SlowMist
4K posts


SlowMist
@SlowMist_Team
SlowMist is a Blockchain security firm established in 2018, providing services such as security audits, security consultants, red teaming, and more.






🎙️ Cregis MicUp Vol 13: When Agents Take the Wheel — What Does the New Era of Crypto Infrastructure Look Like? 🗓️ May 13, 2026 | 5:00 PM GMT+8 | Live X Space 🔗 Set your reminder: x.com/i/spaces/1Xxyg… AI Agents are rapidly moving from concept to execution. Across crypto, finance, payments, and security, the industry is racing to integrate AI into workflows, operations, and infrastructure with the promise of greater efficiency, automation, and intelligence. But what can Agents actually do today? Where are the real limitations? And what risks emerge when autonomous systems begin interacting with financial infrastructure at scale? Join Cregis for a forward-looking discussion on how AI Agents are reshaping crypto infrastructure and what the next era of Web3 may look like. 🎤 Meet Our Expert Panel: Tony Tan — HK Community Lead at @SlowMist_Team Constance Zhou — Marketing Manager at @InterlaceMoney @xsser_w — CEO at Tanwei Dujian Technology Mike — Chief Researcher at @NeoSoulAI 🎙️ Moderated by Bovey 📋 What We’ll Explore: 🔸 Why Is Everyone Betting on AI? Why is the industry moving so aggressively toward AI adoption? What real strategic value does AI bring to crypto infrastructure and financial systems? 🔸 What Can Agents Actually Do? Beyond the hype, what are the real capability boundaries of AI Agents today across security, payments, operations, and research? 🔸 The Enterprise Reality — Risk, Cost & AI Deployment: What challenges are companies underestimating when integrating AI? From security and permissions to operational cost and team readiness, what lessons have emerged in practice? 🔸 Living Alongside AI — Opportunities, Risks & the Future: If AI becomes deeply embedded into finance, payments, and everyday decision-making over the next decade, what could that world realistically look like for ordinary people? Why This Matters: AI is no longer just a tool — it is becoming part of the infrastructure layer itself. As autonomous systems gain more responsibility across crypto and finance, understanding both their potential and their risks becomes critical for builders, enterprises, and users alike. This session brings together voices from security, payments, AI research, and infrastructure to explore what happens when Agents begin taking the wheel. 📌 Join us 5 minutes early to secure your spot! #AI #AIAgents #CryptoInfrastructure #DigitalAssets #CyberSecurity #Payments #CregisMicUp









🚨 Big Security Drop Incoming (sometime this week) – Pure Wallet x SlowMist Spaces Teaser 🚨 Hey PureWallet Army! 👀 Something major is cooking… We’re teaming up with @PureWalletPlus & @SlowMist_Team — one of the top blockchain security powerhouses — for an exclusive X Spaces on Security in DeFi & Fintech. Expect deep dives into: • Real-world wallet threats & how to stay protected • Military-grade offline security in action • ISO-certified standards vs. the wild west of DeFi • Future of trust, audits, and threat intelligence This is your chance to hear straight from the experts building the most secure mobile cold storage solution in crypto. Date & time dropping very soon — Set your reminders and turn on notifications! Who’s ready to level up their security game? Drop a 🔥 below if you’re tuning in! #PureWallet #SlowMist #DeFiSecurity #CryptoSecurity #Web3 x.com/PureWalletPlus…

We're proud to announce that our smart contracts are now undergoing a full audit with @SlowMist_Team. We believe true innovation only thrives with ironclad security and transparency. Audit report coming soon!





