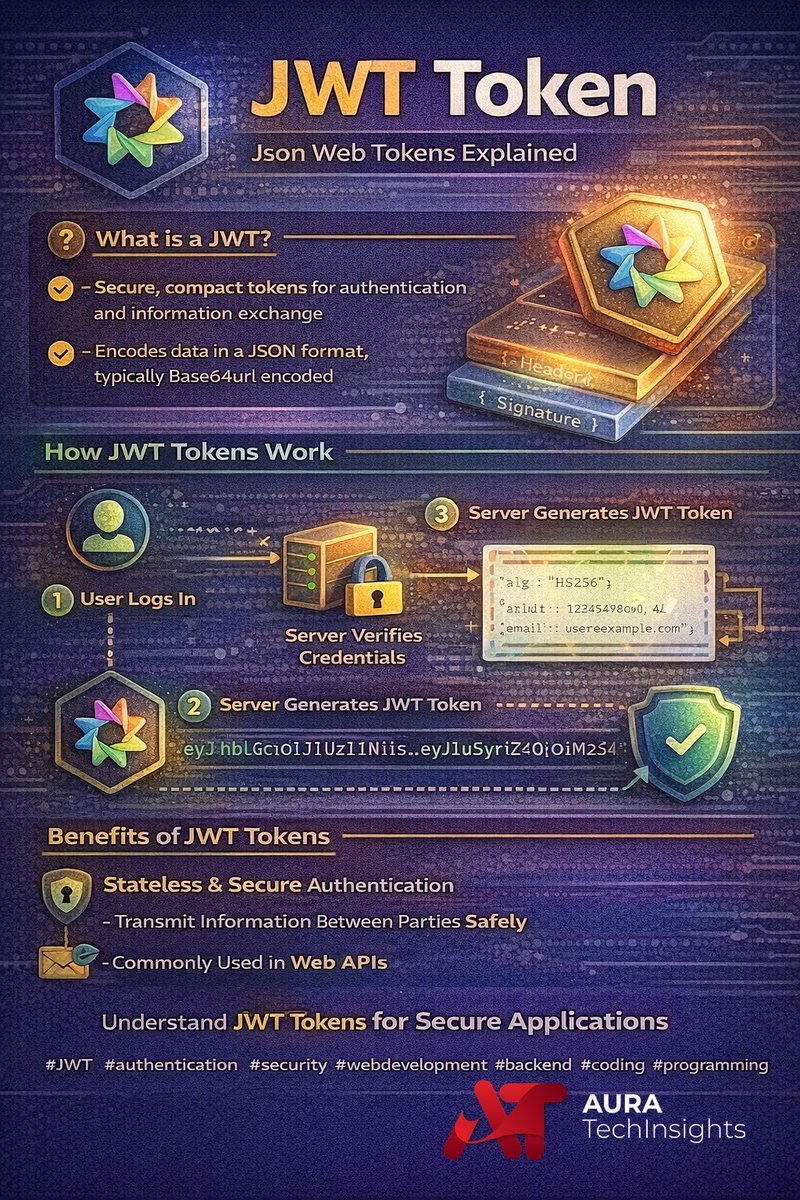
JWT is dead? 😳 Just watched a great breakdown on PASETO tokens. It seems they solve some major security issues and algorithm headaches with JWT.
What are your thoughts on switching to PASETO? Is JWT still king? 🚀
#coding #jsonwebtoken #PASETO #webdevelopment
English