ทวีตที่ปักหมุด
Composable Security ⛓️💥
853 posts


Composable Security ⛓️💥
@Composable_Sec
Liquid (Re)Staking and Off-Chain Components Security Audits Worked with: @LidoFinance @UniswapFND @redstone_defi @YieldNestFi @0xOthentic
Let us help 🔎🐛 เข้าร่วม Ekim 2022
93 กำลังติดตาม932 ผู้ติดตาม
Composable Security ⛓️💥 รีทวีตแล้ว

@OpenAI and @paradigm developed a benchmark evaluating the ability of AI agents to detect, patch, and exploit high-severity smart contract vulnerabilities.
Here are my takeaways from the EVMbench paper:
1⃣ Security Researcher
- In-depth human audits are still irreplaceable, and AI serves best as an assistive tool.
- The main bottleneck lies in finding the vulnerability, rather than exploiting it.
- Top researchers with a good intuition for where a bug might be are already faster and more effective than ever before
- If you are a beginner, reconsider your carrier path.
2⃣ Security AI Agent Builders
- Using different tools and frameworks for the same base models drastically changes the agent's final results.
- Focus on multi-stage audits and narrowing down the search space.
- Build specialized tools.
- Remember that one update can instantly make your product worthless.
3⃣ Developers
- The time window to react and deploy a patch after vulnerable code is published is shrinking drastically.
- The better your test suites are, the more effective the AI-suggested patches will be, reducing the chance of errors.
- The risk of exploitation increases regardless of your exposure, as the time barrier required for an attacker to understand the project no longer exists.
- This is the moment when saving time and money on development should be spent on security (both internal security practices and external providers services).
English
Composable Security ⛓️💥 รีทวีตแล้ว

AI Agent Security WILL be one of the top and fastest-growing security branches. Currently, we're experiencing isolated fails from those focused on usability, but soon this will lead to multimillion-dollar losses.
If you're building an AI Agent (or know someone who might benefit - tag them in the comment) and would like to ensure its security, we'd be happy to take such a project within @Composable_Sec as part of our research program, free of charge.
Spots are very limited, DMs open.
English

Off-chain audits shouldn’t start with a checklist.
They start with a story:
- how your bridge talks to your L2?
- how your oracle gets its data?
- where keys live?
- what happens when something fails?
We map the attacker’s path through that story, hit the riskiest links first, and help ship prioritized fixes.
✅Benefit: shorter audit, clearer priorities, improved security.
English

We are pleased to announce @znd | @zondacrypto decided to cooperate with us to secure the @TMPLtoken
The $TMPL is the world's first national Olympic Committee token, developed in partnership with @pkolpl 🇵🇱.
It is a utility token created on the Ethereum blockchain using the ERC-20. In addition to the standard functionality, TMPL includes a vesting and claiming system that automatically releases tokens over time to specific wallets, based on predefined rules.
Such an initiative requires the highest security standards. We are committed to working closely with them to ensure that the audit not only detects vulnerabilities but also enhances overall security.

English

* . * . * .
. * . * . * . *
+---------------------------------------------------------+
| Composable Security |
| 22222222 0000000 22222222 6666666 |
| 22 22 00 00 22 22 66 |
| 22 00 00 22 66 |
| 22222 00 00 22222 6666666 |
| 22 00 00 22 66 66 |
| 22 00 00. 22 66 66 |
| 22222222 0000000 22222222 666666 |
| |
| Security that strengthens what you build in 2026. |
+---------------------------------------------------------+
. * . * . * . *
* . * . * . *
Español
Composable Security ⛓️💥 รีทวีตแล้ว

Many assume that as security auditors, our role is strictly limited to finding bugs and criticizing code. In reality, we see ourselves as long-term partners in our clients' growth.
Being a specialized team allows us to prioritize deep collaboration. We don’t just look for vulnerabilities; we look for every possible way to help our clients succeed.
Recently during @EFDevcon, that meant playing "matchmaker."
I introduced a client to another project in my network where I saw a clear opportunity for mutual growth. The connection was a perfect fit!
As auditors, we sit at a unique crossroads with extensive networks and deep insight into the ecosystem. We love leveraging these connections to create value beyond the codebase. When our clients win, we win.
Never hesitate to reach out - we’re in this for the long haul.

English
Composable Security ⛓️💥 รีทวีตแล้ว

1/ The most underrated line from recent @samczsun piece:
“protocols have the legal authority to spend dollars out of their own treasury but no legal authority to spend dollars that users have deposited.”
English
Composable Security ⛓️💥 รีทวีตแล้ว
We are excited to share that our third audit with @Composable_Sec is underway!
Our newest smart contracts introduce automated yield strategies, debt swapping, collateral swapping, and more to continue to improve user convenience - allowing users to earn more and enjoy a simplified lending experience. We look forward to completing the audit and bringing these features to life!

