Tweet fixado
Tom Pohl
6.1K posts


Tom Pohl
@tompohl
My mission is to humbly serve the curious with excitement! https://t.co/OksE77tIah [email protected]
Des Moines, Iowa Entrou em Nisan 2008
906 Seguindo1.3K Seguidores
Tom Pohl retweetou

#SecKC is just 2 WEEKS AWAY! We've got the legendary @tompohl and @benjaminkelley giving talks with @mcohmi emceeing!
Don’t miss the action, make sure to let us know you're going to be there!
Full Details: seckc.org/upcoming-event…
Register today: forms.gle/UoMr1Q8dSzGFNS…
English
Tom Pohl retweetou

New from Penetration Testing Manager @TomPohl: How default #Cisco settings gave up full router configs—no credentials needed. Learn how small oversights can lead to big breaches. Read the blog: ow.ly/3Fqh50VPqJV
#Cybersecurity #PenetrationTesting #Pentest #IT #CISO #DFIR
English

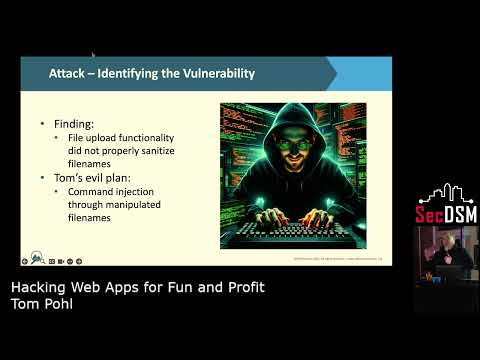
Hacking Webapps for Fun and Profit!
youtu.be/vN4lOAuibcc?si…
I had a really great time putting this presentation together and hopefully it'll inspire you to look at your applications more critically and fix them before someone malicions finds them!
#PenTesting #WebApplication
YouTube
English
Tom Pohl retweetou

Web apps are a top target for #hackers! From command injection to exposed APIs, small flaws can lead to major breaches. @Tompohl shares the common attacks & how to spot and stop them ow.ly/UJ7o50V3AOo
#Cybersecurity #WebApp #CISO #Security #PenTesting #IT #DFIR #Pentest
English
Tom Pohl retweetou

Join LMG Security #Pentest expert @TomPohl for "Hacking Web Apps for Fun & Profit!" Watch tomorrow (2/6) at 6:30pm CT for web app hacks & prevention strategies.
Live: Foundry Distilling Co., West Des Moines
Live-stream: @SecDSM" target="_blank" rel="nofollow noopener">youtube.com/@SecDSM
#SecDSM #DesMoines #WebApp #IT
English
Tom Pohl retweetou

Cybercriminals are targeting APIs & costing businesses $75B annually! Our #PenetrationTesting Team Manager @tompohl shares why #WebApp API penetration testing is crucial & 5 things every #API #pentest should include: lmgsecurity.com/the-critical-r…
#Cybersecurity #APISecurity #CISO #IT
English

* Unauthenticated RCE vs all GNU/Linux systems (plus others) disclosed 3 weeks ago.
* Full disclosure happening in less than 2 weeks (as agreed with devs).
* Still no CVE assigned (there should be at least 3, possibly 4, ideally 6).
* Still no working fix.
* Canonical, RedHat and others have confirmed the severity, a 9.9, check screenshot.
* Devs are still arguing about whether or not some of the issues have a security impact.
I've spent the last 3 weeks of my sabbatical working full time on this research, reporting, coordination and so on with the sole purpose of helping and pretty much only got patronized because the devs just can't accept that their code is crap - responsible disclosure: no more.

English

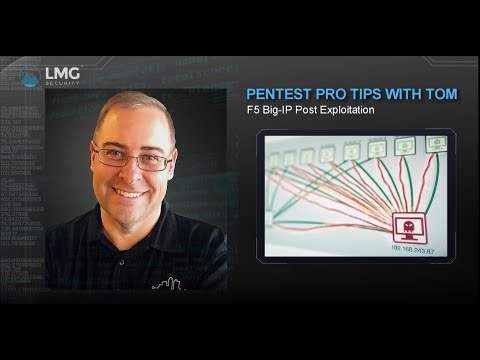
Are you curious about post exploitation of @F5 Big-IP’s? Check out my latest video on some techniques after you’ve compromised a box!
youtu.be/WKEX53S3DSI?si…
YouTube
English

@gabsmashh @tompohl Is it in the bottom of the bottle? Gotta drink it all to solve
English
Tom Pohl retweetou

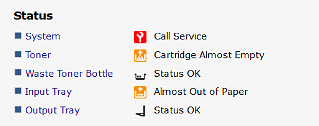
@tompohl I just received the info after about 1 hour of waiting, but I am pretty sure it was someone legitimately using the printer.
English

@tompohl I saw your presentation "How I met your printer" and I am unable to reproduce the SMTP notify process on a RICOH MP C3004ex printer. I changed all the necessary settings accordingly and setup notifications (the printer has a few issues). Did they fixed this?
English

@stratosberry What’s a redacted version of the smtp server page look like?
English

@levarburton I just watched this on my flight this
morning. Brought back so many wonderful memories. I grew up with you on both Reading Rainbow and Star Trek. I have a video of my son singing the theme song near the time when the show was ending that I absolutely treasure. Thank you!
English

Tom Pohl retweetou

There's a rule: don't trust even your friends with cameras when you're inebriated.
That said, I think @tompohl does a simply amazing job delivering an intro for me from my home studio. I may have to splice this into all of my talks.
English

@myst404_ Nice work! I literally just went through this very same exercise and then found your article! BTW I first just made a copy of Issa into /tmp/newlssa and modified like 86 to output the value of the $plain variable, but I wanted to make a tool that could do it offline too
English