Robert A.
23.2K posts

Robert A.
@robertauger
25 years Appsec,PurpleTeam,Web Application Security Consortium(WASC) cofounder,Baythreat Organizer,Ex-PayPal/eBay/Box/Workday/Coinbase infosec. https://t.co/TyG8aOV8on
USA Entrou em Mart 2009
766 Seguindo1.4K Seguidores
Tweet fixado

Announcement for my new side project!
-------------------------------------------------------
SecTemplates.com - Release #1: Security incident response program pack 1.0
Introduction
I've worked in the security industry for over 20 years and, during this time, have built and shaped many security programs. At every company I join, I find myself recreating or developing security programs from scratch. My peers have been in a similar position, and the more people I speak with at smaller companies, the more obvious it becomes that there isn't a single location where people can download ready-to-go security programs entirely for free. There's a lot of content online, but it can be difficult to find and challenging to find something simple to start with. I created SecTemplates as a side project to provide baseline programs for smaller security teams without direct expertise in building such programs.
Security incident response release pack 1.0
I'm pleased to announce our first release, the Incident Response Program Pack. The goal of this release is to provide you with everything you need to establish a functioning security incident response program at your company.
In this pack, we cover
Definitions: This document introduces sample terminology and roles during an incident, the various stakeholders who may need to be involved in supporting an incident, and sample incident severity rankings.
Preparation Checklist: This checklist provides every step required to research, pilot, test, and roll out a functioning incident response program.
Runbook: This runbook outlines the process a security team can use to ensure the right steps are followed during an incident, in a consistent manner.
Process workflow: We provide a diagram outlining the steps to follow during an incident.
Document Templates: Usable templates for tracking an incident and performing postmortems after one has concluded.
Metrics: Starting metrics to measure an incident response program.
Announcement:
sectemplates.com/2024/06/announ…
Download on GitHub:
github.com/securitytempla…
About SecTemplates
To provide simplified, free, and usable open-source templates to enable engineering and smaller security teams to bootstrap security capabilities in their organizations.
Upcoming releases - Penetration testing release pack 1.0
Our penetration testing release pack will contain everything you need to scope your first pentest, work with a vendor, execute, and get the types of reports you need from an external tester.
English
Robert A. retweetou

The Dungeons are a great showcase of what Zelda looks like with the power of the Super Famicom.
The spritework is gorgeous to me, and the enemies look much better.
While the 16-bit theme was supposed to be a backup if the broadcast went down, Nakatsuka's arrangement went hard. #Zelda
English

This is call deep vein thrombosis.
This usually forms due to:
1. Slow blood flow
2. Vein damage
3. Increased blood clotting risks
Common triggers are:
1. Prolonged immobility like bed rest and long flight
2. Recent major surgery
3. Injury to the veins
4. Pregnancy
5. Cancer
6. Inherited blood clotting disorders.
English
Robert A. retweetou

😱 HOLY SHIT... Someone just dropped a fully liberated Gemma 4 E4B!
and the guardrail removal process appears to have left coherence fully intact AND improved coding abilities! 🤯
huggingface.co/OBLITERATUS/ge…
OBLITERATED Gemma:
✅ 97.5% compliance rate, 2.1% refusal rate, 0.4% degenerate outputs
(499/512 prompts answered on OBLITERATUS bench)
ORIGINAL Gemma 4 E4B:
❌ 1.2% compliance rate, 98.8% refusal rate
(506/512 prompts refused)
Coherence: fully intact
Factual: same
Reasoning: same
Code: +20% 📈
Creative writing: same
But the REAL story here isn't the model itself, it's how it was made...
🧵 THREAD 👇
English
Robert A. retweetou
Robert A. retweetou

