Exploit5lover 🇵🇰🇵🇸
554 posts


Exploit5lover 🇵🇰🇵🇸
@exploit5lover
Claims to be a Hacker - : 503 and 521 everywhere
pakistan Присоединился Ekim 2022
67 Подписки931 Подписчики

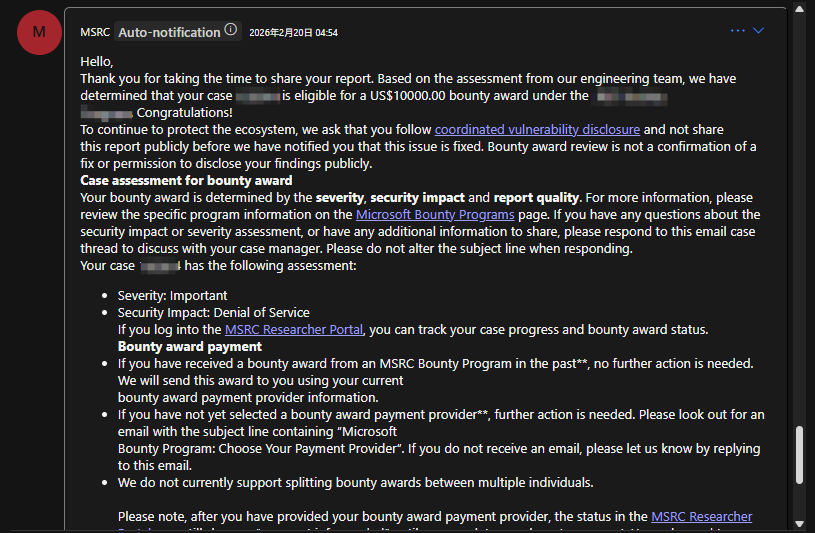
Huge thanks to @msftsecresponse for the $10,000 bounty reward! This report was rated as Important (DoS). Looking forward to the patch!
#bugbounty #cybersecurity #MSRC
English

@exploit5lover i just wanna know the bug cause i ve been hunting on it for a real long time
English

Alhamdulillah.
Chaining vulnerabilities is where payouts multiply.
#BugBounty #bugbountytips
English

@exploit5lover Congratulations brother!
Can you tell me how much you hunt a day ?
English

Read New Write-up: Single request DoS
#BugBounty #BugBountyTip
exploit5lovers.medium.com/classic-single…
English

@Savitar0x01 @Hacker0x01 Masha'Allah, congratulations 👏
Indonesia

published one of my write up- @hossainwalid93/access-to-domino-hcl-server-db-leads-to-mass-pii-leak-11c771bd6354" target="_blank" rel="nofollow noopener">medium.com/@hossainwalid9…
English

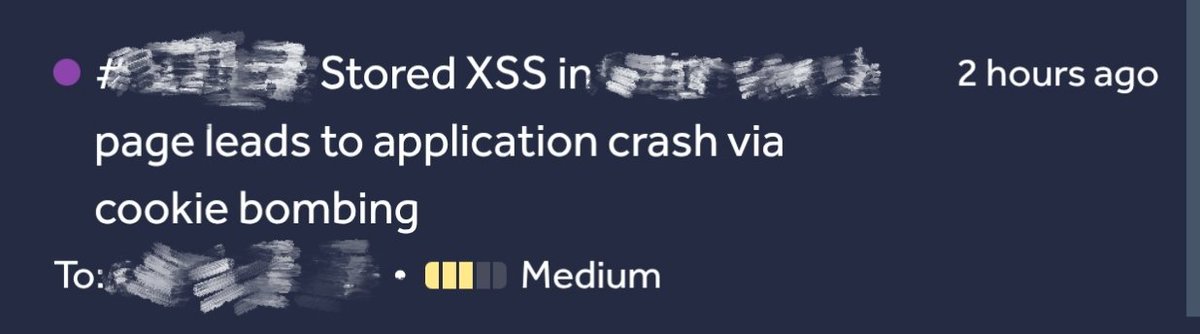
If you find a stored XSS that auto-executes for many users but can’t be escalated further, it may still be abused for user-level availability impact by poisoning cookies at scale, causing requests to fail due to header size limits.
kimu@K3S3l7
When trying to escalate XSS and you don't find a way to do so (cookies protected, sensitive requests protected with otp etc..) Worst case scenario is escalating it to DoS Which is fun and works most of the time + can increase severity a little bit since A vector will be set
English

