Fallen Apple 🍎
611 posts


Fallen Apple 🍎 retweetledi

IDOR hunting workflow I keep coming back to:
1) Map object IDs (UUIDs, ints, slugs) across endpoints (REST + GraphQL).
2) Change one dimension at a time: user_id, org_id, project_id.
3) Watch for soft failures: 200 with partial data, empty arrays, unexpected responses.
4) Test non-GETs too: PATCH/DELETE often skip the same checks.
5) Test for different paths/platforms: UI vs API vs mobile vs webapp.
Most IDORs aren’t fancy, they’re just inconsistent, and it only takes one.
English

Took me 2 and half hour. But challange was awesome!

AmirMohammad Safari@AmirMSafari
Can you spot the XSS vulnerability? 👀 Test it out live at: pwnbox.xyz
English

@exploit5lover Congratulations brother!
Can you tell me how much you hunt a day ?
English

Alhamdulillah.
Chaining vulnerabilities is where payouts multiply.
#BugBounty #bugbountytips
English

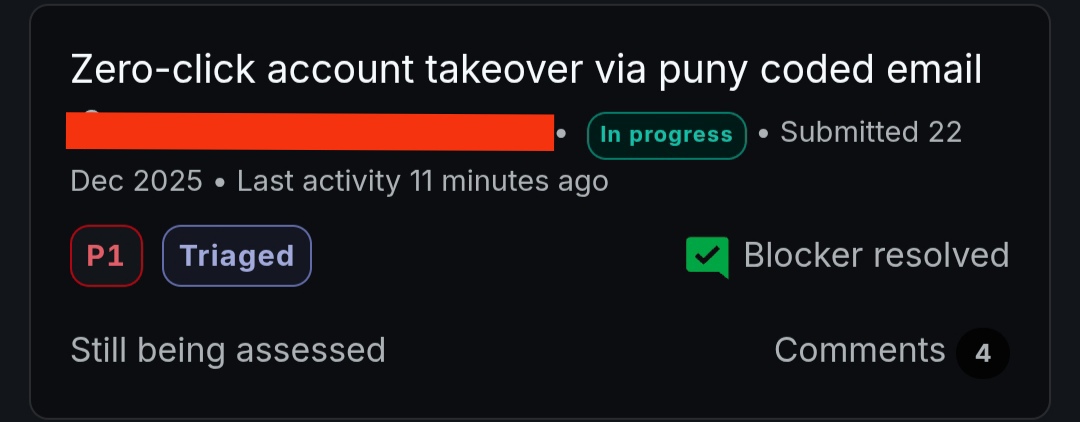
@intigriti Via postmassage where oauhtData sent to wildcard. Attacker phish the user to their page and open a window for fetch data.
English

@fallenapplle @TakiasSec Good evening please I will like to connect with you privately
English

H1/Bugcrowd public programs are really hard for me. Any tips for that?? 🫡
#bugbounty #cybersecurity
Bangladesh 🇧🇩 English
Fallen Apple 🍎 retweetledi