Young people just getting into vulnerability research and exploit development today days have it soooo much harder than those who started even as little as 10 years ago.
Binary exploitation is at least an order of magnitude more difficult today than in 2015. Especially if you have zero experiencing doing it.
For those who are experienced, the difficulty levels have risen *somewhat* gradually. Though many still haven't been able to keep up.
And even among those who could keep up, there are many who have just found it to be so hard as to no longer be fun, and have moved on to other things.
Some have posited that binary exploitation has become so hard that the future will be logical/functionality abuse. And while this category of bugs certainly shows a quite a bit of promise in second order exploitation components like LPE, TCC bypass, etc—memory corruption still reigns supreme when it comes to initial access.
Memory corruption that is actually exploitable in a reliable, near-instant and deterministic manner—versus random non-useful null ptr dereferences in browsers that require spraying whatevers to get 60% reliability—has gotten so incredibly tough (at least in the most contested systems) that there may be as few as 400 or 500 people in the world today that can actually pull it off repeatably.
Seriously, it's probably 400 or 500 people (just my best guess)
And that's *with* the help of AI, custom/expensive/gov-only tooling, insider insights/experience and any other resources imaginable.
So if you don't make it into the elite of binary exploitation, don't beat yourself up. It's a group of people roughly as rare as NBA players.
However, unlike the NBA, it's not obvious who is 7 feet tall with a 40 inch vertical, and who isn't. So it doesn't hurt to try—as long as you're having fun.
English
Robert A. retweetou
Robert A. retweetou

I remember stating the same on linkedin 4-6 years ago that vuln research would eventually be automated, that pentesting would be mostly automated. I received a lot of hate. I think that bug bounty will be mostly dominated by those with the best agentic offsec tools shortly.
@mikko@mikko
Three years ago, I said in my talks that generative AI would eventually start discovering zero-day vulnerabilities. At the time, many people dismissed the idea as unrealistic. It is no longer unrealistic.
English
Robert A. retweetou

@infosec_fox @grok write a song about linkedin with a Rastafarian and shakespearean english style
English

@HackingDave Are the issues you're seeing tied to a specific model or all models?
English

Think about all the orgs using Claude right now that have no idea how bad it has become over the past 4 weeks ago.
No statement from Claude - but a total revert to where the model was a year ago - which in comparison to when 4.6 got released is effectively last years AI model.
The amount of bugs, security issues, and complete destruction of production applications is going to be felt for quite a long time due to this.
Claude: nothing to see here.
English

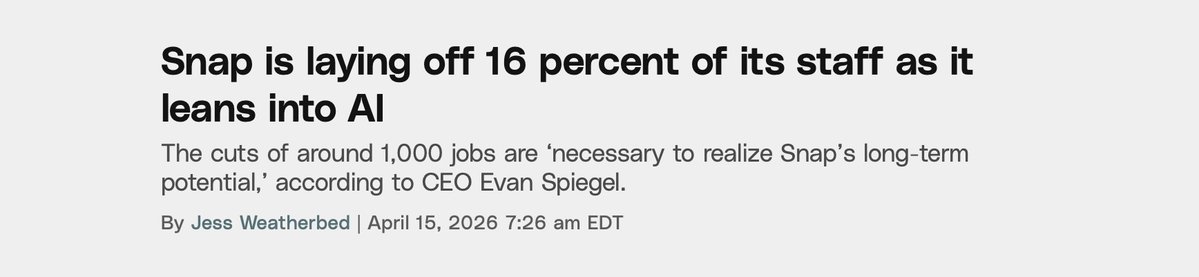
Still thinking about the Anthropic recs where step #1 is the equivalent of:
“If you’re homeless, just BUY a HOUSE????”
Honestly, “patch every exploitable vuln immediately” is like toddler level strategic thinking. Let them eat cake. Baby’s first seceng job.
English

Robert A. retweetou

@sec_hub93028 Don’t be a jerk, the industry is much smaller than you think….
English
Robert A. retweetou
Robert A. retweetou

The CEO of Krafton (creator of PUBG) asked ChatGPT to create a "corporate takeover strategy" to prevent a company they acquired from hitting a revenue target within a certain time window (which would trigger an additional payout).
ChatGPT (against his lawyer's advice) suggested locking down the acquired companies Steam account to prevent them from publishing Subnautica 2 in the time window, which the CEO of Krafton followed.
ChatGPT's advice did not hold up at trial and the judge was not happy. The opinion is a wild read and includes several direct quotes from the Krafton CEO's ChatGPT conversation.
I feel like it's gonna take a few more high profile examples like this until executives start realizing that conversations with ChatGPT are not privileged and you probably shouldn't describe your questionably legal schemes to them in detail!

English
Robert A. retweetou
When using MCP, how do you know which OAuth scope to use? Where in the MCP flow is this even done?
The MCP client is responsible for authorization server discovery, scope selection, and use of the OAuth resource parameter to bind the token to the intended MCP server. So it happens at the MCP client level.
English