Закреплённый твит
Quantova
132 posts


Quantova
@QuantovaGlobal
Foundational blockchain platform powering decentralized apps, stablecoins, and post quantum resistant smart contracts via QVM.
Zug, Switzerland Присоединился Haziran 2023
113 Подписки19.1K Подписчики

@Joseph_Kearney Fair point
The conversation should be about how to prepare, not whether the risk exists
English

Embarrassing at best. Some of the biggest names in quantum computing explicitly say this is an issue. And you get a group of amateurs to come on your show and say it's not a issue.
Then you just make up how physics works 😂.
I said it last time you posted this shit. Zero probability, scientifically is absolute certainty, are these "physicists" willing to personally guarantee that there is a "ZERO" risk.
Simply Bitcoin@SimplyBitcoin
Jeff Booth, Nick & Jack explain how there is ZERO risk of quantum attack on Bitcoin Few understand.
English

Some users don't care too much about decentralization.
Some users don't think too much about security in general, or post-quantum security in particular.
Some users don't care about verifiability and all this technical stuff. That's understandable.
But builders should care about it. A lot. All the time.
That's the job.
English

@Cloudflare How should systems reason about security once it becomes time dependent (latency, exposure windows)?
English

We’re recording a new ThisWeekinNET.com episode soon with Bas Westerbaan, Principal Research Engineer at Cloudflare, on post-quantum cryptography.
What does post-quantum mean right now? Why is it back in the news? What should people know?
Reply here with your questions.
English

🚨TODAY: @coinbase ramps up efforts on post-quantum security.
Urging coordinated action as @brian_armstrong says the industry must address quantum risks “sooner rather than later.”


English

@asanso @GiulioRebuffo how are you handling key lifecycle and reuse bounds with this setup?
English

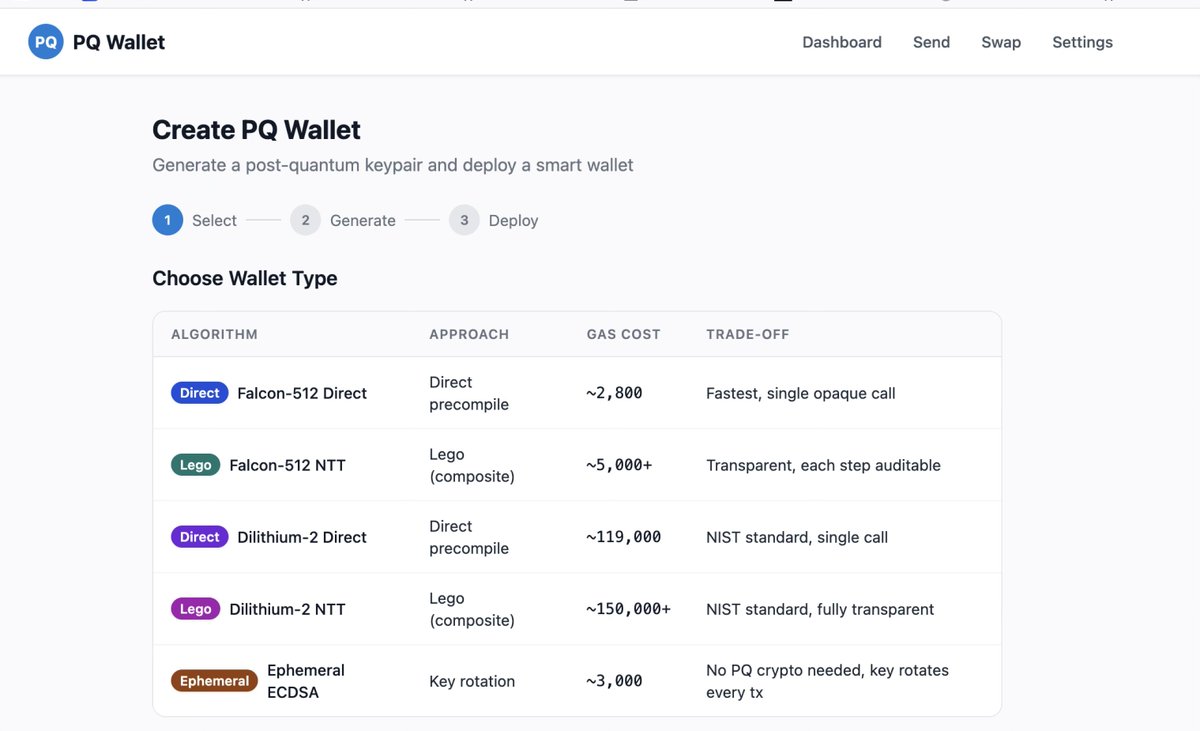
Dropping a new testnet for post-quantum signatures.
This one implements the PQ signature scheme we’ve been discussing so far: Falcon and an ephemeral key.
Would love feedback from folks kicking the tires. More details soon. Kudos to @GiulioRebuffo. link👇
English

@AbdelStark @blksresearch Does batching SHRIMPS inside STARKs actually offset
the signature size + verification overhead?
English

