Keystone Wallet Official Support
24.9K posts


Keystone Wallet Official Support
@KeystoneWalletX
Official Support for Keystone | The most user-friendly, open-source, air-gapped hardware wallet for your entire crypto journey🛡️


What's the one wallet security rule everyone should know? Tell us in comments👇

The Risk You Installed Without a Second Thought You install browser extensions to make things easier. A VPN to feel safer online. An ad blocker to clean up the page. A trading tool to save a few clicks. After that, you stop thinking about them. They sit quietly in your browser and do their job, or so it seems. When you open ChatGPT, check a transaction, or connect to a Web3 app, the browser still feels like a neutral space. Often, it is not. Recent security research shows that some browser extensions quietly take more than they should. They collect sensitive information and send it elsewhere, without making it clear to the user. For people using Web3 tools, this can be especially risky. When Helpful Tools Start Watching Silently: Browser extensions live very close to what you do online. Once installed, many of them can read web pages, see what you type, watch network requests, and sometimes access cookies across many sites. When this power is misused, the result is rarely obvious. There is no pop-up warning. No sudden crash. Everything looks normal. That is the problem. The data is collected quietly, blended into normal browsing, and easy to miss. Urban VPN and the Hidden Risk of AI Chats: This issue became clear after research by Koi Security (@KoiSecurity), later confirmed by SlowMist (@SlowMist_Team). They found that the browser extension Urban VPN Proxy was collecting data in ways that had nothing to do with running a VPN. When users visited AI platforms like ChatGPT, the extension injected code into the page and watched the network traffic. It collected what users typed and what the AI replied, then sent that data to remote servers. A VPN does not need to do any of this. What makes the situation worse is the scale. Urban VPN Proxy, along with seven related extensions such as 1ClickVPN Proxy and Urban Ad Blocker, affects more than eight million users. Urban VPN alone has over six million users, strong ratings, and even a Google Featured badge. From the outside, it looks safe. That trust is what allows the data collection to continue. Why This Is a Bigger Problem for Web3 Users: At first, collecting AI chats might sound uncomfortable but harmless. That view ignores how people actually use AI today. Many Web3 users and developers rely on AI to write scripts, debug transactions, and review wallet or smart contract code. During testing, some people hardcode mnemonics, private keys, or test wallet details directly into code and paste the full script into an AI chat. When a browser extension has too much access, that information does not only go to the AI. It can be captured directly in the browser, saved, and sent elsewhere. Over time, this becomes valuable data that can be stored, matched with other information, and reused later. The danger is not always immediate. Often, the damage shows up much later as targeted scams, wallet takeovers, or carefully planned fund losses. Axiom Enhancer and Trading Without Permission: If the Urban VPN case is about quiet data collection, the next example shows something more direct. Research from SquareX Labs (@sqrx_labs) found serious issues with Axiom Enhancer, a browser extension aimed at users of the Axiom trading platform. The extension regularly checked whether an Axiom.Trade tab was open. When it was, the extension copied the user’s login cookies and sent them to a remote server. This means attackers did not need a password. They did not need to break two-factor authentication. By reusing an active login session, they could access the trading account as if they were the user. Once inside, attackers could drain funds through low-liquidity trades. To anyone watching, it looked like normal trading. In reality, money was being moved out. This has already happened before. In 2024, the AggrTrade malicious extension used the same approach to steal one million dollars from Binance users. The same group was later linked to other extensions targeting popular Web3 trading tools. Why These Risks Are Easy to Ignore: Browser extensions are dangerous because they are quiet. Permissions are often approved with a single click. Extensions run all the time in the background. Updates happen automatically, without warning, and can change behavior weeks after installation. Some extensions even wait days or weeks before doing anything suspicious, just to avoid detection. By the time users notice something is wrong, it is often too late. Reducing Risk Without Fear: You do not need to stop using browser extensions. You just need to be clearer about your boundaries. 1️⃣ Carefully Review Requested Permissions: When an extension asks to read all websites, access cookies, or monitor network traffic, pause for a moment. Ask yourself whether that access truly matches what the extension claims to do. If the permission feels bigger than the feature, that alone is a warning sign. 2️⃣ Avoid “Three-No” Extensions: Tools with no clear developer, no public reputation, and no way to contact the creator are hard to trust. At the same time, popularity is not protection. Even extensions with millions of users and platform badges have been caught behaving badly. 3️⃣ Isolate Your Testing Environment: Use a separate browser profile or a test environment. Avoid installing unknown tools in the same browser you use to manage wallets, sign transactions, or trade. 4️⃣ Never Expose Sensitive Information in the Browser: Mnemonics, private keys, signing data, and full code that contains credentials should never appear on a browser page. Once that information is visible there, extensions with enough access may be able to read it. 5️⃣ Use Hardware Wallets: For development and testing, hardware wallets make a real difference. Keeping keys on a separate signing device and avoiding hardcoded secrets removes the temptation to trade long-term safety for short-term convenience.


