Tweet fixado

I’m super pumped to release v1.0 of my free Azure security tool (PurpleCloud) in the hopes that it will be useful to the InfoSec community evolving the so called “Purple Teaming” in the cloud!
Website: purplecloud.network
English
Jason Ostrom
227 posts


@securitypuck
Instructor and Author @SANSInstitute | Blue & Red Team | GoLang & Terraform| Builder of things | Husband & Father | #NHL #NFL | @[email protected]







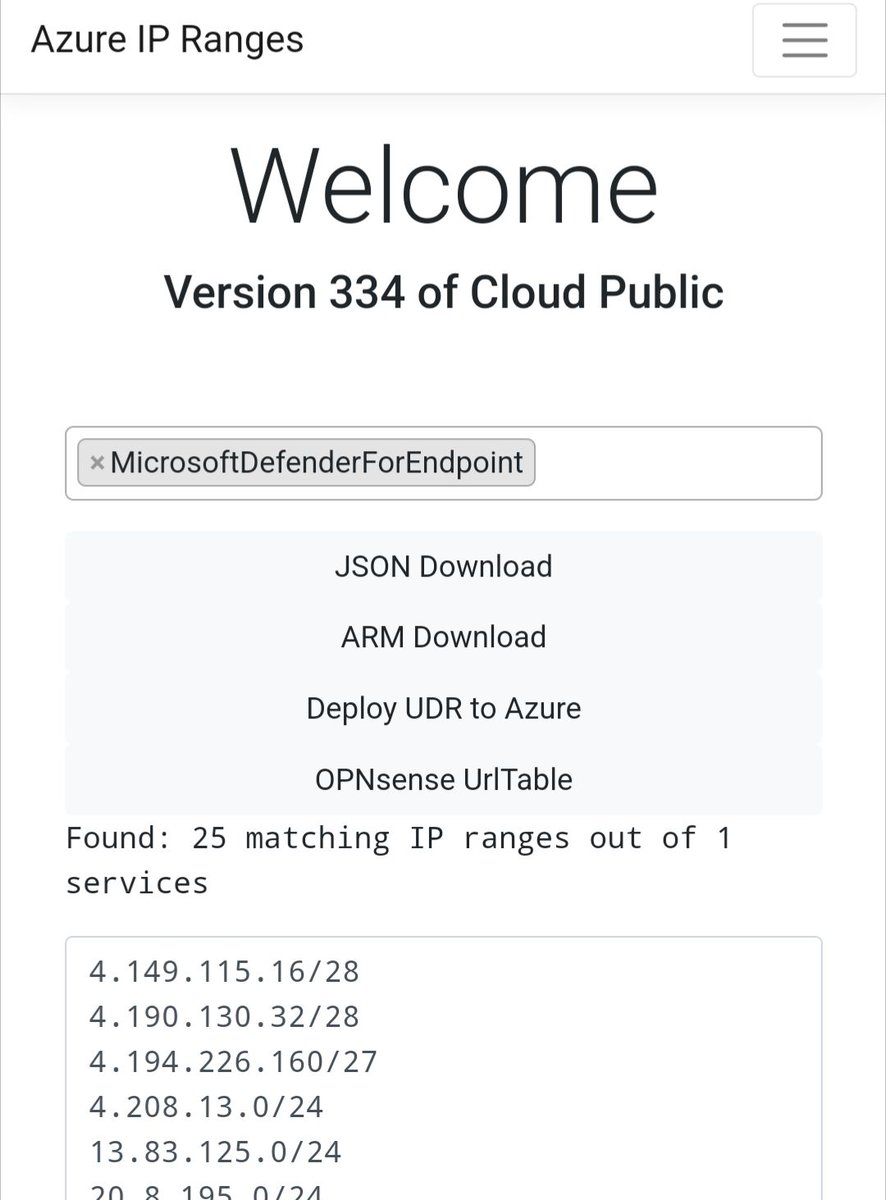


Do you know the Azure IP Ranges site by @derdanu ? It's a great tool to filter IP ranges by service and even download them in different formats. azureipranges.azurewebsites.net








If you do have a M365 dev tenant and want to get started with building out labs for red teams. Highly recommend this SANS free on demand course. SANS Workshop – Building an Azure Pentest Lab for Red Teams sans.org/webcasts/sans-…