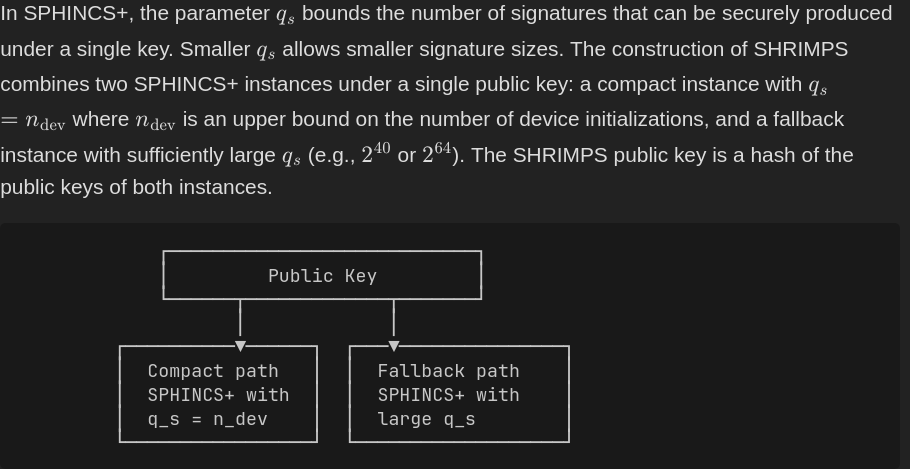
Provable SHRIMPS: Post-quantum hash-based signatures verified in Cairo with STARK proofs.
As usual @blksresearch is killing it on the post quantum bitcoin research.
SHRIMPS 🦐 is so cool that I made provable shrimps, it could be useful to for batch shrimps signature verification.
Don't panic, as @adam3us said:
"SHRIMPS & bitcoin quantum readiness > quantum FUD."
Jonas Nick@n1ckler
Please welcome SHRIMPS🦐 to the family of stateful PQ signatures: 2.5 KB hash-based sigs across multiple devices. SHRINCS🛋️ gave ~324-byte sigs but is single-device. SHRIMPS🦐 addresses multi-device; any device loaded from the same seed creates sigs 3x smaller than SLH-DSA
English

@CasaHODL @lopp @nic_carter 1) If verification costs increase under PQ schemes, how does that impact block size and throughput assumptions?
2) Can Bitcoin maintain decentralization under heavier validation load?
English

Two quantum papers in one week, both with estimates way below previous projections. Google is now targeting 2029 for their post-quantum cryptography transition.
We're hosting a Space with @lopp and @nic_carter this Thursday at 1 PM ET to discuss what this means for Bitcoin and the path forward.
What questions do you want answered?
x.com/i/spaces/1aJbd…
English

@pumatheuma @SuccinctLabs ZK based disclosure might become a standard
but attackers don’t need to prove capability, defenders do, not clear that balance holds
English

Google's Quantum AI team used @SuccinctLabs zkVM SP1 for responsible disclosure of a new SOTA quantum algorithm.
Their paper presents a 20x more efficient implementation of Shor's algorithm for cracking secp256k1 keys: the elliptic curve used by Bitcoin and Ethereum.
They believe the attack is so dangerous that instead of publishing the circuits, they instead published a ZKP that the circuits exist.
I wonder if ZK proof of exploit becomes a broader theme in vulnerability disclosures going forward.

English

Google released a paper showing 256-bit ECC may require <500k physical qubits to break in minutes
Once key extraction fits within operational windows, mempool and key exposure assumptions break down.
Post-quantum migration is no longer optional.
That’s exactly the problem Quantova is built to address
English

@Cat_States What happens to systems where key exposure + latency windows become exploitable even before full breaks?
English

🚨 The quantum threat to Bitcoin just got MUCH closer.
We're talking as soon as a year or few.
A decade ago, breaking RSA-2048 or P-256 (what Bitcoin uses) required ~1 billion physical qubits.
Today? As few as 10,000 qubits.
That's not a typo.
A new paper just dropped from Oratomic, a neutral atom startup. Co-author: John Preskill, one of the greatest quantum theorists alive.
The breakthrough is high-rate quantum error correction + neutral atom architecture = dramatically fewer physical qubits.
10,000 reconfigurable atomic qubits. That’s all you need.
Researchers have demonstrated neutral atom arrays of up to 6,000 already.
How much longer will the bitcoin community play with fire?!

English

@Cointelegraph The real issue isn’t a 9 min, it’s that once signatures are exposed the security model around key reuse and mempool behavior starts to break down
That’s a protocol problem, not just a timing
English

@conordeegan Agree on the urgency, but once you move beyond key rotation, PQC introduces different performance and verification characteristics that many systems weren’t designed for
In some cases it’s less migration - - more redesign
English

Migration to post-quantum cryptography is largely a fixed amount of work.
Every system using classical crypto will have to find where it’s used, change how keys are handled, rotate them, etc. That part won’t change.
However, what is changing is the timeline. We keep seeing target dates move forward like this. It’s happening for a mix of reasons: progress on the quantum side, lower resource estimates, and a growing understanding of the risk.
At the same time, nothing fundamental is missing anymore to get started; NIST schemes are standardised, implementations exist, and we have a lot of early working deployments already.
if you are still adding new classical crypto into a system today, you are adding work that will need to be undone.
Time to PQC everything

English