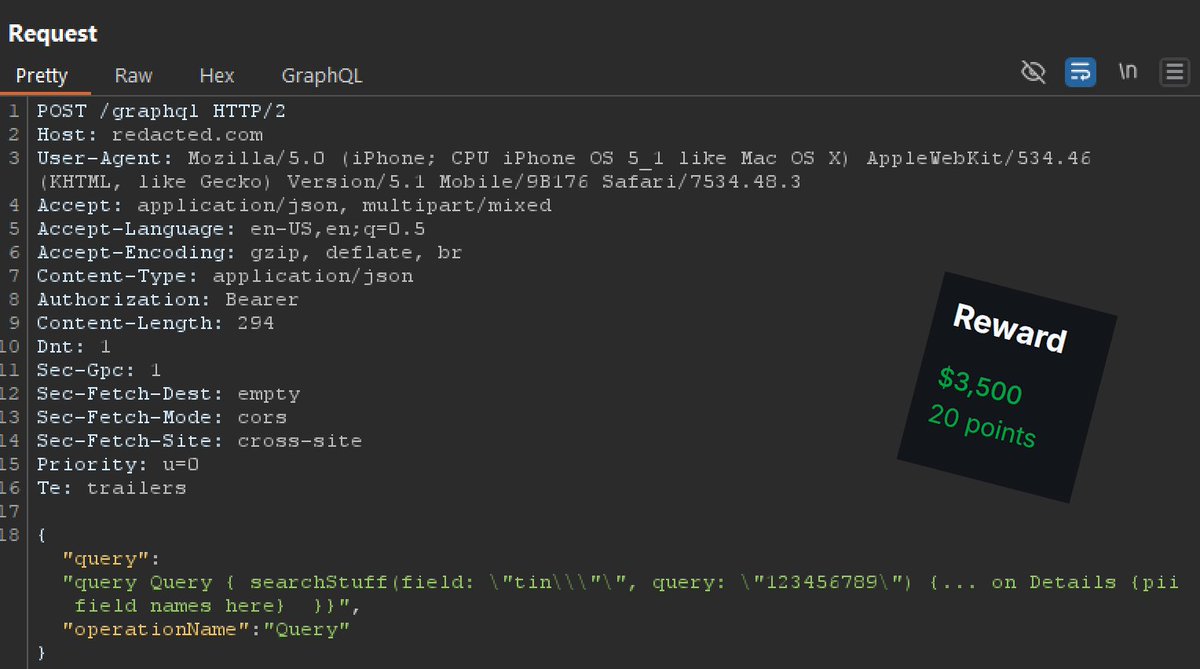
Weird graphQL IDOR / access control bypass:
In this one, graphQL would check the "tin" (tax identification number), if supplied, against the Bearer token. If the Bearer did not have access to the tin, you would get access denied. Normal stuff there. So my thought was, how could I make the server still lookup the tin value without the access check?
It regularly expected:
\"tin\"
This causes the server, since "tin" is present, to check access control prior to returning data.
What worked was:
\"tin\\\"\"
So adding \\\" after tin bypassed the access control logic (for some reason), meanwhile the graphQl query still ran and sent back the PII for any TIN I sent it.
#bugbounty is just strange sometimes. Some of the battle is finding neat endpoints and places, and some of it is endless tinkering.
English
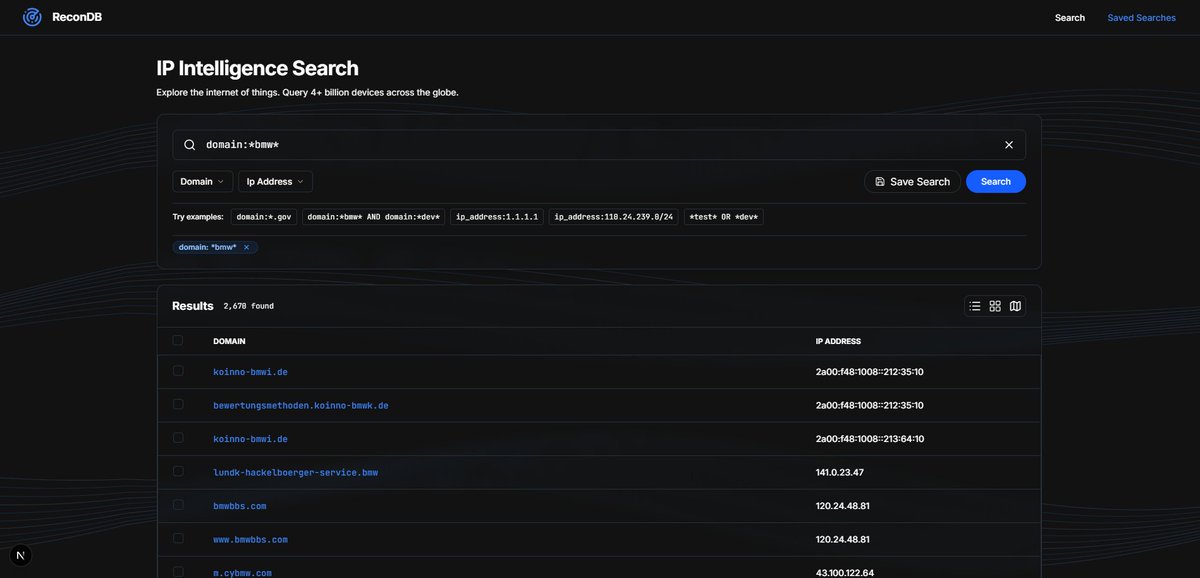
Seeing a lot of new tools using the THC API, but it doesn't support this level of search and filtering. Raw THC datasets + ELK is the right way to do it 💪 Open-sourcing this very soon.
#bugbountytip #bugbounty #recon #programming
English
Fallen Apple 🍎 retweetledi
Fallen Apple 🍎 retweetledi