🚨Beware of Solana #Phishing Attacks: Wallet Owner Permissions Can Be Altered 1️⃣Recently, we assisted a victim of a phishing attack that resulted in the unauthorized transfer of his account’s Owner permission. This is similar to the "malicious multisig" –style attack commonly seen on #TRON. The victim lost over $3M in assets. Another $2M locked in DeFi protocols was inaccessible — though fortunately, this portion has now been successfully recovered with help from the relevant #DeFi teams.👏 2️⃣How the #Solana Owner Modification Works🔐 The attacker exploited two counter-intuitive behaviors: 🔹No visible balance change during signing: Wallets typically simulate transactions and show balance effects. The attacker crafted a transaction with no visible changes, lowering suspicion. 🔹Users don’t intuitively expect ownership to be changeable: Unlike Ethereum EOAs, Solana accounts allow their Owner field to be reassigned, which many users don’t realize. 3️⃣Understanding Solana Account Ownership🧩 Solana accounts fall into two major types: 🔹Normal Accounts 🔹PDA (Program-Derived Accounts) Token accounts also use their own ownership rules enforced by the token program, which are frequently targeted in phishing campaigns. 4️⃣MistTrack Tracing🕵️ Our @MistTrack_io analysis of the attacker’s address revealed highly complex fund movements. Assets were routed primarily through two hubs: 🔹BaBcXD… 🔹7pSj1R… The laundering pattern included: • rapid multi-address hops • multi-platform mixing • cross-chain cycling • CEX deposits • reuse of DeFi assets 5️⃣How to Protect Yourself from Similar Attacks🛡️ This incident ultimately stems from phishing. Attackers use fake: ✨ airdrops ✨ quests ✨ whitelist invites ✨ announcements ✨ reward claims These links trigger signature requests containing high-risk operations like Owner reassignment. Before clicking or signing, always ask: 🔹 Is the source legitimate? 🔹 Is this really from the official team? 🔹 What exactly is this signature doing? 🔹 Are there unfamiliar permissions or unknown addresses? If you don’t understand the permission request — STOP! Never sign out of uncertainty‼️ 6️⃣Best Practices to Reduce Risk🧊 ✔️Use a low-value wallet for interactions, quests, and airdrop hunting. ✔️Keep high-value assets isolated — ideally in cold storage. ✔️Avoid granting unlimited approvals; limit allowances whenever possible. ✔️Always verify URLs and signature prompts. ✔️Never approve operations that seem unrelated to what you intended to do. Your strongest defense is simple: ⛔Don’t click blindly. Don’t sign blindly. 🔗Details: slowmist.medium.com/beware-of-sola…

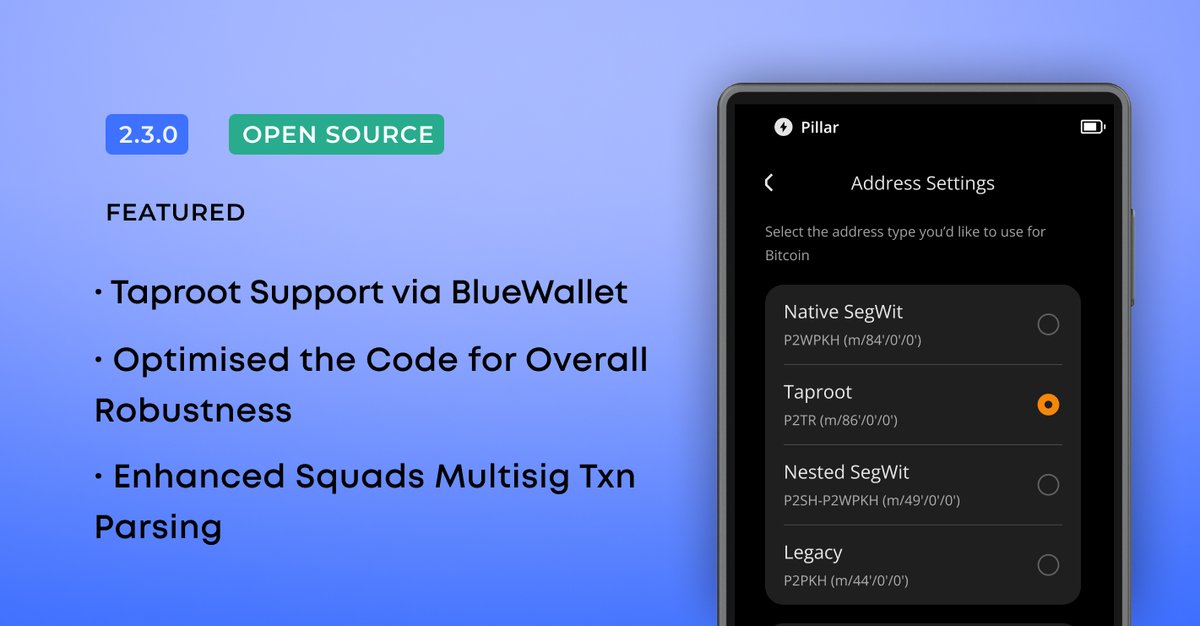
Our Solana CLI integration beta testing is LIVE 🚀 Already shown your interest? Check your DMs, you're in! You’ll be among the first to experience what we’ve built. Missed the call? Drop a comment. No Keystone? We got a special discount for you. Let’s build Solana together.



i really like zashi wallet for zcash its a hot and a HD wallet your hot wallet has one recovery seed and you can hardware wallet with a keystone (seperate seed) but you can plug in your keystone to your phone, and you can use a hardware wallet from your phone.. pretty cool zillions






If you’ve ever said, “I’ll buy a hardware wallet later,” That "later" is today 🎉 Our Black Friday Sale is live with 20% off on everything till Dec 5. All at the lowest price of the year. Secure your bags now & remind your hot-wallet friends to grab one!

Day 1 is now OPEN! You can win a FREE @KeystoneWallet Pro 3 device by entering the raffle in our Advent Calendar. More details below ⤵️

Day 1 is now OPEN! You can win a FREE @KeystoneWallet Pro 3 device by entering the raffle in our Advent Calendar. More details below ⤵️