5hid
788 posts


@5hid_
Cyber Security & Malware Analysis enthusiast




Check out our new post!! Analyzing NotDoor: Inside APT28’s Expanding Arsenal lab52.io/blog/analyzing… #APT28







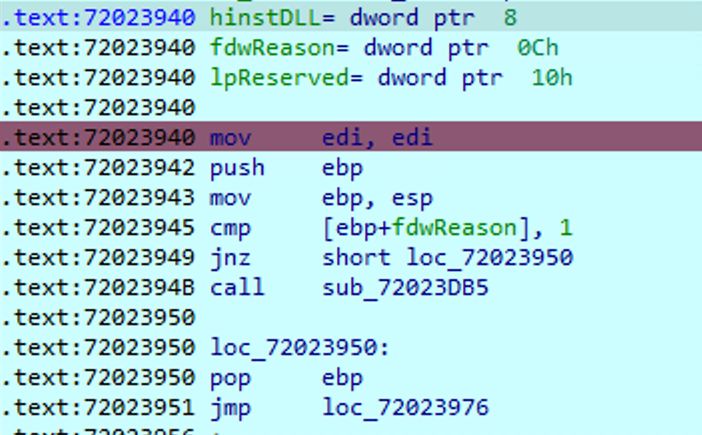
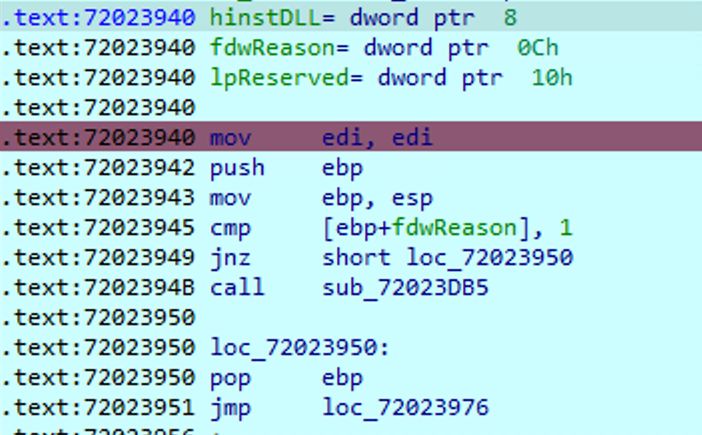
🚨 Notepad++ DLL Hijacking Vulnerability Let Attackers Execute Malicious Code Read more: cybersecuritynews.com/notepad-hijack… A newly discovered DLL hijacking vulnerability in Notepad++, the popular source code editor, could allow attackers to execute arbitrary code on a victim's machine. Tracked as CVE-2025-56383, the flaw exists in version 8.8.3 and potentially affects all installed versions of the software, putting millions of users at risk. The vulnerability enables a local attacker to achieve code execution by planting a malicious DLL file in a location where the application will load it. This type of attack undermines the integrity of the application and can be used to establish persistence or escalate privileges on a compromised system. #cybersecuritynews #vulnerability









