

BINSEC Team @ Université Paris-Saclay, CEA, List
649 posts


@BinsecTool
Binary code analysis for security / Academic research (Infosec, SE, FM, AI) / Open-source tool / Applied in industry / Posts by @michaelmarcozzi and @Seb_Bardin




Interested in binary code analysis for security and reverse? The *BAR workshop* comes back for its 8th edition, once again with @NDSSSymposium in beautiful SanDiego. Submission 13 Jan 2026, Workshop 27 Feb 2026 ndss-symposium.org/ndss2026/submi…


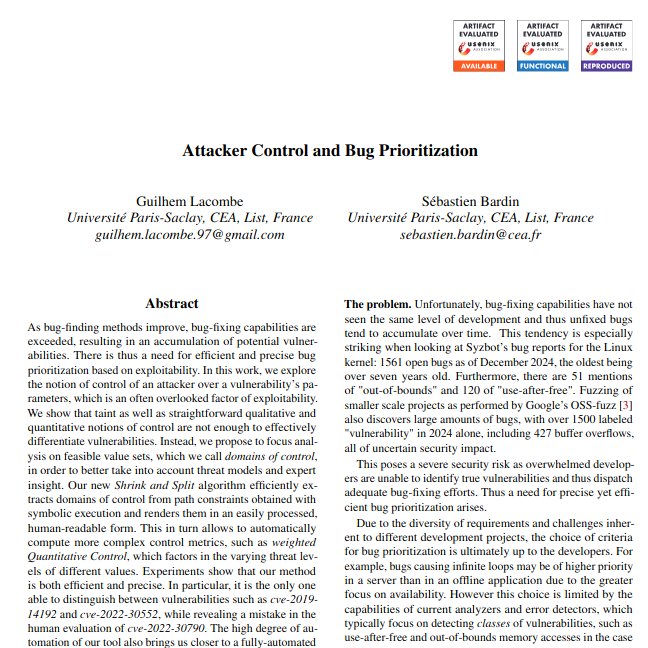














How to detect backdoors efficiently? ▶️ Backdoors were found in firmware & open-source code ▶️ Detection requires much manual reverse-engineering ▶️ Fuzzers cannot see backdoors Our @ICSEconf preprint on finding backdoors with fuzzing is at binsec.github.io/nutshells/icse… A thread ⬇️