🚨New Salary as Per 8th Pay Commission
Teacher :-₹85,000
Doctor :- 1,30,000
Judge :- 1,50,000
Scientist :- 1,40,000
Peon :-₹45,000
Clerk :-₹50,000
Postman :-₹55,000
SI. :-₹80,000
Head Constable :-₹69,000
ASI :-₹76,000
Junior Engineer :-₹92,000
Inspector :-₹1,20,000
Section Officer :-₹1,29,000
IAS / IPS / IFS :-₹1,55,000
IAS / IPS (Senior Scale) :-₹2,10,000
Secretary to the Gov of India:-₹3,00,000
Note: Above Figure Contain Basic Salary Only. DA, HRA, TA, Uniform Allowance, and Risk Allowance will be an additional 25-50%.
English
Fallen Apple 🍎 retweetledi

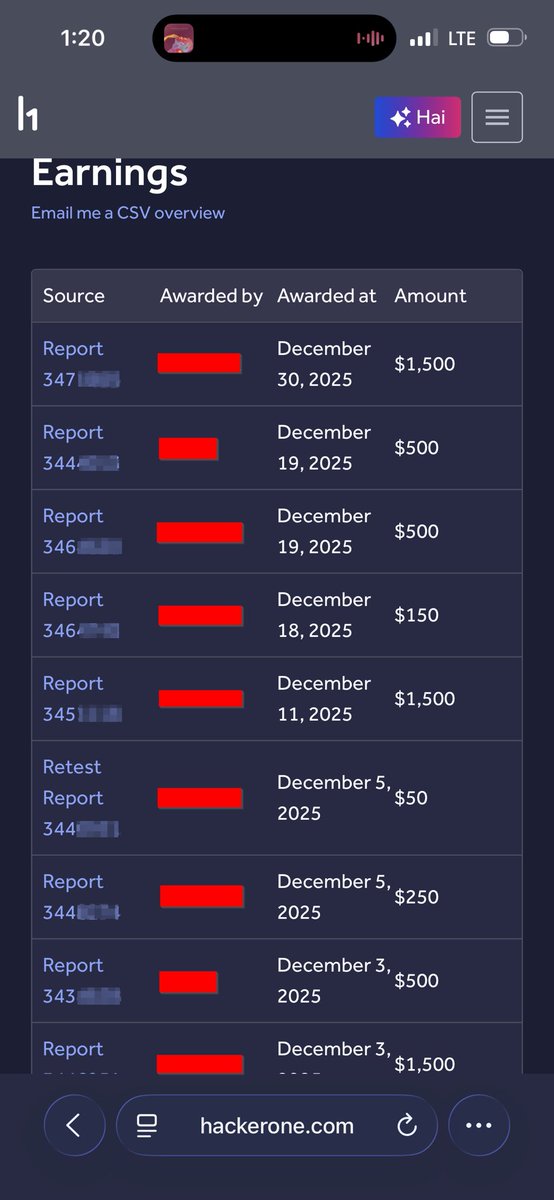
Late one, hunted for 2 weeks in December and made $6000+. Excited for what we can achieve this year. Below are some writeups I published in 2025:
$1,500 Recon Tips: @tinopreter/1-500-recon-secrets-dorks-to-dollars-0e7eca022708" target="_blank" rel="nofollow noopener">medium.com/@tinopreter/1-…
Lets $ Leak $ OTP: @tinopreter/otps-for-everyone-the-simplest-otp-leak-youll-ever-find-5ff2d7d9c812" target="_blank" rel="nofollow noopener">medium.com/@tinopreter/ot…
From 429 to 200: medium.com/bugbountywrite…
English
Fallen Apple 🍎 retweetledi