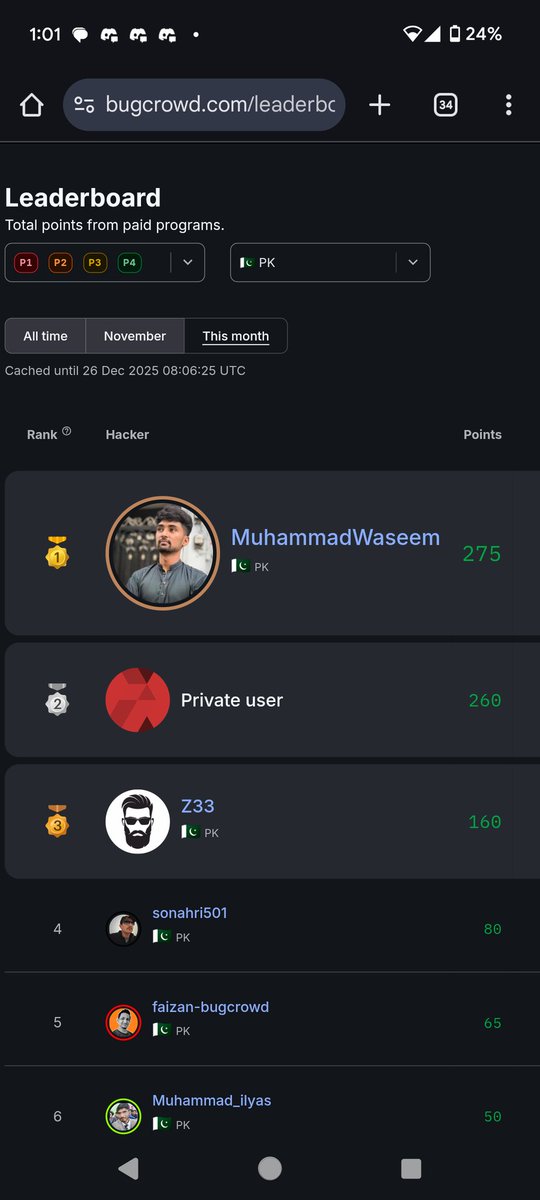
@wgujjer11 @Bugcrowd If you are a noob , what about us then 😂
English

