
whynotsecurity
15 posts







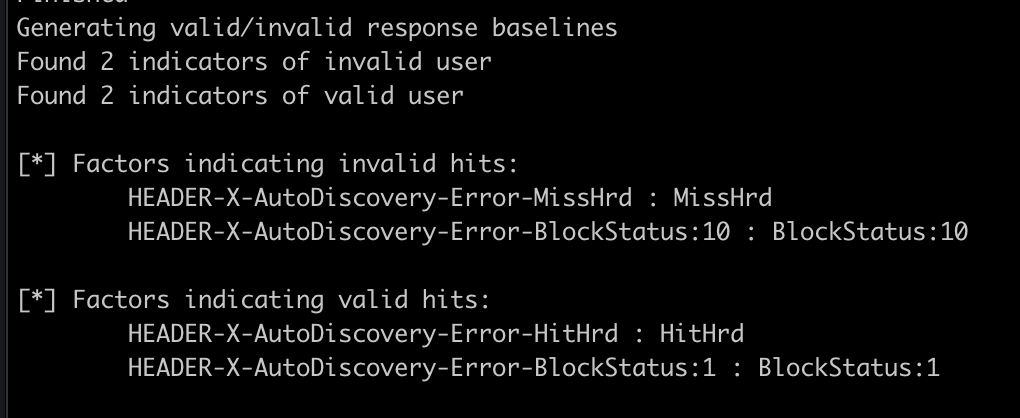
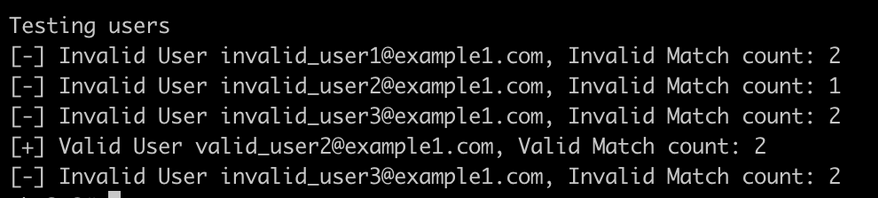
EyeWitnessTheFitness: create a single Fireprox API that can pass thru to multiple web endpoints. No need to generate multiple APIs to do enum, more opsec friendly, and helps bypass scan prevention techniques that filter by IP B: whynotsecurity.com/blog/eyewitnes… G: github.com/knavesec/EyeWi…


Since it was made public, time to release! Big "External Email" phishing warnings on Outlook webapp & client can be obfuscated with some simple CSS/HTML injections into your phishing email. Writeup, Remediations & POC: whynotsecurity.com/blog/external-… #RedTeam




Its national dog day, so naturally its time to release an update on Max! This update includes a new attack primitive with how it works, as well as some new features to a few of the old functions for better data extraction. Post: whynotsecurity.com/blog/max2/



