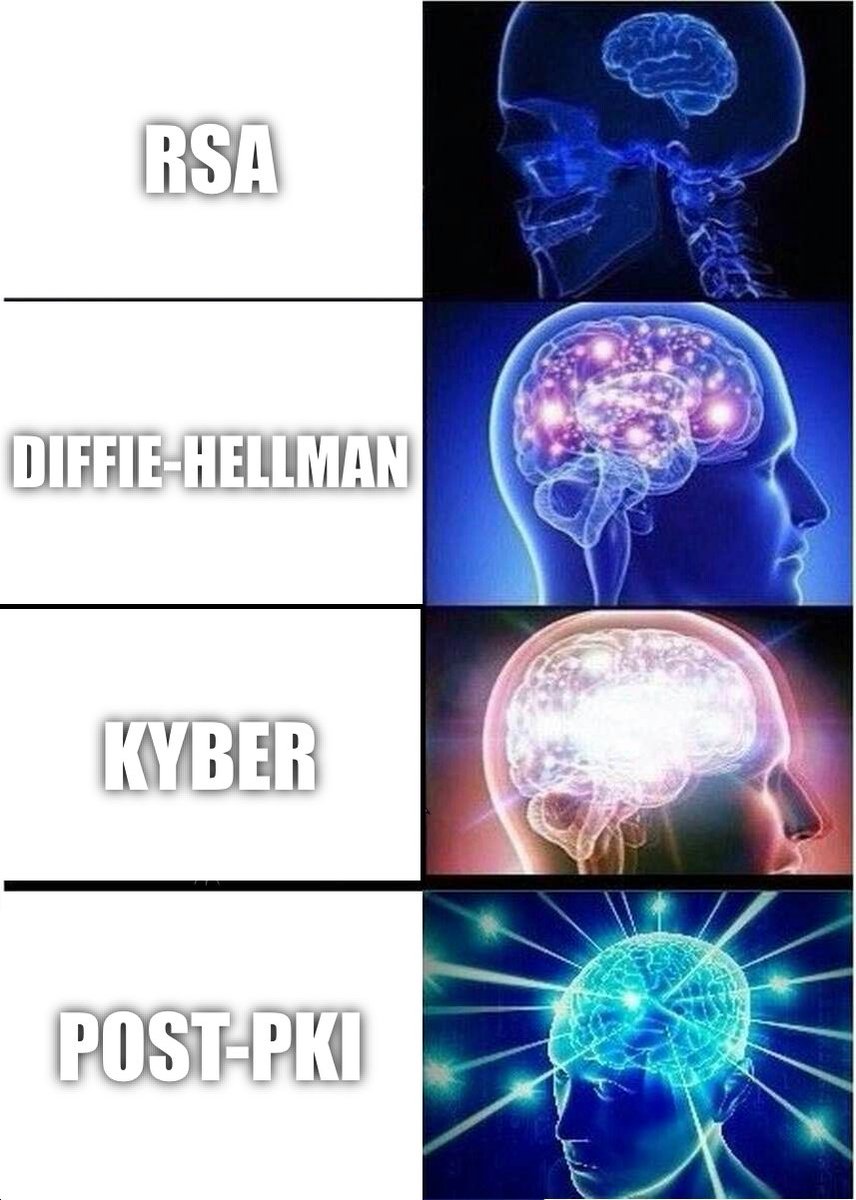
If you're an ethical hacker and can explain the Post-PKI Autonomous Key Management (AKM) in this video, reply below for an interview:

Booting up AutoPilot for CyberSecurity linkedin.com/pulse/autopilo…



Now the story really begins; We understood that we were not the first ones to arrive; Most of the machines were already compromised! They had crypto mining software installed, such as XMRig. Moreover - they leveraged pricy GPUs that were present on the machines in the clusters.