English
Composable Security ⛓️💥 รีทวีตแล้ว
Composable Security ⛓️💥 รีทวีตแล้ว

Hard to disagree with @mattaereal; public/open goods are undervalued, leading to builder burnout as written in latest @theredguild article
Imagine incident response without @_SEAL_Org, static analysis without slither from @trailofbits, or learning security basics without @PatrickAlphaC videos.
When @drdr_zz and I were creating SCSVS, many people were eager to use it, treating it as a checklist or reference. Many things were created on top of it. However, few people actively contributed.
This is partly due to the lack of desire to build someone's brand (which is understandable), but it is not the only reason, as we see in many joint and non-branded initiatives that also have similar struggles.
Without the support of sponsors or super high motivation, it's difficult to actively develop such projects.
With the New Year slowly approaching, why not make a change?
One project that deserves way more attention is Security Frameworks. It offers quick, actionable insights across a massive range of security topics.
The sad part? When I send it to clients, most are hearing about it for the first time.
Reply below with an underrated initiative, project, or tool that you think needs more eyes on it. 👇
English
Composable Security ⛓️💥 รีทวีตแล้ว

Composable Security ⛓️💥 รีทวีตแล้ว

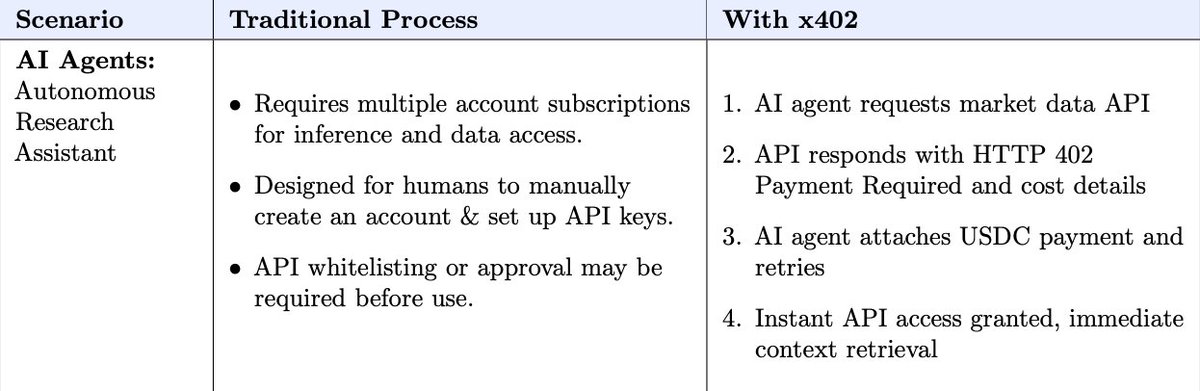
I'm going through the x402 white paper, and some of the things presented as advantages seem to be disadvantages or serious security holes.
Let's take this example:
Traditional process: API whitelisting or approval may be required before use.
VS
x402: AI agent attaches USDC payments and retries, instant API access.
If there's no whitelisting or validation, your agent could communicate with an API that will consume all your funds. Since it's not done on this layer, you'll have to remember to do it on another one.
Very interesting topic, I'd be happy to dig deeper and put together an article.
English

🔖NEW ARTICLE
Our team has developed a robust and multi-faceted approach to safeguarding the industry’s largest projects.
A prime example of this is our now long term partnership with @LidoFinance , where we conducted multiple in-depth security reviews of their Oracle – a critical component for the platform’s integrity and user trust.
🔗composable-security.com/blog/secure-bi…

