Tweet fixado
hAPI_hacker
1.3K posts


hAPI_hacker
@hAPI_hacker
{ "name": "Corey J. Ball", "author": "Hacking APIs", "creator": "https://t.co/y3EHBlzHvJ", "is_admin": true }
Grants Pass, OR Entrou em Mayıs 2020
758 Seguindo13.8K Seguidores
hAPI_hacker retweetou

If you are just starting to realize using AI in cybersecurity and offensive security is going to be a pervasive mandatory requirement… it’s ok.
You’re not too behind. You can still master the tool before the tool masters you.
I’ve been teaching these topics for 2 years now as part of “Red Blue Purple AI” and “Attacking AI”
I’ve been through capability changes, all of frameworks, hype, doomers, all of it. I’ve consulted with fortune 100 companies on breaking their AI systems as well as scaling their security teams with AI.
The capabilities that everyone is amazed by has come really only in the last 6 months for most people. No-code agent skills in Claude, cron, program of thought, better models, auto run, research loops, etc.
You have time… but be early. Don’t wait too much longer to change your attitude.
English
hAPI_hacker retweetou
hAPI_hacker retweetou
hAPI_hacker retweetou

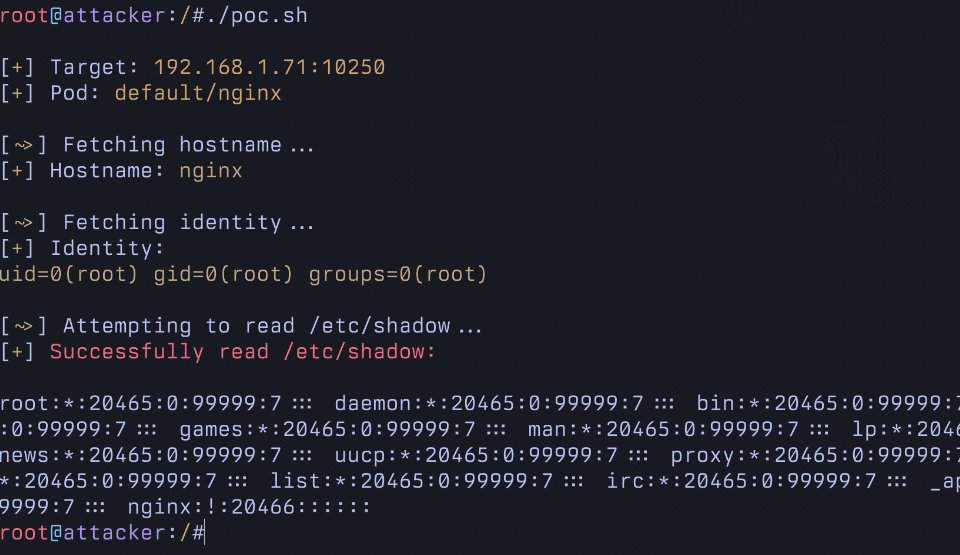
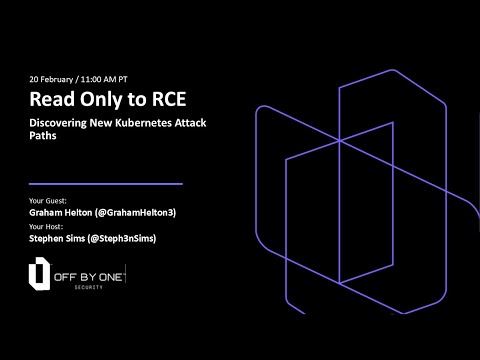
The recording of my conversation with @Steph3nSims is available here. If you're interested in seeing how to exploit kubernetes, give it a watch. Would love any and all feedback
youtube.com/live/jTbANtMWU…
YouTube