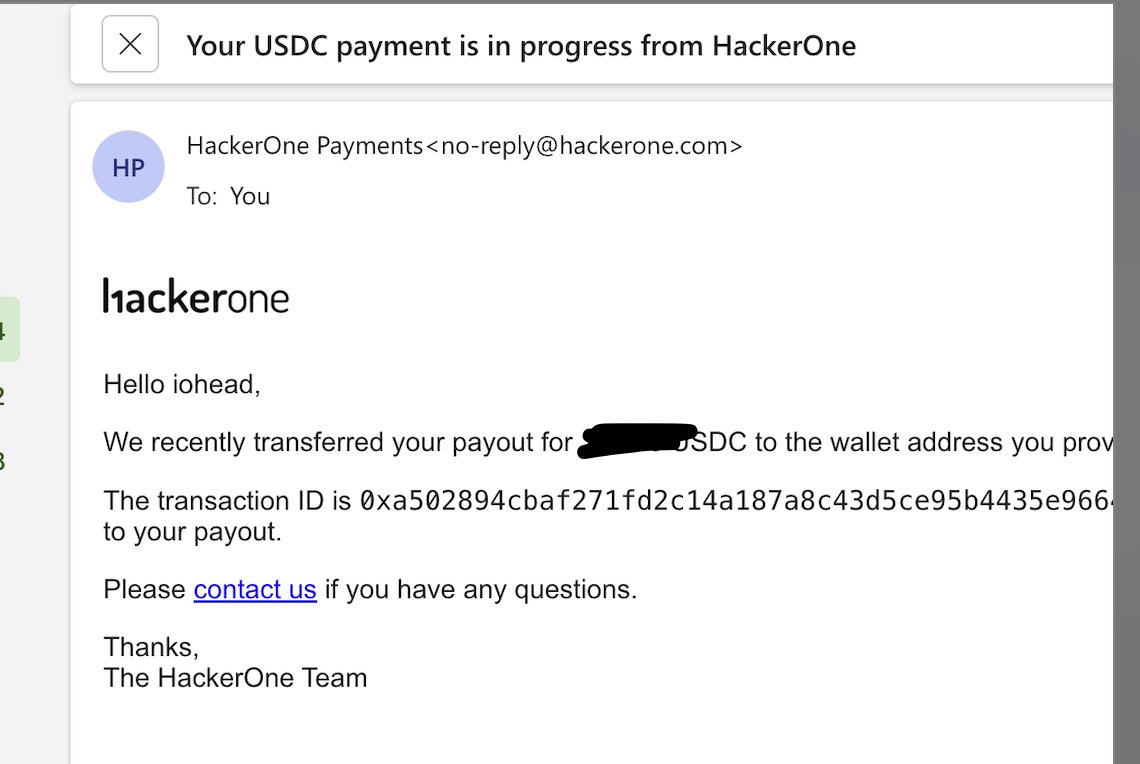
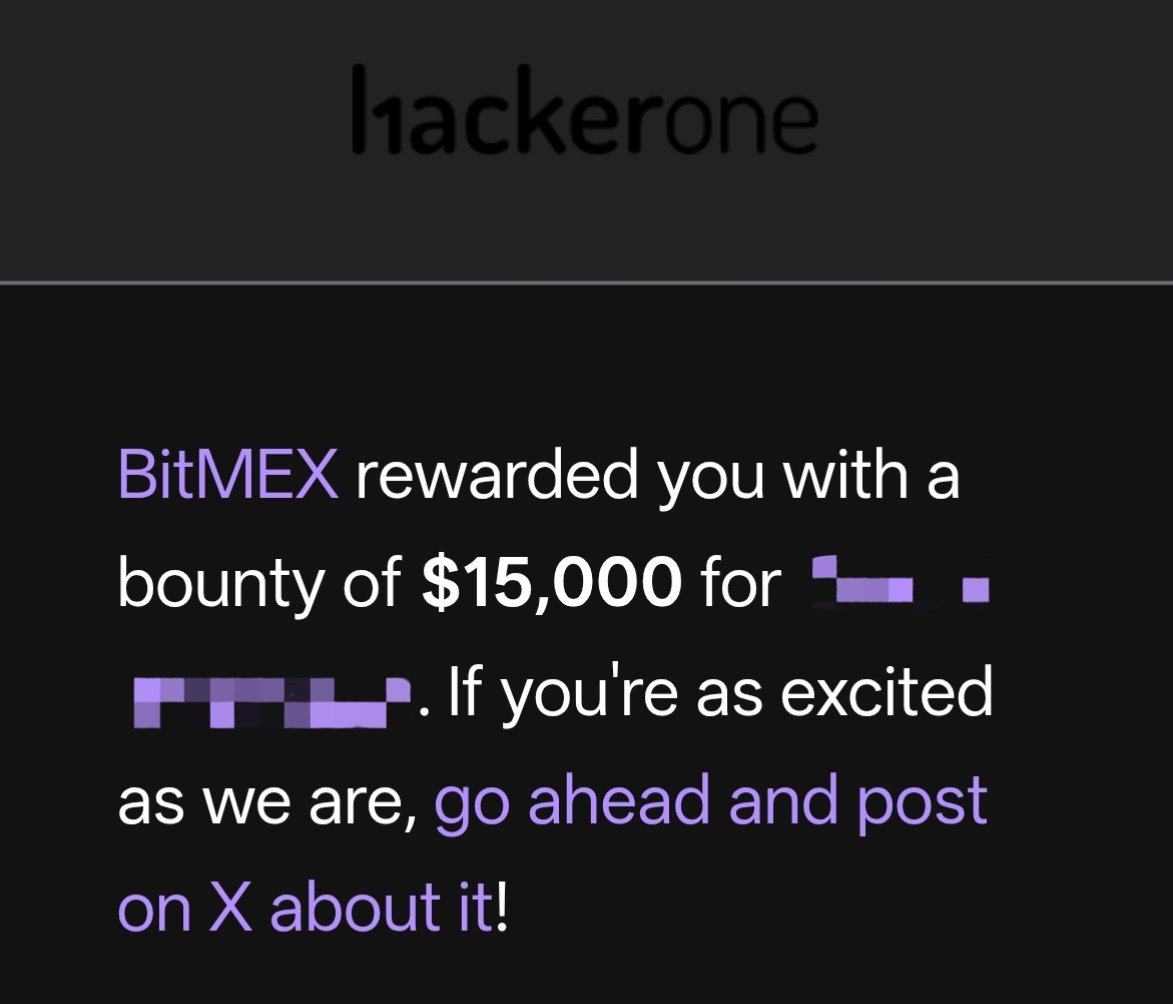
Alhamdulillah,
Second last bounty of this year. In the last two months I tried to focus on quality not quantity.
And yes! I’ll definitely share tips with all of you, though I am not an expert.
#BugBounty #hackerone

English

@ma1fan @hackerone Congratulations. Brother, what wallet are you using to receive USDC .
English