sh4des ретвитнул

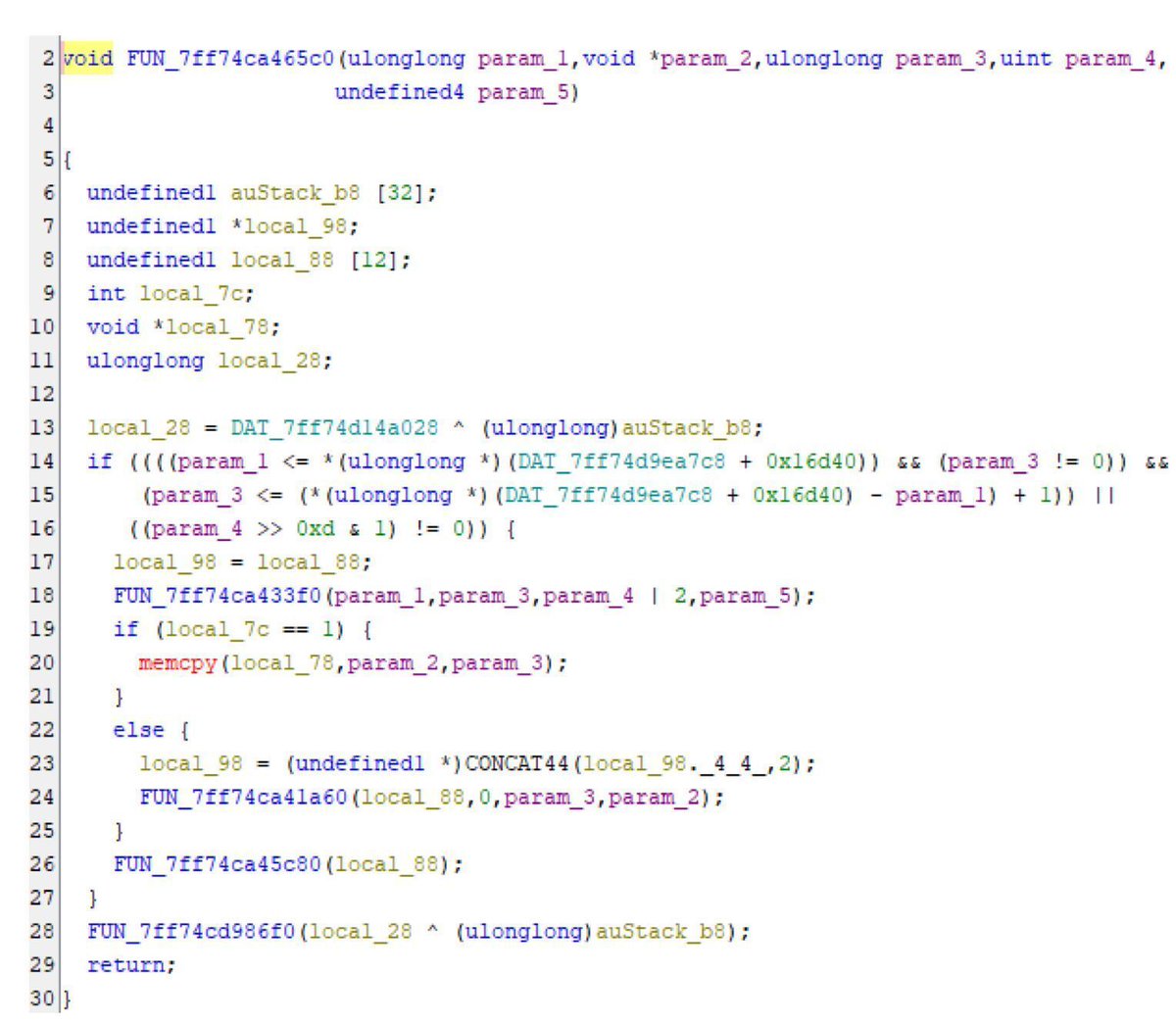
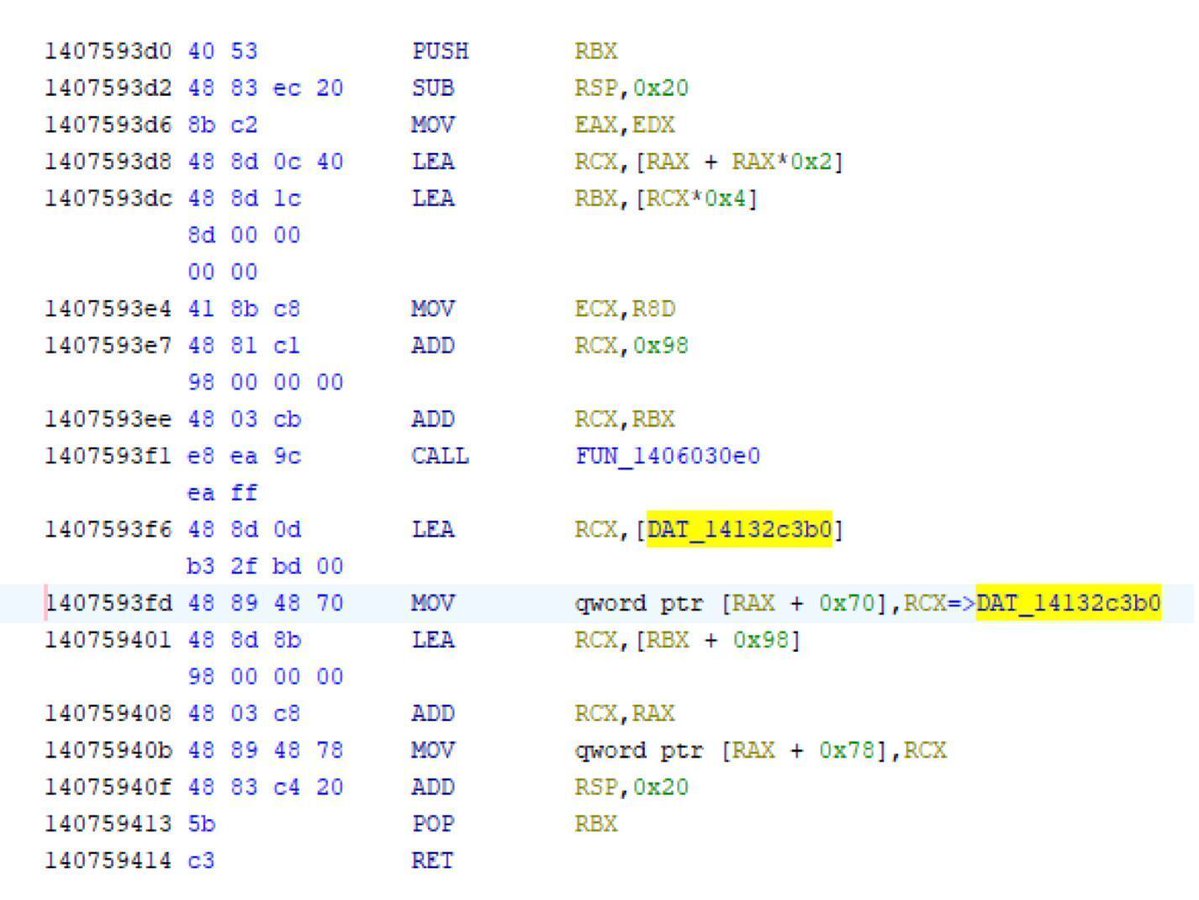
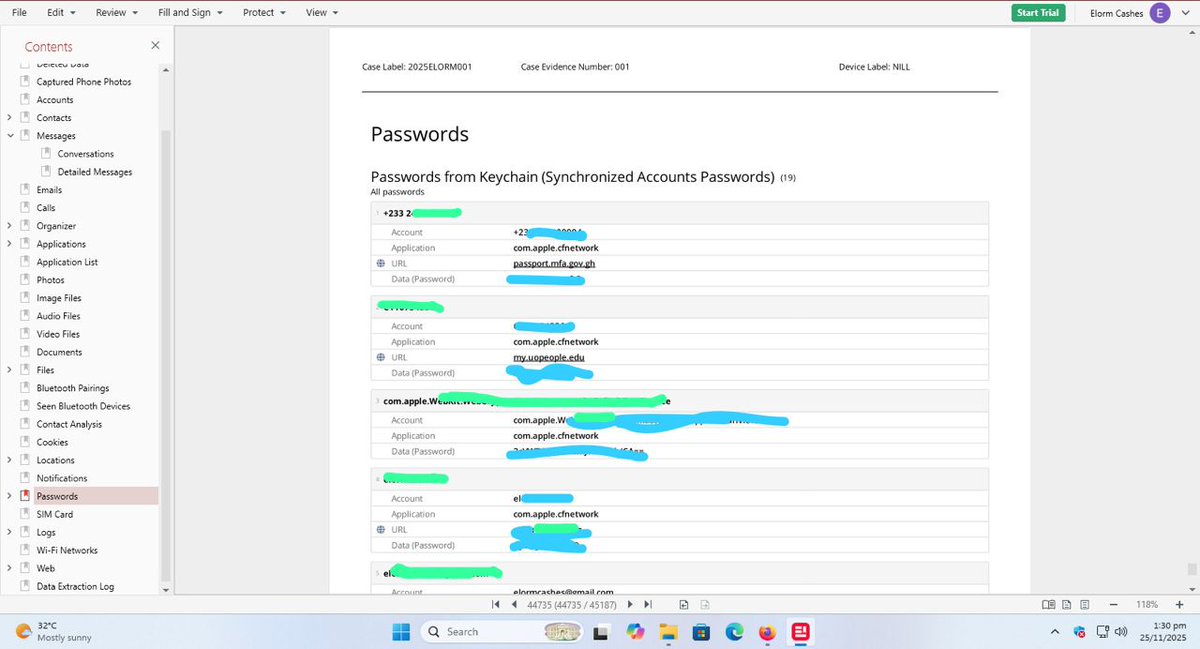
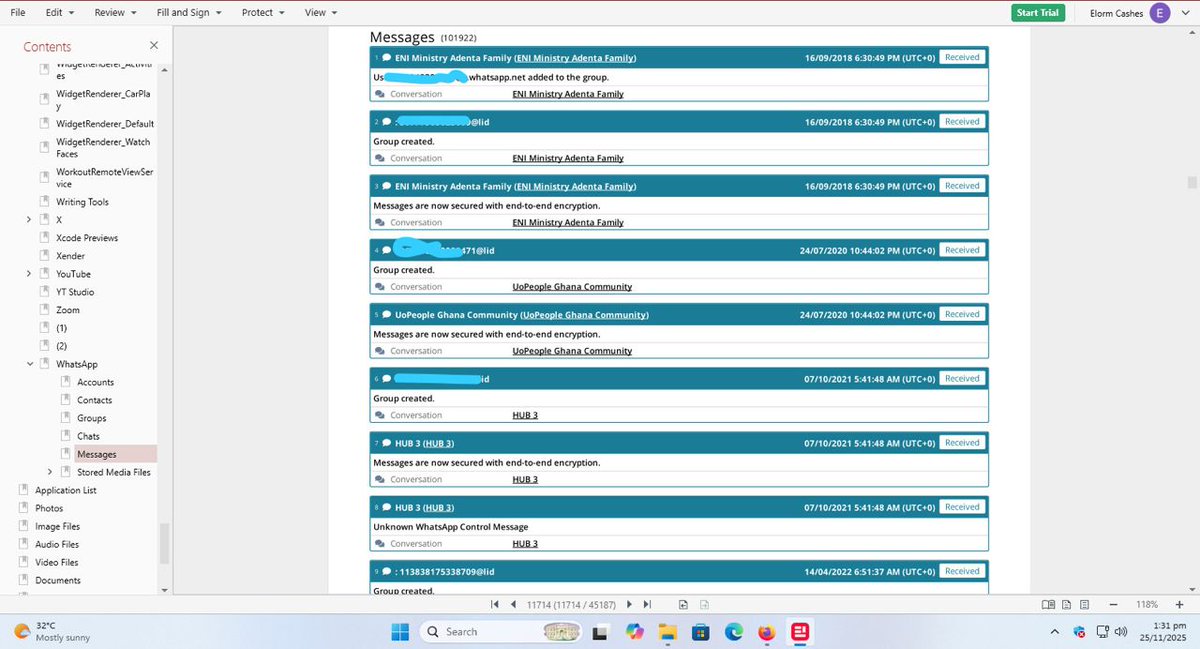
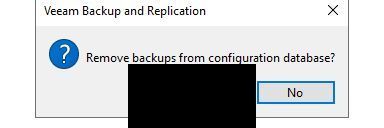
RDP bitmap cache artifacts revealed the threat actor opening the Veeam Backup & Replication console, reviewing backup jobs, tape & storage infrastructure — and removing backups from the configuration database.
Full report 👇
thedfirreport.com/2025/12/17/cat…
English