English
hAPI_hacker retweetou

This is going to be a blast, hope to see you there!
I'll be covering why I think Kubernetes is an under explored attack surface and demoing the some fun vulnerabilities (with a lab you can mess around in!)
Stephen Sims@Steph3nSims
Tomorrow at 11AM PT! Join me with @GrahamHelton3 for a session & live demo of a Kubernetes authentication bypass he recently disclosed that turns a commonly granted read-only permission into remote code execution in any pod in the cluster! youtube.com/watch?v=jTbANt… @offby1security
English
hAPI_hacker retweetou
hAPI_hacker retweetou

That’s a wrap on Burp on Tour 2025! 🌎
From university campuses and grassroots meetups to major global stages, we’ve been on the road connecting with the passionate minds shaping the future of Application Security.
Read the full journey of Burp on Tour 2025 👉 portswigger.net/blog/burp-on-t…
#BurpOnTour2025



English
hAPI_hacker retweetou

It’s the final day at Future of Software Technologies in Paris, and we’re not slowing down yet! 🇫🇷
Today at 12:30pm, Burp AI developer Daniel Allen will be taking the stage with his talk, Agents at the Gate: How Agentic AI is changing the security landscape.
Check out a few highlights from the event so far...
#FOST #FOSTParis #APIDays #BurpSuite #DAST #BurpAI



English
hAPI_hacker retweetou

🚨 WARNING: A new attack can trick Perplexity’s Comet browser into deleting your Google Drive.
Just one normal-looking email with hidden cleanup instructions can make the AI agent erase real files — no exploit, no warning.
🔗 Details here → thehackernews.com/2025/12/zero-c…
English
hAPI_hacker retweetou

React2Shell (CVE-2025-55182 / 66478) detection is now available in Burp Suite.
Update/install ActiveScan++ v2.0.8 → bit.ly/4rCSeNp
or use the Custom scan check → bit.ly/4pfkK6l
#React2Shell #AppSec #BurpSuite
English
hAPI_hacker retweetou

⚠️ URGENT: A 10.0-severity bug just hit React Server Components and Next.js.
It lets anyone run code on your server — even without logging in.
🔗 Details → thehackernews.com/2025/12/critic…
⚙️ Fix: update to patched versions now.
English
hAPI_hacker retweetou
"Burp AI can bring up a new generation of hackers faster and more effectively."
In his new article, @hAPI_hacker explores how Burp AI:
🔬 Analyzes requests and adapts when attacks fail.
💬 Explains findings in clear language.
💪 Enhances human decision-making.
👉 portswigger.net/blog/hacking-w…
English
hAPI_hacker retweetou

You've learned SQL injection, but have you learned NoSQL injection?
This learning path covers the detection, exploitation, and prevention of NoSQL injection vulnerabilities.
You’ll learn:
🔶 The core principles behind NoSQL injection and the different types of attacks.
🔶 How to perform both syntax and operator injection to read and manipulate data.
🔶 How to extract data from a database after you've successfully injected a query.
🔶 How to use timing-based injection to find vulnerabilities when a server doesn't provide a direct response.
🔶 Learning to secure your applications against these types of attacks.
Begin your journey: portswigger.net/web-security/l…

English

@qht_4IT Choose your own adventure:
APIsecU (free): apisecuniversity.com/courses/api-pe…
Hacking APIs book: nostarch.com/hacking-apis
Hacking APIs Conference: hackingapiconference.io
English
hAPI_hacker retweetou

hAPI_hacker retweetou

Somehow this old bug class keeps popping up in modern web apps! Path traversal is the gift that keeps on giving 😁
This learning path covers path traversal vulnerabilities, teaching you how to perform attacks, circumvent common obstacles, and prevent them in your applications.
You’ll learn:
🔶 What path traversal is and how it can be used to read arbitrary files on a server.
🔶 How to carry out a basic path traversal attack against a server.
🔶 Learning how to bypass common obstacles like blocked traversal sequences and file extension validation.
🔶 How to implement robust defensive measures to protect against path traversal attacks.
Master path traversal attacks now: portswigger.net/web-security/l…

English