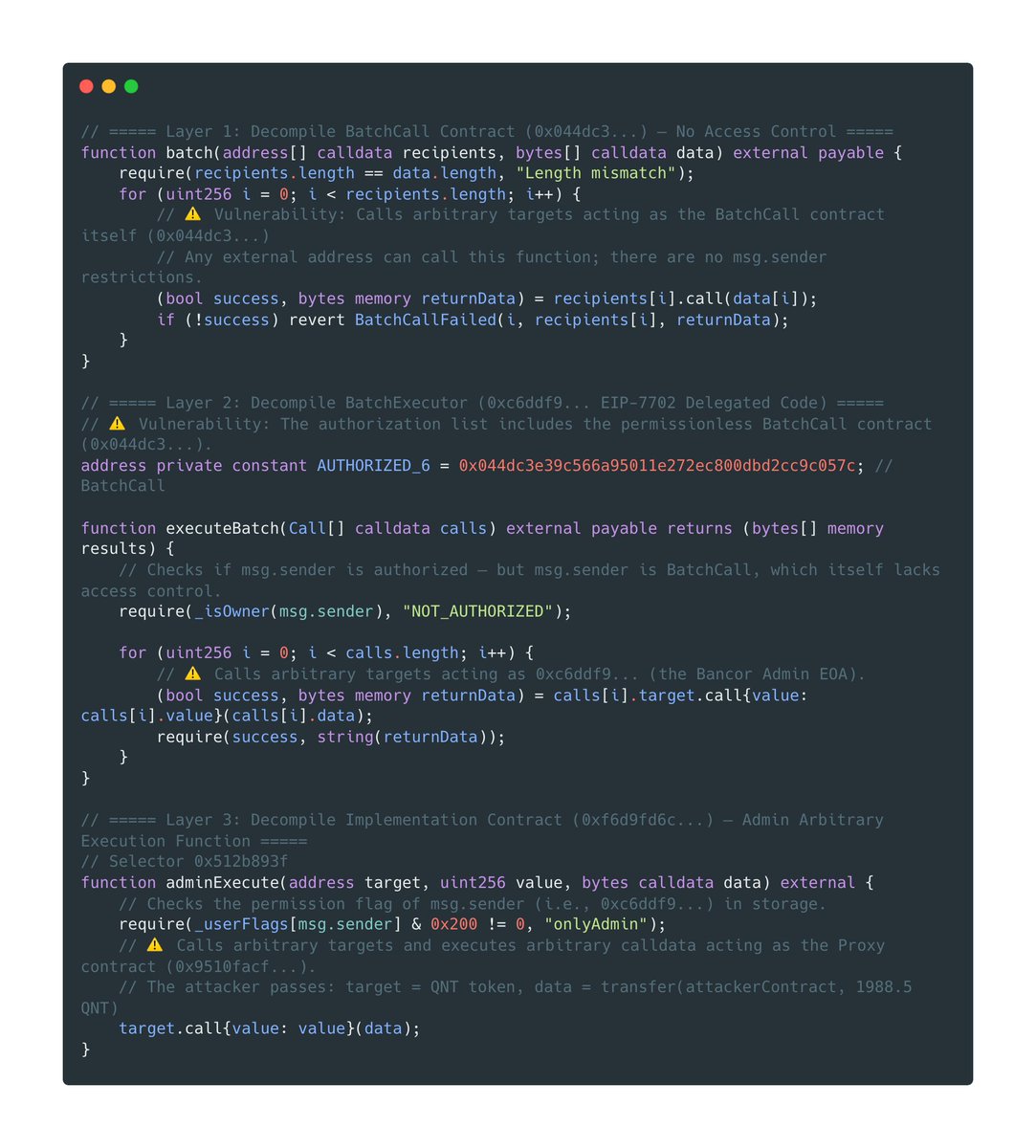



There was an attack against the ZetaChain GatewayEVM contract today that impacted the internal ZetaChain team wallets only. We've already blocked the attack vector so no more funds can be compromised and will be releasing a detailed post mortem after we have completed our investigation. As a precaution cross-chain transactions are currently paused on ZetaChain. Investigation is still ongoing and at this time no user funds were impacted by this attack. The current status can be tracked at status.zetachain.com.