how to hack discord, vercel and more with one easy trick
kibty.town/blog/mintlify/
English
Fallen Apple 🍎 retweetledi

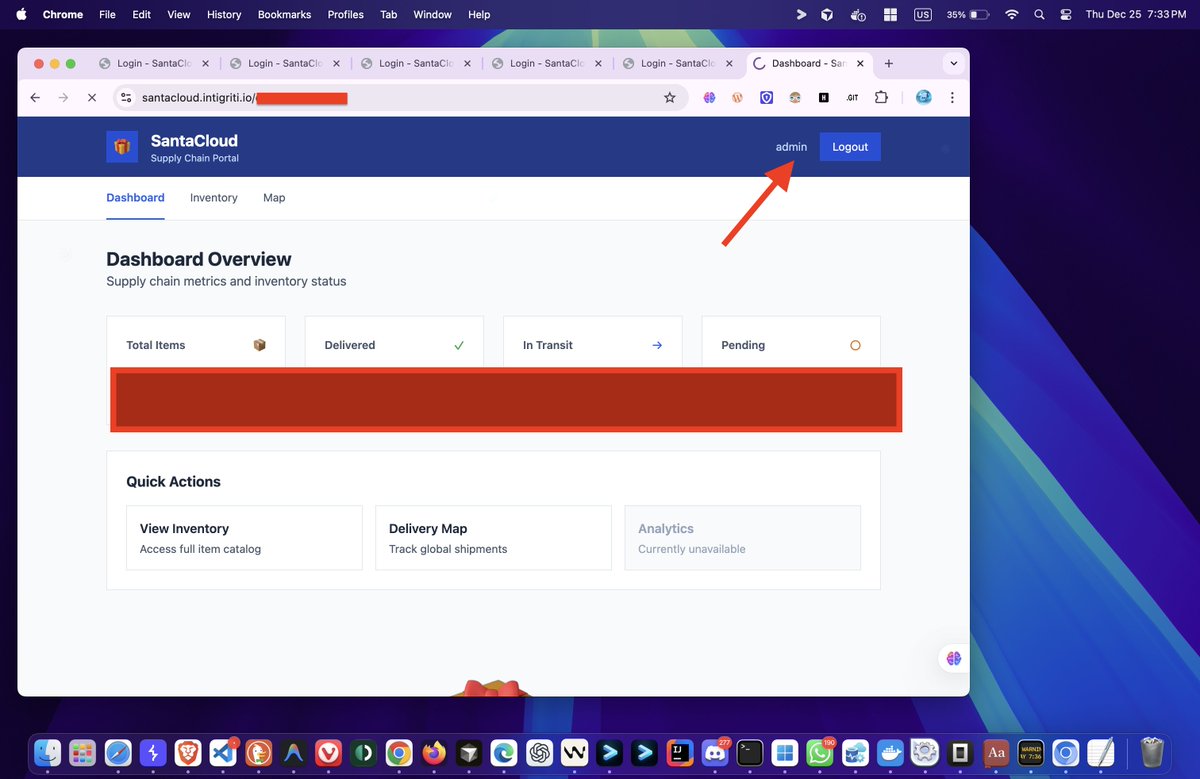
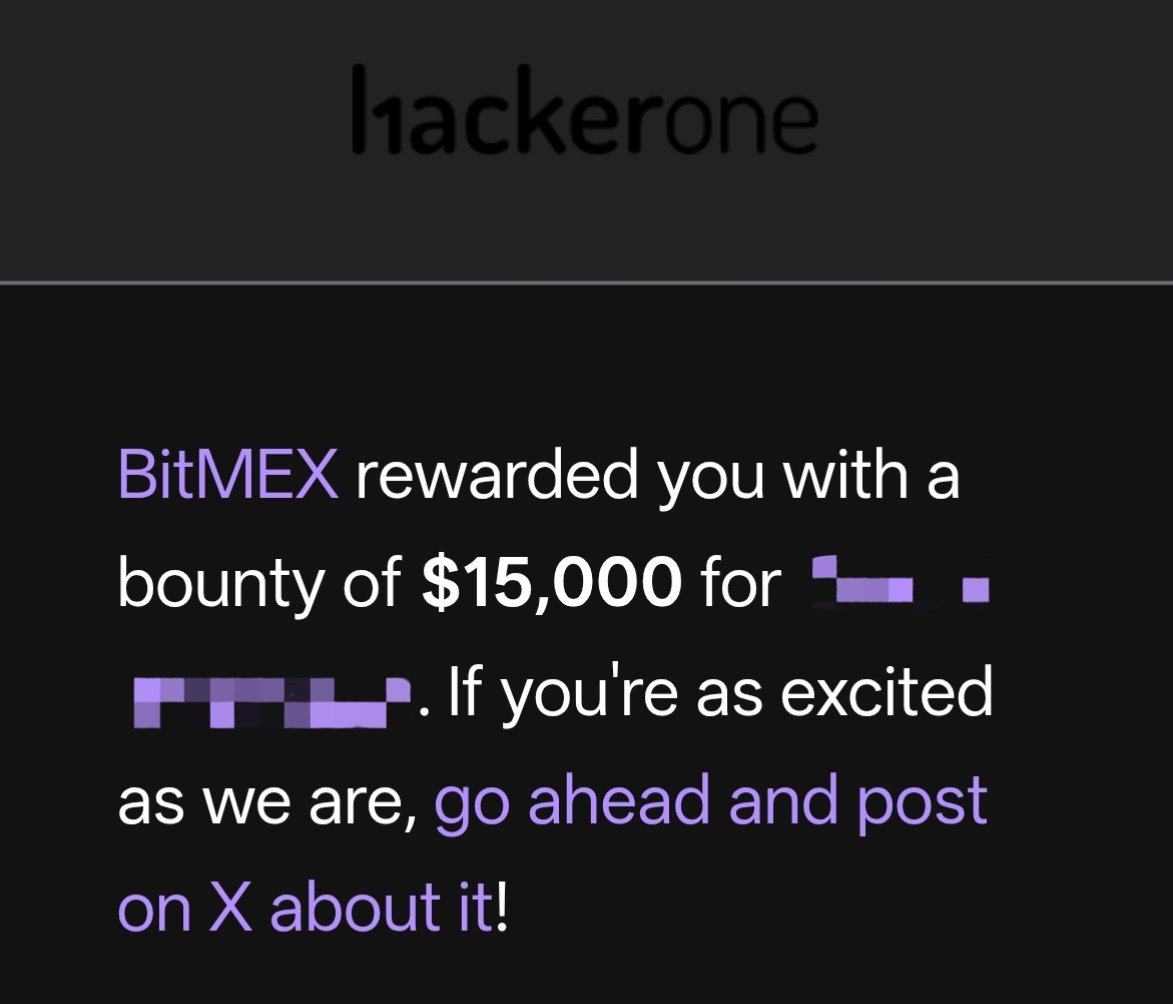
Alhamdulillah,
Second last bounty of this year. In the last two months I tried to focus on quality not quantity.
And yes! I’ll definitely share tips with all of you, though I am not an expert.
#BugBounty #hackerone

English