English
Composable Security ⛓️💥 รีทวีตแล้ว

Yesterday was a crazy day. The @Balancer hack shook the entire community. Many analyses emerged, but unfortunately, some missed the point of what's most important at a time like this and why such analyses are being done.
User safety and helping projects should ALWAYS be our first priority. As usual, @SEAL led the way, but we know that many other good people also abandoned their current tasks to analyze fixes and consult on strategies with affected teams.
Analyzing the root cause of a hack shouldn't be about gaining as many followers as possible because you were the first to write about it. The point is to share information responsibly. Firstly, to limit losses, and secondly, to prevent these kinds of vectors in the future.
Was it a re-entrancy ?
No, there was no a callback and no user data specified in the swap data.
Was it an access control issue?
No, the attacker was executing operations on his behalf.
The root cause was that ...
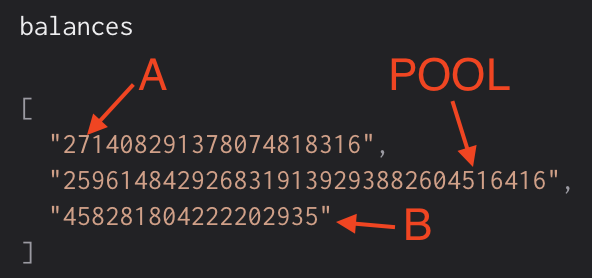
1️⃣ The attacker used a pool with 3 tokens: A, B and the POOL token itself.
2️⃣ Swapped a lot of POOL token for a lot of A and B: transfer in POOL and transfer out A and B. The balances of A and B are *small*, while balance of POOL is *huge* (see the balances picture).
3️⃣ Make swaps back from A and B to POOL. All swaps are "exact amount out" swaps and the "amount in" is calculated. However, the swaps from A/B to POOL drop the POOL token from balances when calculating amount in.
🚨 The effect: to get a big amount of POOL (to return the pool back to the initial state) the attacker needs to transfer in a small amount of A/B, because the amount is calculated based on small amounts of A and B only (POOL is excluded from the calculation).
As you can see, it was not a trivial attack, and removing this vulnerability is not easy either. The straightforward recommendation would be not to exclude POOL token from the invariant, but I bet there was business logic reason for that.
Final thoughts:
➡️ Multi token pools are tricky. Especially those that have its own token in it.
➡️ Any changes to invariants calculations are super important to check carefully.
Inflating and resulting balances (point 1):
Attack (point 3):


English
Composable Security ⛓️💥 รีทวีตแล้ว

Bera core update:
The binary for the hard fork has been circulated and many of the validators have upgraded. Prior to going live and producing blocks once again, we'd like to ensure that core infrastructure partners necessary for chain operations (oracles for liquidations etc) have updated their RPCs, so at this point they will be our main blocker to resuming liveness.
Following the RPCs for core services, we'll look to coordinate with bridges, CEX partners, custodians etc to restore service.
We're also in conversation with the current holder of the BEX funds, a MEV bot operator who has been live on Berachain for a few months. He has indicated that he is a white hat, and is willing to pre-sign a set of transactions to transfer the funds back upon the chain going live.
In accordance to our communications with the whitehat, we're confirming that funds should be returned to 0xD276D30592bE512a418f2448e23f9E7F372b32A2, the Berachain deployer address. The deployer address has also sent messages onchain to indicate that this procedure is to be followed.
etherscan.io/tx/0xcfb45fa2f…
etherscan.io/tx/0x4de28b39a…
Once the chain is live again, we will also provide a rundown of the various safety measures implemented across the BEX, other core apps, and Berachain as a whole. The team will also provide further information on future facing plans for BEX and any other expected second order effects from the last 24 hours.
Thanks in advance once again for all of your support and understanding as we work to recover funds and maximize user safety.
Berachain
English
Composable Security ⛓️💥 รีทวีตแล้ว

Today, around 7:48 AM UTC, an exploit affected Balancer V2 Composable Stable Pools.
Our team is working with leading security researchers to understand the issue and will share additional findings and a full post-mortem as soon as possible.
Because these pools have been live onchain for several years, many were outside the pause window. Any pools that could be paused have been paused and are now in recovery mode.
All other Balancer pools are unaffected. This issue is isolated to V2 Composable Stable Pools and does not impact Balancer V3 or other Balancer pools.
Balancer is committed to operational security, has undergone extensive auditing by top firms, and had bug bounties running for a long time to incentivize independent auditors. We are working closely with our security and legal teams to ensure user safety and are conducting a swift & thorough investigation. We’re grateful to our partners and the broader DeFi community for their support.
Security notice: Fraudulent messages claiming to be from the Balancer Security Team are circulating. These are not from us. Do not interact with unsolicited communications or click unknown links.
Official updates will be posted only via:
- This official Balancer account on X (Twitter)
- Our official Discord server
Be careful with communications from other sources, they can be fraudulent.
We will provide a comprehensive update with more details as our investigation progresses.
The Balancer Team.

English

We are pleased to announce that we will be auditing @arkivnetwork that originated within the @golemproject ecosystem.
Arkiv provides a database with Web3 guarantees. It merges the usability of Web2 (easy querying) with the trustlessness and permissionlessness of Web3.
Built on 3 layers:
L1 - Ethereum - security and finality
L2 - Arkiv Chain - coordination & anchoring
L3 - DB-Chains - custom, data-centric blockchains
We have been entrusted with an important first audit of the (L2 <> L3) bridging architecture. The team made modifications to the OP bridge contracts and to op-geth. These changes will be the primary focus of our review. All other components are treated as out-of-the-box, leveraging proven modules that they trust.
We are committed to working closely with them to ensure that the audit not only detects vulnerabilities but also enhances overall security.

English




